What is a honeypot?
- May 16, 2019
- Posted by:
- Categories: Archer News, Ask Archer, Cyberattack, Hacking, Industrial Control System Security

We’re answering your security question, “What is a honeypot?”
It sounds sweet, but it’s actually a trap.
Here’s how it works.
Watch here:
Tempting Tub
Honeypots earned notoriety through the famous childhood story character Winnie the Pooh.
Looking for the last lick of honey, he sometimes got his head stuck inside the tempting tub of sweetness.
In the cyber world, honeypots are tempting, too.
You set up a virtual version of something, say, a security camera, then wait to see who tries to attack it and how.
Lightning Speed
Security company NetScout set up smart device honeypots and found it took less than five minutes for attackers to launch their digital assault.
Crooks take over these IoT — or Internet of Things — devices and rope them into their botnet armies, the company said in December.
Another company, Sophos, set up ten honeypot cloud servers across the globe.
Cyber crooks hit the first one in just 52 seconds, then pounded them with more than five million “relentless and continuous” attacks for the 30 days they were live, Sophos reported in April.
Serious Damage
Industrial cybersecurity researchers use honeypots, too, to find out more about the people trying to take over or destroy critical infrastructure.
MalCrawler set up honeypot power plants and substations, presenting its findings in 2015.
Researchers found that some hackers just wanted to steal info, while others wanted to cause a major outage — and even tripped the switches that would black out parts of cities had they been real.
Crime Online
Police use honeypots to go undercover online, taking over dark web sites and pretending to be drug dealers.
Dutch police secretly ran the criminal site Hansa and collected info on illegal activity until they shut it down and went after the perps in 2017.
Bad guys can use honeypots, too, making sites that look real, but steal your info, like your credit card number.

How to Protect Yourself
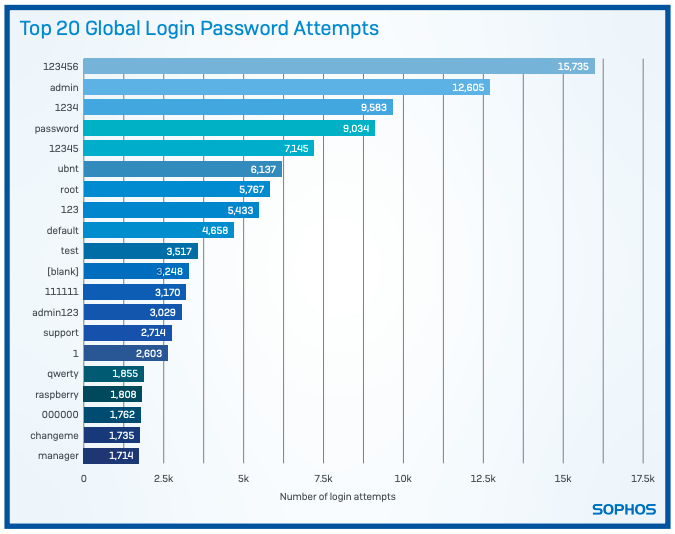
In many cases, the honeypots show that cyber crooks use bots or automated attacks,
checking every device to see if you changed the username and password or just left the easy-to-hack default ones on there.
If it’s the default credentials, the crooks get in, take over your device and use you to make money or assault even more people.
They can enslave your machine and use it to do DDoS, or distributed denial of service, attacks, like the one that took down Twitter, Amazon and Netflix in October, 2016.
Learn from the honeypots — and Winnie the Pooh — change the default password that comes on your devices, so you don’t get stuck.
Use a password manager to help you keep track of all the long and complex passwords you create for yourself, so you don’t reuse passwords or create simple ones that are easy to guess.
Take it Further
Some people think of their IoT devices, like their IP cameras and cable modems, and “set and forget” devices, according to NetScout.
But they can have security vulnerabilities, and unless you update them, you can also be vulnerable to attacks, honeypot research shows.
Also, some devices sit on store or warehouse shelves for a while.
That gives researcher and attackers time to find security holes.
So, your device may be insecure — and need updates — as soon as you open the box.
Also, turn off Universal Plug and Play (UPnP) on your home router, Sophos advises, as it has a security issue that can put you at risk.
See more answers from Archer News:
What is EKANS and what does it want from you?
What is SIS? Your life could depend on it
The top 4 things you need to do with your home router
Main image: Teddy bear staring at honey on a computer screen. Image: David Bicker
