This Super Bowl of industrial hacking just took place in Miami
- January 30, 2020
- Posted by:
- Categories: Archer News, Hacking, Industrial Control System Security, Posts with image, Power Grid, Vulnerabilities
As Miami prepares for the biggest football event of the year, hackers are celebrating their own championship wins.
They competed in the same city last week to see who could find the most security holes in industrial equipment.
The results could save lives.
Follow one talented team’s three-day journey to victory — or defeat.
Watch here:
Ready to Hack
We caught up with Steven Seeley in line outside the S4 cybersecurity conference in Miami last week.
Three months of hard work leading up to this moment — his first try at hacking industrial machines — here at the historic Fillmore theater.
“It’s been like a dream, sort of, to do an exploit competition like this, of this sort of caliber,” he tells us. “Really, really cool.”
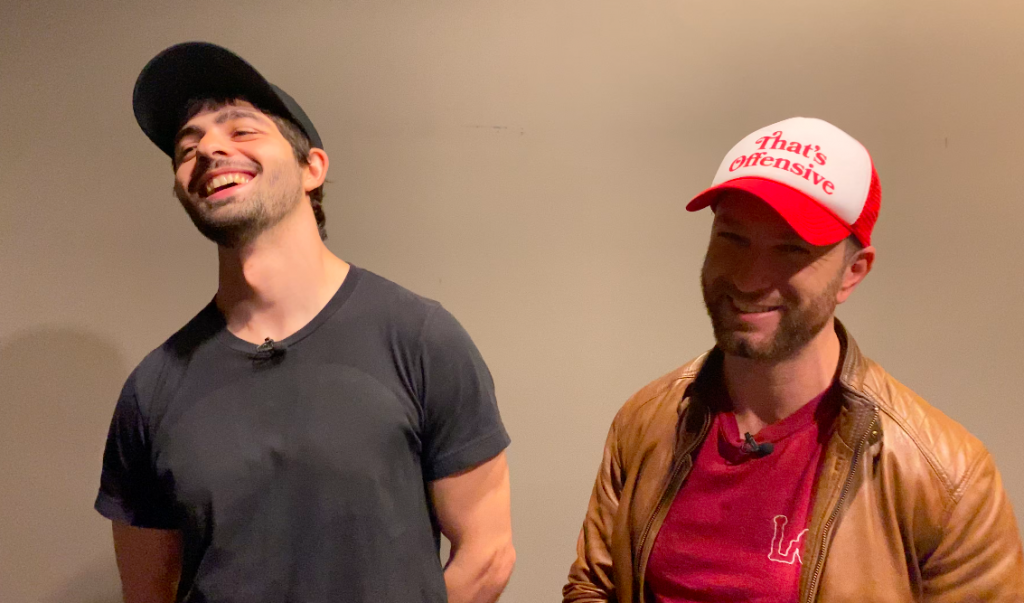
Seeley is based in Mexico City, teaming up with partner Chris Anastasio from San Francisco to hack their way to the top at Pwn2Own in Miami, part of Trend Micro’s Zero Day Initiative, or ZDI.
In this competition, people try to “pwn” — pronounced “pone” — or “take over” software and devices for money and prizes, receiving what they pwned as part of the award.
This time, for the first time, it’s industrial, with eight teams attacking the crucial machines that help run our world.
“Eventually, you work it all out together to achieve what you want to achieve,” Seeley said. “Which is, you know, gaining full control of the machines. It’s scary.”

Going In
Inside, we find out which team goes first. It’s Seeley and Anastasio, also known as Team Incite.
They’re targeting seven different industrial devices or software over three days.
The teams get three five-minute attempts for each target.
“It’s super fun. It’s a challenge,” says fellow hacker Fabius Artrel of Houston, Texas. “It’s almost like a puzzle that has a real world impact.”
Day One
One of Team Incite’s targets on this first day, an HMI, or human machine interface — an essential tool in power plants and factories.
The seconds tick by as Seeley and Anastasio to make the attack they developed at home work live on stage.
“You see them just nervous, nervous until they see that one piece that shows they’ve confirmed it,” said ZDI’s Dustin Childs. “And then, it’s just a huge sigh of relief and then everyone claps and it’s applause and it’s great.”
On this day, with this target, Team Incite’s demo succeeds.
They shake hands and show off their work.
“Rather than have this happen in the real world, we’re doing it in a very closed environment and everyone benefits from that,” Childs said.
For more technical details about the exploits, see ZDI’s Pwn2Own blog.

Day One, Part Two
Next, it’s off to a private room to talk with the device maker to confirm the security bug.
“We pulled it off, I think,” Seeley tells us as he leaves the stage.
But they did not, at least not all the way.
Someone had already reported the vulnerability to the maker.
So, the team gets only a “partial” win and partial points toward the big prize — the Master of Pwn trophy for the entire contest.
Day Two
The second day of Pwn2Own brings success and failure to multiple teams.
Researcher Tobias Scharnowski came from Germany and represents two other colleagues who stayed at home.
“I tested our exploits and I actually modified it yesterday. And the last 20 tries that I’ve performed, only one failed,” he told Archer News. “I tried to make it as reliable as possible. Let’s see what it’s going to be onstage.”
On this day, the demo succeeded, but the bug had already been reported to the maker, so Scharnowski’s team gets just a partial win.
Team Flashback, with researchers Pedro Ribeiro and Radek Domanski, racks up points with a successful demonstration.

