Fake factory lures in cyber attackers
- January 21, 2020
- Posted by:
- Category: Archer News

If you asked the small boutique company MeTech to fill your order, you’d be in trouble.
Need a prototype made? MeTech would leave you hanging.
Unless you are a malicious hacker.
Watch here:
The Mission
MeTech is a fake company, created for one purpose — to see how cyber attackers would try to mess with an industrial company and industrial control systems.
It’s a honeypot, a lure. But it took on a life on its own.
“After weeks of discussing the company among ourselves, we started to feel it was real,” said researchers from Trend Micro, who presented their findings last month at the S4 industrial cybersecurity conference in Miami.
The Company
They decided to pose as an industrial prototyping company with a focus on automotive, military, aerospace and manufacturing customers.
The researchers created a website with their own MeTech motto and logo, adding photos of real-looking fake people created by artificial intelligence — a programmer, maker, engineer and more.
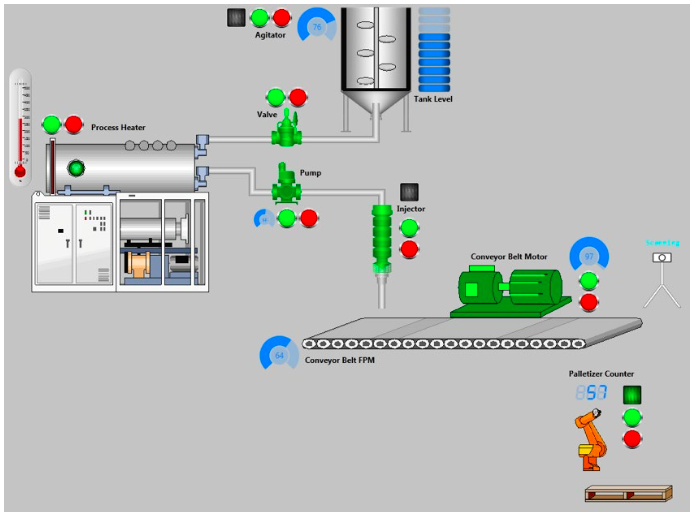
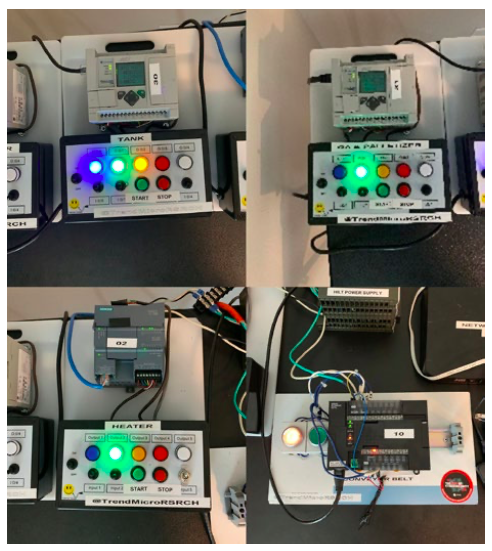
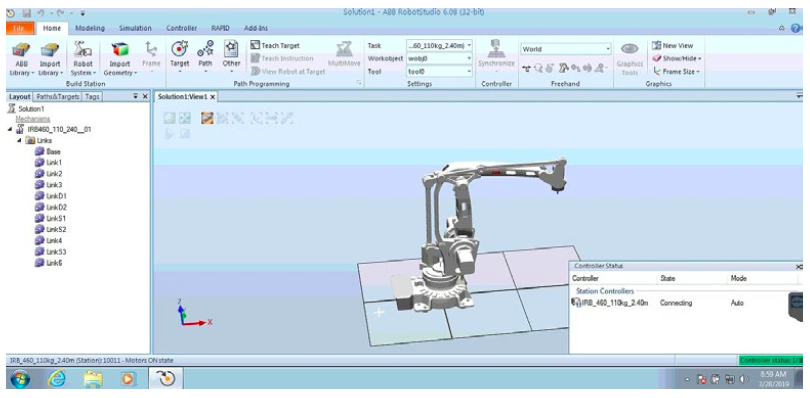
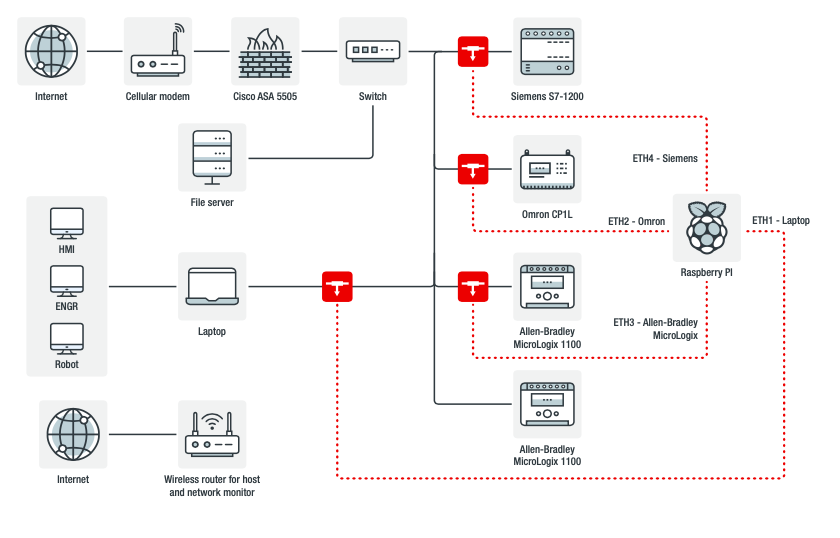
Their “factory” was a computer system with virtual industrial robots, conveyor belt, palletizer, process-heater, pump and injector, plus real programmable logic controllers, or PLCs, to back them up.
“Embracing the idea, vision, and brand of our faux company was very important because we had to depict a realistic company image while reducing room for mistakes, such as leaking details about our real affiliation,” they said.
The Lures
You may hear stories of other honeypot systems attacked within minutes of setup, but MeTech required a little extra help.
“The approach we took was to stage leaking information, to put us in such a position that attackers might find our honeypot interesting enough to play around in and eventually attack,” the researchers said.
How do you that with an industrial system?
