“Which operating system is secure on a computer?”
- July 3, 2018
- Posted by:
- Categories: Archer News, Ask Archer, Cyber Crime, Hacking, Posts with image
You ask security questions, we answer!
In our “Ask Archer” show live on Facebook, viewer Andrék asked, ““What operating system do you consider secure in a computer?”
See answer here:
We turn to Archer’s Patrick C. Miller for his response.
“Any operating system that you use is only as secure as you make it,” Miller said.
But there is good news.
“There are ways to make every single operating system very secure,” he added.
You may think Windows is not a secure platform, for example.
“People like to beat up on Windows,” Miller said. “Windows is actually a really good platform. It can be a very secure platform if it is configured correctly.”

Windows may have a reputation for security flaws, but you can make your Windows operating system more secure. Image credit: 6097778
You may have to take extra steps to make sure it’s secure.
“When you install it from out of the box and it comes from HP or Dell or whatever, HP or Dell isn’t trying to take care of your security. They are trying to sell you a laptop with an operating system on it,” Miller explained. “And they are also trying to sell a bunch of software from their partners embedded inside your laptop, too.”
“So, they’re not looking out for your security or your best interests. That is just a reality,” he said. “They make good stuff, they make good hardware, but they’re not thinking about your security as the first thing on their mind.”

You can improve the security of your operating system, no matter which system you use. Image credit: Alessandro89
DIY Security
You can secure Windows and other systems yourself.
Search for security guidelines or hardening guides online.
“They walk you through step by step the right settings to make your machine very secure,” Miller said.
Here are some links to help:
For beginners:
Mac security tips: best Mac security settings
The 10 Best Methods on How to Improve Linux Security
How to configure your Chromebook for ultimate security
For users with more experience:
Hardening Microsoft Windows – STIGS, Baselines, and Compliance
Mac OS Security & Privacy Guide
40 Linux Server Hardening Security Tips
Security Flaws
All operating systems have their own security problems.
“Apple had an administrator — or root level — hack, where anybody could gain access to your computer from anywhere,” he said. “It was quite frightening.”
“People like to say Apple is more secure,” he added. “Honestly, they all have their issues. And they can all be secured in ways that are very secure. So, whichever flavor you like, take your pick and look for a hardening guide for your system.”
You may have to make a tradeoff between functionality and security.
“They’re on opposite ends of the seesaw,” he said. “You may end up losing some functionality for higher security.”
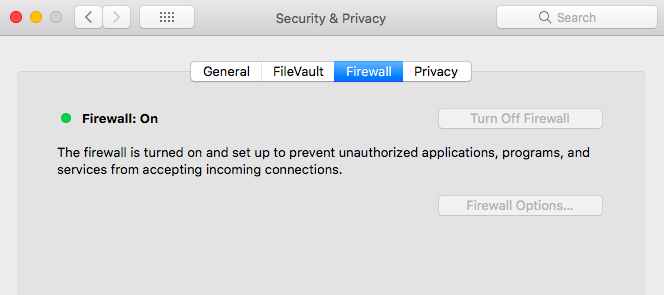
You’ll want to turn on your operating system’s firewall for more security. Here’s how for Windows & for Mac.
Getting Started
One way to dip your toe in is to look at the hardening guides and change one setting, for example, a web browser setting.
“Use the computer for a while and see if it still works the way you want,” he recommended. “Change another setting, use it for a while. So, you don’t end up kind of hardening it so much that you can’t use it. That actually can happen.”
Security can be kind of a double-edged sword, according to Miller.
“Just think of it as if you put 10 locks on your house. It is going to take you 10 times as long to get in,” he said. “If you’re holding two armfuls of groceries, that is going to be rather inconvenient.”
“You want to balance security with what your tolerance levels are,” he advised. “If you want to be ultra-secure, you can have a machine that is absolutely secure using the right hardening guides.”
Security vs. Features?
Does Miller choose a computer based on the security of its security potential or its features?
“I choose my computer based on its hardware. I like my hardware to work together well. I don’t like my components to fail inside the computer,” he answered.
“I know I can secure whatever OS [operating system] I am on,” said Miller.