Day Two, Part Two
On day two, Seeley’s team is struggling. Their plan for their afternoon attempt is falling apart.
They need another hour. But there’s no time left.
On stage, they try once, twice, three times — with no success.
“And the last attempt is also a failure,” an organizer says.
“Everyone is rooting for a successful demonstration. Except maybe the vendors,” said Childs. “But everyone really is looking to see some great research. And then when it doesn’t, we all feel, we all are up there with them kind of going, ‘Oh, man, that’s too bad.’”
“But we also know that it’s not the end of the world,” he added. “If you’ve done research before, you know occasionally you run into a brick wall or you take a path that leads nowhere.”

Day Three
The final day opens with drama.
Team Incite’s first attempt of the day goes down to the final seconds.
“It was one of the most intense Pwn2Own exploits I’ve seen,” Childs said. “People were incredibly tense. You could cut the tension with a knife, easily.”
Seeley and Anastasio are trying to show how attackers could take control of an industrial software platform, the kind that helps run your critical infrastructure, like lights, water, oil and gas.
In the end, they pwn, revealing the vulnerability — hopefully before a real-world attack.
“And we all exhaled, we all applauded when it finally happened,” Childs said.

Day Three, Part Two
The Incite Team’s second attempt of the day ends successfully and more comfortably, with plenty of time to spare.
But will it be enough?
After the demo, Childs says three teams are in the running for the top prize, Master of Pwn.
The Incite Team, Scharnowski’s team and Team Flashback make up the top three, with Team Flashback currently in the top spot.
But organizers are still tallying points and verifying exploits.
Childs heads to the main stage to reveal the results — without knowing who the winner is.
“Right before I went on stage, they confirmed the previous exploit,” he tells us later. “They said, ‘This is the winner. Mic these guys up and give them a trophy.’ And it was that close. And it was that quick.”

Winners
Who is it?
“Congratulations to the Incite Team. Steven Seeley, Chris Anastasio, why don’t you guys come on up,” Childs announces in front of the crowd.
They did it. They are the Masters of Pwn.
“That was fantastic,” Seeley tells the audience. “It was a fantastic event. Thanks to ZDI and S4 for the conference. And the teamwork and collaboration, I couldn’t have dreamed for better, to be honest. Thanks, Chris.”
They earn not only the trophy, but also at least $80,000 in prize money — plus the knowledge that they’re finding security holes before real attackers do.
Some device makers have already fixed the problems turned up in this Pwn2Own.
“That is how fast these things can go and that is how impactful the contest can be,” Childs said. “Our goal is to make sure these holes get into the light of day. And then we close them and make everyone safer in the end.”
Scharnowski’s team placed second out of eight teams, with Flashback Team in third.
Top Dogs
What does it mean to be Masters of Pwn?
“It means we’ve got to keep trying harder,” Seeley said to Archer News.
“It means we worked very hard and we’ve got to continue to work very hard,” said Anastasio.
“Yeah, it’s a nice recognition of the hard work,” added Seeley.
Chances are you’ll see Seeley and Anastasio again. These Masters of Pwn are not ready to hang up their hoodies and let attackers win.
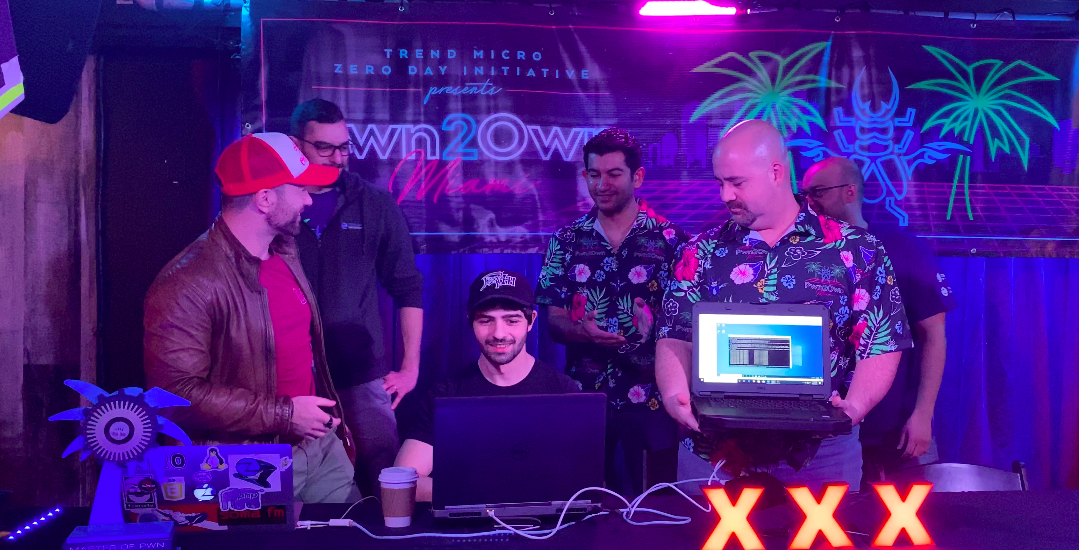
Main image: Team Incite on stage at Pwn2Own in Miami. Image: Archer News
