Hydro cyberattack: “The bastards made my job so much more difficult”
- March 22, 2019
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Industrial Control System Security, Posts with image, Power Grid, Ransomware
Stress. Worry. Frustration.
Some workers at Hydro aluminum plants are gnashing their teeth after the big cyberattack that shut down some operations this week.
“The bastards made my job so much more difficult,” said a man writing as a plant worker on YouTube.
“We ran for a shift and wrote everything down, but the quality failed on some stuff and shipping didn’t know where to send anything so they stopped,” he added.
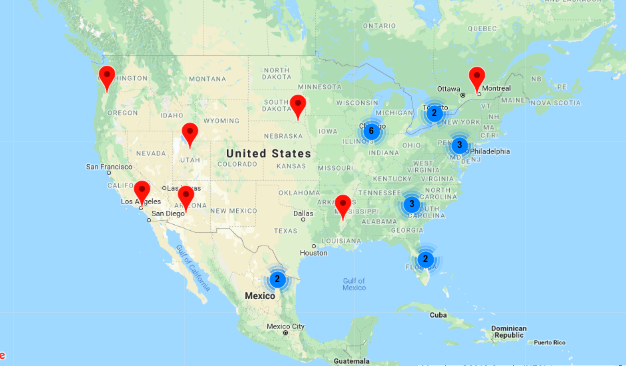
If you worked at one of the 23 Hydro facilities in the U.S. or if you were one of the 35,000 Hydro employees around the world, you might be frustrated, too.
Your bosses would tell you not to turn on your computer or connect any devices.
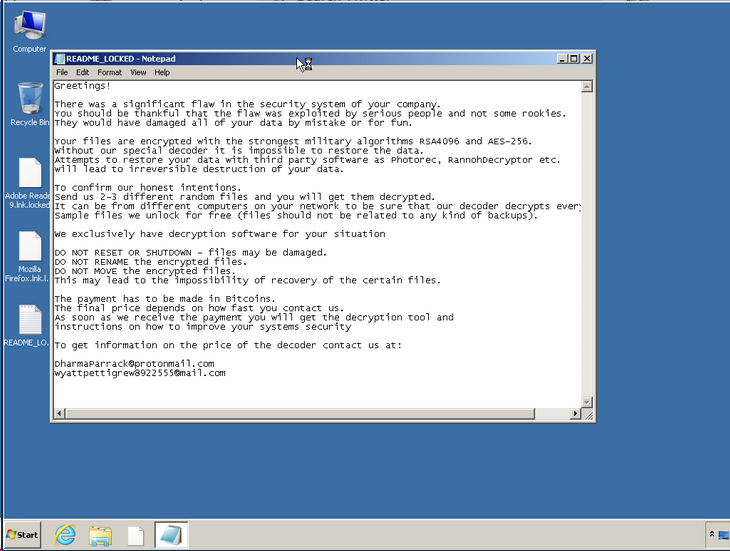
If you did, all you might see is a ransom note, according to security researcher Kevin Beaumont.
The attacker changed your password and scrambled, or encrypted, your files.
You have to pay Bitcoin to get them back.
“The final price depends on how fast you contact us,” the message reads.
How it Works
Some ransomware comes in by email. An employee clicks on a link and attackers can hold the entire company hostage.
Some ransomware can spread itself from network to network, like the WannaCry and NotPetya attacks that shut down hospitals and companies around the world in 2017.
But the ransomware that hit Hydro, called LockerGoga, is different.

The attackers probably used stolen passwords to get remote access to Hydro’s network, getting access to a tool called Active Directory that would let them put malware on every computer on the system, Beaumont said.
“Immediately, every single laptop, desktop and server connected to Active Directory will trigger the malicious software,” he said.
But LockerGoga stops there.
Instead of jumping from computer to computer, from company to company, like other attacks, it roosts until Hydro can get rid of it.
What Does This Mean?
This could mean a different kind of attacker is behind this cyber offensive.
“It’s not a very efficient sort of attack,” said Joe Slowik, adversary hunter at Dragos. “It doesn’t seem to be a very effective way to make money.”
Other attackers might want to get as much money as possible with as little work as possible, using ransomware that would spread to many victims.
“If you’re looking at this from a criminal mindset, that I want to maximize my payoff while minimizing my effort, it’s not terribly useful and sophisticated from that standpoint,” Slowik told Archer News.
The LockerGoga attackers may be targeting the Norway-based Hydro, as they appeared to do with French engineering company Altran in January, some theorize.
“It just smells as though there should be something more to this event than just a simple, fly-by-night, opportunistic ransomware infection. But having said that, that’s just all speculation,” Slowik said.
Some researchers believe the massive 2017 NotPetya cyber attack masqueraded as ransomware, but its true goal was to destroy data.
Protect Yourself
The Hydro ransomware may not spread to your computer or company during this attack, but experts recommend you take steps to protect yourself.
“This is not some kind of an epidemic,” security expert Mark Heard, formerly of Mandiant, said to Archer News. “But rather if you’ve been putting off doing updates or you’re putting off those security projects and such, you might want to reevaluate those based on a demonstrated increase of a threat.”
