Surviving the new global ransomware attack
- June 28, 2017
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Health Care Security, Posts with image
A quick look at what you need to know.
You probably remember the news about WannaCry, a ransomware that hit the world in May and shut down hospitals and companies across the globe.
Now, a new global ransomware attack is on the move.
Some call it Petya. Some call it NotPetya.
“Wannacry – I am a ransomware to end all hyperbolic descriptions!” tweeted security researcher Bryan Campbell. “Petya/notpetya – hold my beer.”
Computers systems at two U.S. hospitals — and possibly more — went down, and the ransomware held big company hostage, like the drug company Merck and the company that owns Oreo and Nabisco, the Washington Post reported.
The malware hit Ukraine the hardest, said cybersecurity company Kaspersky Lab, with Russia next in line. Other countries are reporting attacks as well.
Ukraine’s Chernobyl nuclear plant fell victim, as did a Danish shipping company, the Post said.
“How long do you think it will last?” asked a Twitter user going by the name Velly. “My company just shut down.”
“This thing is bad,” replied user Jack Halon. “Expect it to last a few weeks.”
How does it work?
The attack reportedly started Tuesday morning in Ukraine.
The ransomware wormed its way in through an update for tax software, said cybersecurity researcher Kevin Beaumont.
Some people were hit with poisoned e-mails, said the Ukrainian cyber police.
“The second and most widespread way of distributing the present-day virus-extortion has been confirmed. These are phishing e-mails,” the agency said in a tweet.
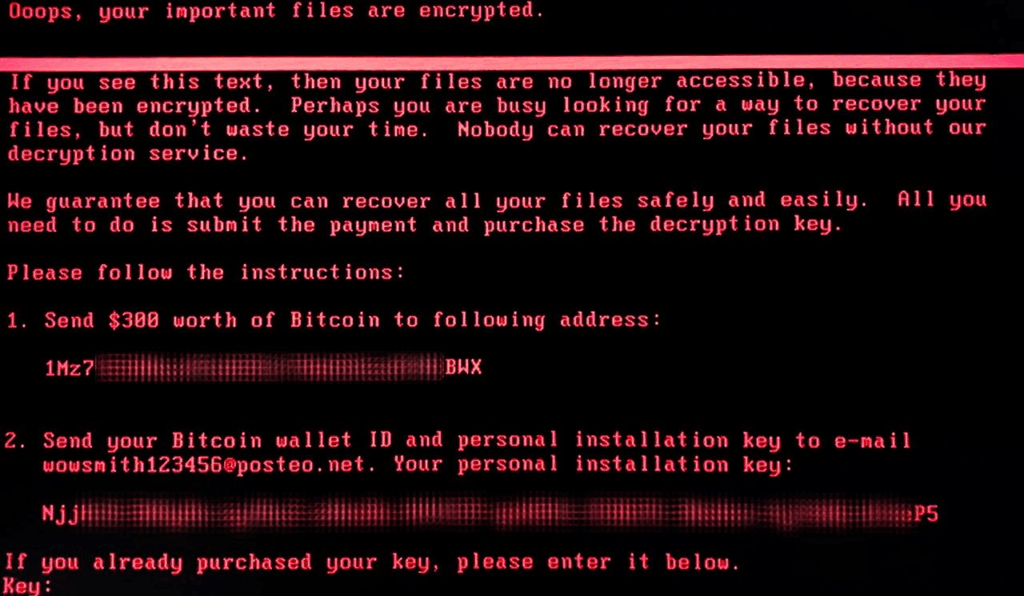
Ransomware in the Petya family will crash your computer, and when you reboot, you’ll get a red and black screen demanding money to get your computer back, said Rick Howard Palo Alto Networks.
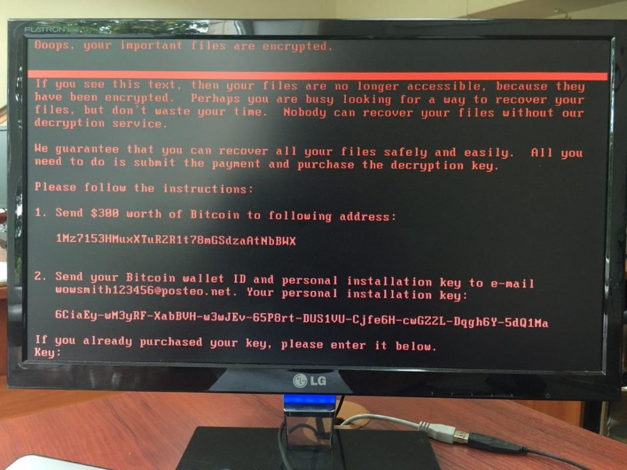
Petya ransom note. Image: Palo Alto Networks
In the current ransomware attack, you may need to pay up $300 in the digital currency bitcoin.
People have already started paying, according to Howard’s post.
However, some researchers, including Beaumont, have said the payments did not work.

Not again!
For some, this new attack is frustrating.
“This stuff is getting really old,” wrote a commenter on the Federal Trade Commission’s website. “Not being a IT [sic] I don’t understand why it can’t be stopped.”
Researchers say the new attack may be using the same security hole as the WannaCry attack in May.

WannaCry ransom note. Image credit: Avast
In that case, people and companies who did not update their computers left open a door for attackers to creep through.
“The WannaCry attacks in May 2017 demonstrated that many Windows systems had not been patched for this vulnerability,” said Howard.
“The spread of Petya using this vulnerability indicates that many organizations may still be vulnerable, despite the attention WannaCry received,” he added.
They may be vulnerable because they still have not updated their systems, even after the May ransomware crisis — or because someone else did not patch, and the infection spread.
Save yourself — and everyone else
Some cybersecurity experts are urging people and companies to take steps to protect themselves, because one vulnerable system can hurt others.
“On the heels of WannaCry, we yet again see the vulnerability of connected systems across the globe. Today’s attack hit critical infrastructure — finance, transportation, manufacturing and more,” said Michael Kaiser with the National Cyber Security Alliance in Washington, D.C.
“It is much more than an inconvenience,” he added. “We are more dependent than ever on the data stored across our computer systems. It is our shared responsibility to do our part in keeping devices secure. It all starts with basic cyber hygiene around software updates and locking down logins.”

The WannaCry ransomware attack in May affected hospitals in England.
What do you do?
First step — update!
“It’s crucial to keep operating systems and other software up to date,” said the FTC.
Next?
“Back up your files!” recommended the FTC, with a video for encouragement.
Also, do not click on attachments from untrusted sources, said Kaspersky Lab.
Companies should also segment their networks to protect from the new Petya, said Arbor Networks.
Here is more info for companies and organizations from the National Cyber Security Alliance:
—Keep clean machines: Prevent infections by updating critical software as soon as patches or new operating system versions are available. This includes mobile and other internet-connected devices.
—Lock down your login: Strong authentication — requiring more than a username and password to access accounts — should be deployed on critical networks to prevent access through stolen or hacked credentials.
—Conduct regular backups of systems: Systems can be restored in cases of ransomware and having current backup of all data speeds the recovery process.
—Make better passwords: In cases where passwords are still used, require long, strong and unique passwords to better harden accounts against intrusions.
—Check with your software vendors: In the wake of an attack of this nature, software vendors may issue patches or other solutions to eliminate specific vulnerabilities discovered during the attack. Implement those fixes as soon as possible.
Main image: Ransomware demand note. Image credit: Kaspersky Lab