—Opening certain ports that would allow attackers in.
—Misconfiguring a remote administration tool, the VNC or virtual network computing, so that outsiders could access the robotics workstation.
—Uploading sensitive company information to an antivirus aggregation service, as if they had been hit by malware.
—Exposing the an industrial control screen, the human machine interface or HMI, to the Internet.
—Posting about some of these issues on Pastebin, a website for sharing information.
A month after MeTech launched in May 2019, attackers started their sieges.
The Attacks
For malicious hackers, the honeypot proved sweet.
They invaded MeTech’s factory to launch ransomware, fake ransomware, crypto mining, financial fraud — and in some cases took remote control of industrial machines .
A researcher even reported the factory’s issues to the Industrial Control Systems Cyber Emergency Response Team, or ICS-CERT.
“This is the right course of action should what was happening to our honeypot happen to a real system,” the researchers said, adding that they contacted the investigator, Dan Tentler, to avoid having others waste time on a faux system.
Messing with Industrial Machines
In August, the industrial system caught the eye of an attacker who performed a “system shutdown,” according to Trend Micro’s report.
“A threat actor goes into the system and clicks around the robotics application and closes the HMI [human machine interface] application, before eventually powering the system down,” the researchers said.
In December, an attacker staged a three-day invasion, starting the factory system, stopping the conveyor belt, starting up the palletizer, and eventually shutting the factory down and locking the screen.
For a real factory, this could cause havoc and/or burn time and money.
“Our findings should serve as cautionary examples for organizations who run similar systems,” the researchers said in their conclusion.
Money from MeTech
Some attackers wanted money more than control of machines.
