The Internet turned on itself in Friday’s big attack
- October 27, 2016
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Home Security, Posts with image, Smart Devices

When computers could not get through, they kept trying, adding to the massive Internet traffic jam.
You may have tried to get onto Twitter. Or Netflix. Or Amazon.
But when you gave up last Friday, October 21, during the massive cyber attack, your computer or phone may have kept going, trying again and again to reach your destination. And that made the attack even worse.
This kind of automatic “retry” activity increased traffic by ten to twenty times normal, said Internet service company Dyn, the target of the attack, in a post Wednesday.
Add that to the attack itself—a bombardment from 100,000 zombie computers and devices, according to Dyn—and it’s hard to keep your head above water.
“We saw both attack and legitimate traffic coming from millions of IPs [Internet Protocol addresses] across all geographies,” said Scott Hilton with Dyn.
Ultimately, the system could not keep up, and people could not access some of the big-name sites that live online, from Reddit to PayPal to Spotify.

Twitter users—if able—spread the word about the big cyber attack on Friday.
Can it be fixed?
Dyn is investigating, analyzing and fixing weak spots, according to the company.
“We very quickly put protective measures in place during the attack, and we are extending and scaling those measures aggressively,” Hilton said.
There is also a criminal investigation underway into this “complex and sophisticated” attack, the post said.
But the company can’t fix the cause of the attack—the mammoth army of slave computers and devices that attackers use to blitz their targets.
In this case, Dyn said, it was indeed a botnet—a network of infected or ‘bot’ devices—called Mirai that was used for the DDoS, or distributed denial of service, attack.
The October 21 attack did not appear to affect Facebook.
Stopping the bots
One of your devices could even be part of the botnet—one of the home routers, security cameras, and other connected devices that attackers turned into online weapons.
“Weak default passwords that don’t get changed, vendor backdoors [ways a manufacturer can get into your device after you have bought it], and installing things on already compromised networks make these attractive targets,” said Slade Griffin with Contextual Security.
Cybersecurity company ESET recently tested 12,000 home routers and found 15% of them are unsecured, most with weak passwords and the username “admin,” easy for attackers to crack.

ESET research found that 15% of 12,000 home routers studied had weak security. Researchers did not specify if one make or model was more insecure than another. Photo credit: mightyohm via Foter.com / CC BY-SA
Reset
You may be able to reset the username and password on your Internet of Things—or connected—devices, like your baby monitors, thermostats and wireless security systems.
Others may not have a fix.
“Even if they wanted to do something, they couldn’t, because there’s no way for users to configure the default settings and default credentials,” said Rob Morton, director of public relations with Akamai Technologies.
“It’s not an Internet of Things,” he added. “It’s an Internet of Unpatchable Things.”
Who’s responsible?
Some experts say the companies making the connected devices need to make them more secure.
“Hopefully, the manufacturers and others will step up and say, ‘Hey, we are doing something about this,’” Morton told Archer News. “‘We’re going to change the software so it prompts the user to change their default credentials and allows them to be done when they first plug that device into the network.’”
One company is recalling 10,000 security cameras after Friday’s attack, according to Reuters.
China-based Hangzhou Xiongmai said it will recall several batches of home surveillance cameras made in 2014, after researchers showed the company’s cameras had been attack targets, Reuters reported.
You can ask your device maker for more secure devices, Morton said, as opposed to waiting until you’re the victim of a more severe attack.
“There’s a ton of value in asking for it now,” Morton said. “Consumer demand would be huge for these device manufacturers to rethink security and relook at how to better offer a more secure device.”
“And maybe, maybe, we will see that there is a groundswell in consumer opinion following this and potentially other large attacks,” said Morton.
Defending the Internet
The Department of Homeland Security said it has talked with 18 major communications service providers about the attacks and is in the process of creating a set of strategic principles for securing devices, according to Reuters.
In addition, a member of the U.S. Senate Intelligence Committee sent letters to the Department of Homeland Security, the Federal Communications Commission and the Federal Trade Commission this week, asking the agencies what kind of abilities they have to help fight off DDoS attacks.
“DDoS attacks can be powerful tools for censorship, criminal extortion, or nation-state aggression,” Senator Mark Warner (D-Virginia) wrote in his letter to the FCC.
He asked if, for example, Internet service providers could declare a person’s device as insecure and refuse to connect it to the Internet.
That could mean that if your router or camera become infected, you would no longer be able to use it online.
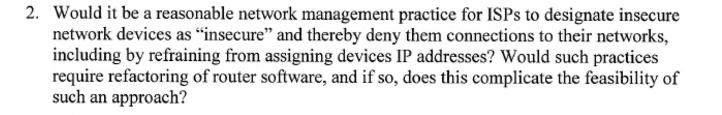
Part of Sen. Mark Warner’s letter to the FCC after the October 21 attack.
Who did it?
Though Senator Warner’s letter mentioned nation-state aggression, national security experts do not think a foreign country is behind Friday’s attack.
So far, no one appears to have claimed credit.
It can be difficult to figure out the attacker’s identity if no one steps forward, according to Morton.
“There’s been no one taking claim,” he said.
At this point, it does not appear to be the work of hacktivists or extortionists, he added.
“None of the traditional reasons why people go after a DDoS,” Morton said. “I don’t know what the odds are in finding out who did it.”
Facebook users joked about who was responsible for the October 21 attack.
More attacks
Experts see more barrages like Friday’s event coming soon.
“Without a doubt,” Griffin said.
“We will have some copycat attacks and as more and more devices become interconnected and the attack surface continues to grow,” he said.
“Attacks are going to get bigger,” Morton said.
The size of DDoS attacks has already increased dramatically.
“Used to be five to 10 gigabits [5,000,000,000 to 10,000,000,000 bits] per second was a big attack,” Morton explained. “Then it was 30 to 40. Then it was 100. Now we’re in the 300 to 600 range.”
There have been some reports that Friday’s attack reached a magnitude of 1.2 terabits [1,200,000,000,000 bits] per second, but Dyn said it has not been able to confirm that number.
“Eventually, we’ll learn that not everything belongs on the Internet,” Griffin said.