Investigators are analyzing the malware to learn more about how it works and how it did its damage.
If analysis shows the attackers did indeed use the Active Directory system, you will want to take steps to protect yours, advised Slowik.
Beaumont has more recommendations in his post, but he also recommends backing up all of your data and protecting the backups so they can’t be encrypted, too.
His final advice:
“Do not pay the ransom. Do not pay the ransom. Do not pay the ransom.”

Frustration
Beaumont expressed frustration that the LockerGoga attack on Altran two months ago did not lead to better security.
Security tools that work to to detect ransomware did not detect LockerGaga, he said.
“The reality here is we had an in-the-wild, classic ransomware attack around for months and there wasn’t anywhere approaching good detection,” Beaumont wrote. “There is a serious lack of open information sharing after ransomware incidents which involve unusual code.”
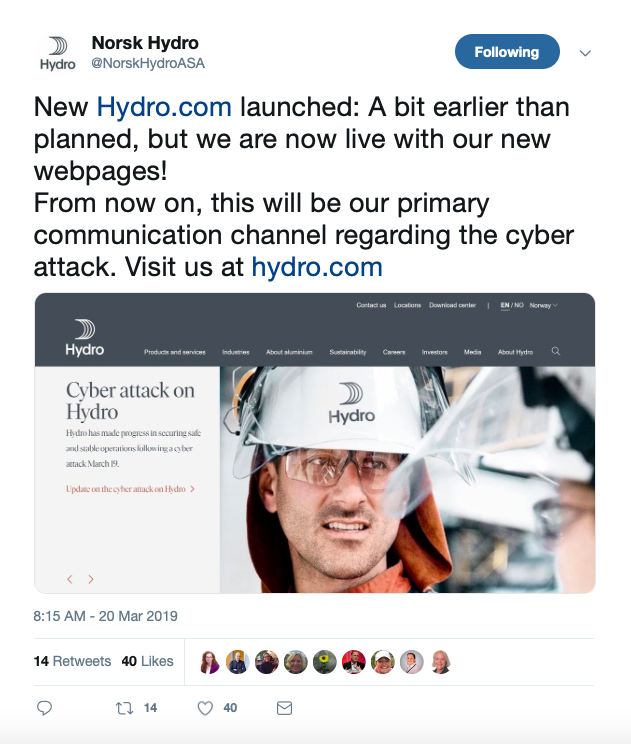
Meanwhile, Hydro announced it is making progress on fixing its systems, restoring its data from backups, and bringing its plants back to full production.
It is one of the world’s largest aluminum producers, and produces electric power as well.
“The root cause of the problems has been detected, a cure has been identified,” the company said in a statement today on its now-functioning website. “Hydro’s experts are working on reverting virus infected systems back to a pre-infected state.”
The company said some operations are still running at half-capacity, and it does not know how long it will take to recover.
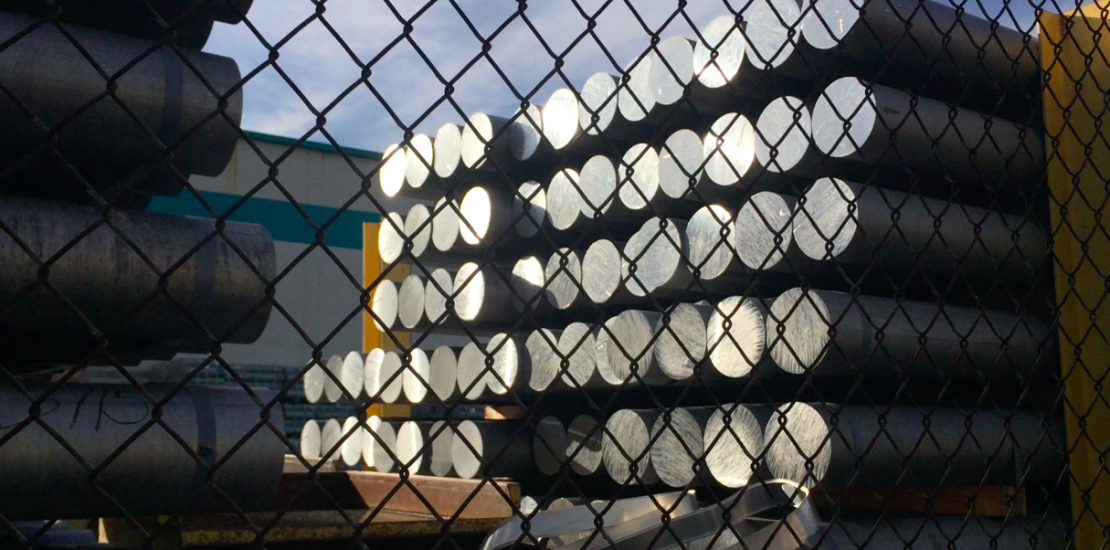
Main image: The Portland, Oregon, Hydro aluminum plant, which was impacted by the ransomware attack. Image: Archer News