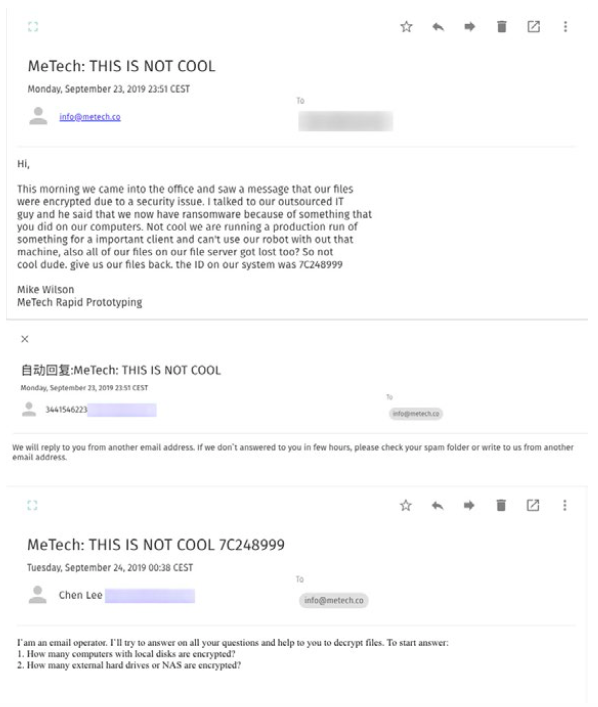
Two hijackers launched ransomware on MeTech computers, encrypting files and demanding ransom — one asking for $10,000 in cryptocoins to free the files.
MeTech responded as if they were real and very frustrated employees, asking for proof that their files could be decrypted and negotiating the ransom down to $6,000.
Of course, the researchers never paid.
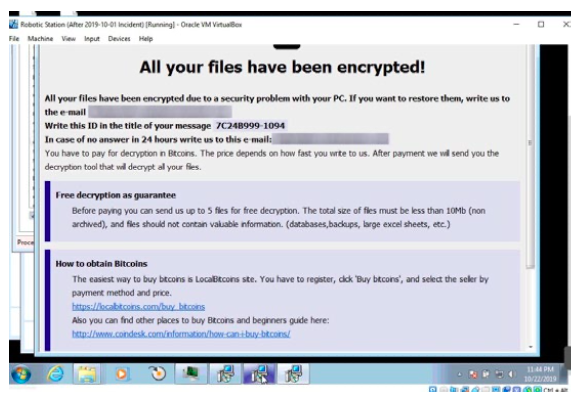
Another sneaky cyberspace invader tried to trick MeTech into thinking its files were encrypted by renaming files with new extensions.
The fraudster asked for $750 to “decrypt” the files.
When no one responded to the false ransomware demands, the hacker returned and tried to get more attention by opening porn.
But the fake ransomware attack on the fake company yielded no fruit.
Researchers just reset the system and moved on.
Making Money Off of MeTech
If MeTech employees had not monitored their network, they might have missed other abuse.
Cyber criminals installed a remote access tool onto factory computers, using MeTech machines and energy to mine their own digital coinage.
The crypto miners earned but a pittance, according to researchers.
“However, if this was going on with many other machines around the world, the threat actor behind it could cash in on the attack well,” they said.
The attackers returned twice, at one point actually fixing the miner, according to the report.
Other crooks also tried to use MeTech’s system for their own gain.
“We observed that third-party actors had used the resources in the honeypot to engage in and obscure possibly abusive and inappropriate activities, such as buying smartphones by upgrading mobile subscriber accounts and cashing out airline miles for gift cards,” the report said.
Protecting Real Companies
During its short life, from May through December 2019, MeTech did not pride itself on stellar cybersecurity.
Quite the opposite.
“For our honeypot to garner this kind of attention, we practically had to do everything wrong when it came to our faux company’s general security stance,” the researchers concluded. “However, for many small businesses with no IT or security staff, such a situation is not uncommon.”
Don’t do what they did, the researchers urged.
Instead, make sure your equipment and industrial control system components are not exposed online, unlike MeTech and its misconfigurations.
“Ultimately, weak security not only makes cyberattacks possible, but can also serve as additional invitation for attacks on industrial systems that have long stoked the interest of cybercriminals,” the report said.
Main image: Robots at a fake factory. Image: Fotomek/iStock
