What you can learn from the Hydro ransomware attack
- March 20, 2019
- Posted by:
- Categories: Archer News, Cyber Crime, Industrial Control System Security, Posts with image, Power Grid, Ransomware

One of the world’s biggest aluminum producers, Norsk Hydro, just fell victim to a ransomware attack.
You can learn from the attack and protect yourself.
Watch here:
Ransomware Attack
Hydro runs plants around the world, producing aluminum and, in some cases, power.
But attackers hit the company starting Monday night around midnight in Norway, where Hydro has its headquarters.
The attack — ransomware, stealing computer data and holding it hostage for money, affecting 35,000 employees in 40 countries.
“Let me be clear. The situation for Norsk Hydro through this is quite severe,” said Hydro CFO Eivind Kallevik. “The entire worldwide network is down, affecting our production as well as our office operations. We are working hard to contain and solve this situation, and to ensure the safety and security of our employees.”
Security researcher Kevin Beaumont tweeted that the type of ransomware could be “LockerGoga” as reported by Norwegian media.
Reuters confirmed that Norsk Hydro had been exposed to LockerGoga.
Beaumont told the BBC that LockerGoga would likely have to be placed on the systems by hand, rather than through an email or remotely.
Started in the U.S.?
The ransomware first hit Hydro computers in the U.S., reported Ars Technica, though the report does not say which plant was affected.
There are 23 in all according to Hydro, from Oregon to Texas to Kentucky.
An employee at the Portland, Oregon, plant told Archer News that the plant was basically shut down on Tuesday and that workers could not access their computers.

Hydro plant in Portland, Oregon. Image: Archer News Network
The company has more facilities in countries like Brazil and Germany, and of course Norway.
Hydro says they isolated the computer systems at all of the plants to contain the cyberattack and some are running on manual instead of by computer.
The Hydro website was down today, as well as the company’s stock.
The attack will likely be very costly.
“Not Good News”
“Obviously, it’s not good news,” said control systems cybersecurity expert Mark Heard, formerly of security company Mandiant.
Cyber attackers know they can make money with ransomware, Heard said.
“I hate to say this this is the new normal, but it kind of is,” Heard said in an interview with Archer News.
“It’s an indication of what companies that have operations that are connected to the Internet will have to face and protect against,” he added.
Protect Yourself with Backups
The good news for Hydro — the company says it has back up files and plans to restore all the data from its backups.
“Have your backups. make sure you are backing up in more than one place,” said security expert James McQuiggan of Siemens.
McQuiggan said everyone should have backups, from companies like Hydro to people at home.
Use a hard drive and the cloud if possible, he suggested.
Protect and test your backups to make sure attackers can’t get to them, too.
“Make sure that they’re restoring properly,” McQuiggan told Archer News. “I’ve heard many, many times where companies will say, ‘Yep, we’re backing up, we’re doing the daily backups,’ and then when they have to restore they go, ’Oh, it’s been corrupted the last three months because they haven’t checked.’”
Update Your Systems
The entry point for this ransomware is not clear yet.
Two years ago, a ransomware called WannaCry hit computers around the world.
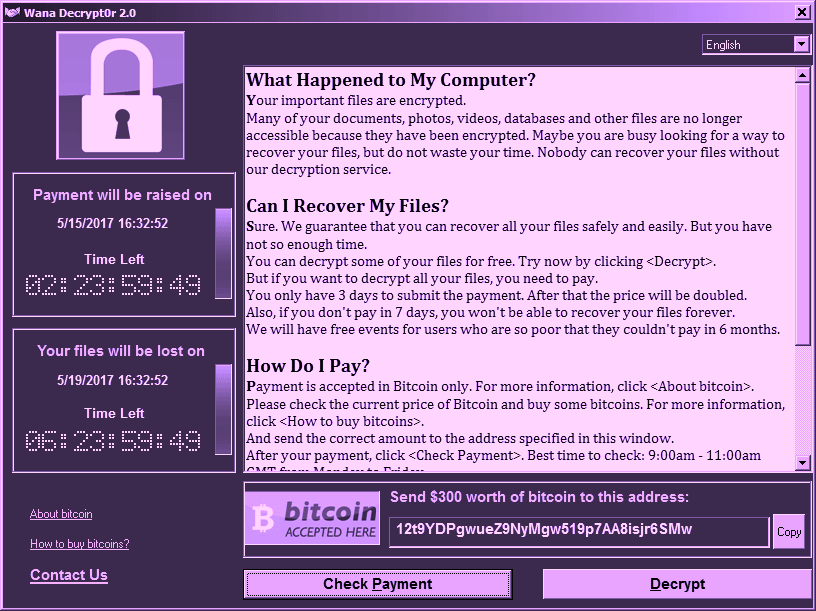
WannaCry ransom note. Image: Avast
Security experts recommended people and companies patch or update their systems.
Check here for help on patching for beginners.
Another cyber attack known as NotPetya also shut down companies in 2017.
Researchers first called it a ransomware attack, but later some said the ransom aspect was just a distraction and the real purpose was to destroy data.
After NotPetya, the National Cyber Security Alliance recommended that companies follow these steps:
—Keep clean machines: Prevent infections by updating critical software as soon as patches or new operating system versions are available. This includes mobile and other internet-connected devices.
—Lock down your login: Strong authentication — requiring more than a username and password to access accounts — should be deployed on critical networks to prevent access through stolen or hacked credentials.
—Conduct regular backups of systems: Systems can be restored in cases of ransomware and having current backup of all data speeds the recovery process.
—Make better passwords: In cases where passwords are still used, require long, strong and unique passwords to better harden accounts against intrusions.
—Check with your software vendors: In the wake of an attack of this nature, software vendors may issue patches or other solutions to eliminate specific vulnerabilities discovered during the attack. Implement those fixes as soon as possible.
Main image: Aluminum. Credit: PublicDomainPictures
