“What is an HMI — and why do attackers like them?”
- September 12, 2019
- Posted by:
- Categories: Archer News, Cyber Crime, Cyber Crime, Cyberattack, Hacking, Industrial Control System Security, Posts with image, Power Grid, Power Grid

You probably use an HMI regularly.
It stands for “human machine interface.”
But HMIs also make good targets for attackers.
Watch here:
Your Daily HMI
You rub elbows — or fingers — with an HMI when you use things like the ATM and the gas pump.
With an ATM, for example, you’re the human, the cash dispenser is the machine and the interface is the computer that lets you control it — in a very controlled way.
Attackers like HMIs. If they can crack them, they can get free gas or turn an ATM into a jackpot.
Big Machines
This can also work on a much larger scale.
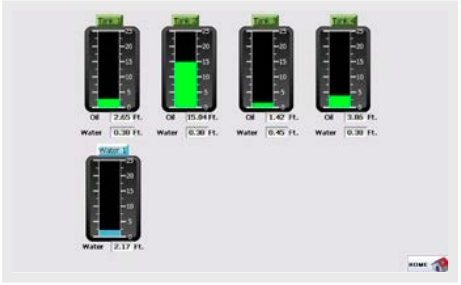
Workers use HMIs to run giant robots and other industrial machines in factories and power plants. But even industrial HMIs are hackable.
The U.S. Cybersecurity and Infrastructure Security Agency says HMI screens show attackers a lot of helpful info about which machines to attack.
If cyber invaders take over the screen, they can trick the real operator into thinking something is happening when it’s not. And they can actually run the machine themselves.
In one famous example, attackers took over part of the power system in Ukraine in December 2015.
Operators saw the HMI cursors moving by themselves and were powerless to stop them, as seen in this video.
Attackers had taken control and shut off the lights for several hours in the dead of winter.
Hacker Machine Interface
How easy is it to attack HMIs?
A Trend Micro study in 2017 found that developers sometimes make basic security errors for HMI software, leaving them vulnerable.
That means companies need to make sure HMIs are protected.
More Trend Micro research last year showed that some companies were still not protecting their HMIs, from oil and gas plants in the U.S. to water companies in Europe and beyond.
HMI Hack
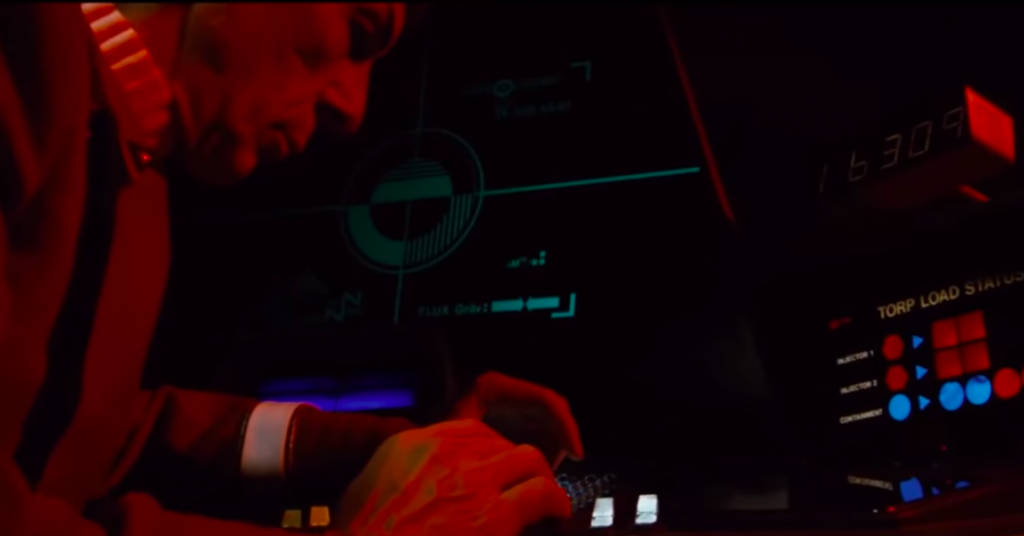
You can see an HMI hack in action in Star Trek II: The Wrath of Khan.
Khan takes over a federation ship, the Reliant, and attacks the Enterprise.
Spock remembers the passcode for the Reliant’s control system, or HMI.
“Reliant’s prefix number is 1-6-3-0-9,” he informs Captain Kirk. “Each ship has its own combination code.”
“Using our console to order Reliant to lower its shields,” Kirk says.
“Assuming he hasn’t changed the combination,” Spock adds. “He’s quite intelligent.”
HMI Insecurity
But Khan forgot.
Spock enters the code and the Enterprise can control Khan’s ship from the bridge.
“Sir, our shields are dropping,” the console operator cries.
“Raise them!” insists Khan.
“I can’t!” the operator replies.
And the Enterprise fires.
Protect Yourself
Don’t be like Khan.
If you own or operate HMIs, take steps to protect them.
—Change the default passcode or password.
—Keep them separate from the Internet and the corporate network.
—Update or patch them regularly. They’re often running 24 hours a day, so patching can be difficult, but is still recommended.
And if you use an HMI on the street or on the job, it’s not a bad idea to keep watch for anything out of the ordinary happening on the screen.
Thanks again to cybersecurity expert Mike Toecker for his Star Trek example of an HMI hack.
He says he’s seen a case where a company used an HMI passcode of just “911” — far too short and too easy for attackers to guess and break in.
See more answers from Archer News:
Main image: Lego ATM and line. Image: LewisTsePuiLung
