It’s not over—expect more Internet blitz attacks
- October 22, 2016
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Home Security, Posts with image, Smart Devices

The kind of attack that disrupted major web platforms like Twitter, Amazon and Reddit on Friday will happen again, experts say.
First, there was celebration.
“I CAN FINALLY GET BACK ON TWITTER AND NETFLIX YAY,” said Twitter user Asyla Valentine.
“Twitter’s back! We’ve been #Twitterless all day! What’s happening in the world?” tweeted CEG Talent in New York.
Then came blame, as people theorized that the Anonymous, Wikileaks, Russia, enemy nation-states, and the presidential candidates were behind it.
Twitter users speculated about the identity of the attackers.
But no matter who is behind it, this kind of attack will most likely happen again, according to cybersecurity experts.
“These are on the rise,” said Vincent Berk of network security company FlowTraq.
“You can bet on it,” said Robert Bigman, former chief information security officer for the Central Intelligence Agency and founder of cybersecurity company 2BSecure near Washington, D.C.
“My guess is that they have many more waiting to go—unless you pay up,” he said.
What is it?
This was not a direct attack on Twitter, Amazon, Reddit, Spotify and the any other sites affected—it was an attack on Dyn, an internet service company.
The attackers used a DDoS—a distributed denial of service attack—to send so much Internet traffic to Dyn that it could not keep servicing the big sites.
“DDoS is crude,” Berk told Archer News. “It is simple. It is not a hack. It is just like showing up with 100 friends to the post office—nobody else can get service because your friends are using all the available lines!”
“Think the bandwidth of 100,000 home computers screaming at full bore at Dyn—using all bandwidth they can get.” he added.
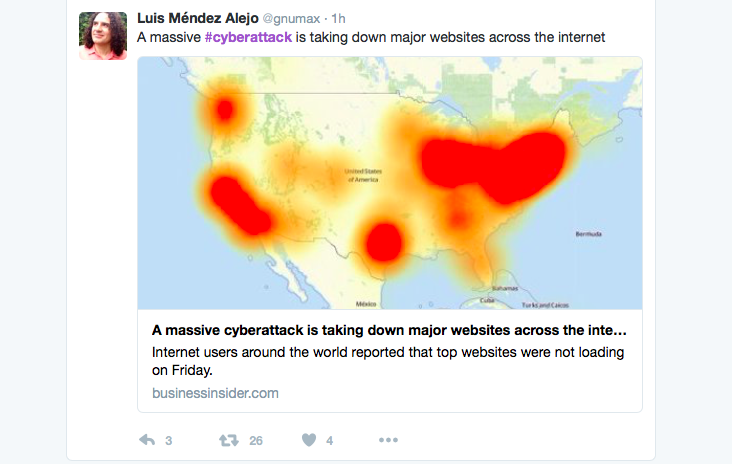
Some Twitter users could not access the site for hours on Friday.
Simple, but effective
The attackers clogged up the lines, so to speak. And in a massive way, experts say.
“Biggest one I’ve ever seen,” said Bigman.
“Considering that the affected service provider—Dyn—has made a business for themselves around mitigating this type of attack, it is reasonable to believe that this is a pretty large-scale attack,” said Craig Young with cybersecurity company Tripwire.
But he adds, the big sites like Amazon and Twitter did not go down. You just couldn’t find them.
“It is important to understand that the attackers have not knocked all of these websites offline but rather they have effectively hidden the sites from users by crippling the systems used to locate sites,” he explained.
“An attack would likely need far more resources to actually take all of these sites down simultaneously,” he said to Archer News.
You did it
Where did the attackers get their army of computers to blast Dyn?
From people’s homes—home routers, security cameras and other connected devices with weak security.
The bad guys use programs to automatically search out your devices with easy-to-guess or default passwords, then take them over. You might now even know your device had been enslaved.
You could be contributing to the next attack that keeps you from your favorite Internet service.

Security cameras make up part of the zombie army that disrupted the Internet on Friday.
Why this attack?
Investigators and researchers are trying to find out who did it.
“We can only speculate at this point but a number of possible reasons come to mind,” said Young.
“At the top of my list would be the possibility that someone is testing or simply demonstrating their ability to disrupt the Internet,” he said.
This could just be a bit of advertising, so a mercenary attacker can show off his or her skills. Other crooks would then pay the attacker to blitz similar targets.
“It is a common practice online for criminal organizations to resell DDoS services, so the ability to create this level of chaos could certainly be a marketing tool,” Young said.
“Probably hacktivist demonstration of the fragility of the Internet,” said Bigman. “Could be precursor for a DDoS ransomware attack.”
Revenge?
Others suspect the attack could be revenge.
Journalist Brian Krebs reported on a large DDoS attack organization last month, and some alleged DDoS attackers were arrested.
Soon after, Krebs’ website was attacked with a record-breaking DDoS.
This attack could come from the same source, according to Berk.
“It is most likely a retaliation for the work the Brian did,” Berk said.
Warning
There was a warning about the possibility of this kind of attack.
The United States Computer Emergency Readiness Team, or US-CERT, put out an alert last week saying that the army of slave devices used to attack Krebs could be used on other sites and companies. These devices are part of the IoT, or Internet of Things.
“Recently, IoT devices have been used to create large-scale botnets—networks of devices infected with self-propagating malware—that can execute crippling distributed denial-of-service (DDoS) attacks,” the warning said.
“Cybersecurity professionals should harden networks against the possibility of a DDoS attack,” it added.
US-CERT warned about the threat of a big DDoS attack.
Defense
Unfortunately, protecting yourself from a DDoS attack is not always easy, especially when they’re large-scale.
“It’s a very smart attack. We start to mitigate, they react. It keeps on happening every time. We’re learning, though,” said Dyn’s Kyle York, according to USA Today.
That means today’s cries of joy, like, “Nice to be able to back on here,” may turn back into tears of sorrow, as attackers continue to use their skills to cripple some of the biggest sites on the Internet.
“I admit I cried all day,” tweeted Maxence Jouve in Marseilles, France.
What to do
What can you do, besides “cry all day”?
Change the default password on your connected devices, like routers and security cameras. If your device has a default password, attackers can find it and capture the device.
Buy smart devices from companies “with a reputation for providing secure devices,” the notice advises, and learn how your device works.
“Consumers should be aware of the capabilities of the devices and appliances installed in their homes and businesses,” it says.
And if a device comes with a default password or open Wi-Fi connection, “consumers should change the password and only allow it to operate on a home network with a secured Wi-Fi router,” according to the alert.
That includes medical devices for use at home.
“If the device transmits data or can be operated remotely, it has the potential to be infected,” US-CERT warns.
