New info on attack campaign against U.S. utilities in 2019
- June 11, 2020
- Posted by:
- Categories: Archer News, Cyber Crime, Cyber Crime, Cyberattack, Cyberattack, Power Grid, Power Grid

Once was not enough.
Researchers now say an attack group launched two different campaigns targeting utilities in the U.S. last year.
Both campaigns used similar strategies and weapons, according to cybersecurity company Proofpoint.
They targeted the same utilities and even the same people, in some cases.
Watch here:
Double Attack
The first campaign used phishing emails designed to trick employees into downloading malware called LookBack.
Some of the fake emails looked like failed exam results from the National Council of Examiners for Engineering and Surveying.
The second campaign used phishing emails to trick people into downloading malware called FlowCloud.
These fake emails included invitations to join the American Society of Civil Engineers.

Similar Strategy
Both LookBack and FlowCloud malware give the attackers “complete control over a compromised system,” according to Proofpoint, including the ability to execute commands, move and click the mouse, delete files and more.
This control could allow attackers to cause trouble in a utility.
“It is another indicator that the wrong people are trying to gain access to the systems that control our critical infrastructure,” said Mark Carrigan with security company PAS Global about the LookBack attacks.
“We should be concerned because it’s pretty clear someone’s trying to get in,” he said.

Small Utilities, Bigger Impact?
Many of the LookBack targets were small utilities, according to The Wall Street Journal.
They include the Klickitat County Public Utilities District in Goldendale, Washington, Alexandria Power and Light in Alexandria, Minnesota, and Rochester Public Utilities in Rochester, New York, according to the The Wall Street Journal.
Why would attackers go after small utilities, instead of larger utilities that could potentially impact more people?
There are several possible reasons, from collecting intelligence to learning how the U.S. grid works.
“They probably also know you don’t have necessarily the resources to protect yourself, like, say, the big ones,” Carrigan told Archer News. “So, you might be their prime target because you’re softer.”
Some of the small utilities are near dams and other critical infrastructure, though they may not actually provide power for those facilities, WSJ reported.
Working Their Way Up
If attackers invade a small utility, they can also pose as that utility and send more phishing emails to larger utilities.
“If you get an email from me, because you know me… you’re probably going to put a little bit more trust in that than if it randomly comes in from the Nigerian prince kind of thing,” said Marty Edwards with Tenable. “A very common intrusion vector or entry vector. And I think everybody should be concerned about it.”
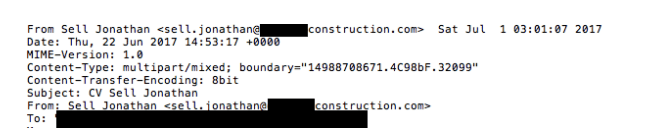
Attackers tried this very tactic in 2017 in an attack on U.S. energy companies.
They infected, for example, a construction company, posed as a construction company employee, then attacked the energy companies.
“A small player in any supply chain can have large downstream effects,” Edwards told Archer News.
“Not just in the energy or utility sector, but in any sector,” he added. “You’d be surprised how many big incidents or big attacks start with somebody small in the overall supply chain.”
Phishing Targets
Both the LookBack and FlowCloud campaigns used phishing emails, a popular strategy for attackers targeting critical infrastructure.
Attackers will scour social media for clues about employees working at utilities so they can make more effective phishing messages, according to Carrigan.
Those crafted messages may convince even well-prepared employees.
“Then it only takes one wrong click,” he said.
Attack Force
Who’s behind the attacks?
Proofpoint identifies the group simply as TA410, a state-sponsored advanced persistent threat actor or APT, typically a nation-state trying to spy or steal information from another country.
“While TA410’s intent for this campaign is perhaps the most difficult thing to ascertain, it appears that they were likely trying to establish an initial foothold in the targeted systems and gather intelligence with FlowCloud’s RAT capabilities,” Proofpoint told Archer News in a statement.
Researchers did not report on any successful downloads of either malware at U.S. utilities last year.
Several target utilities told WSJ that their security tools caught the phishing emails before they could reach the intended recipients.
2020
Archer News asked Proofpoint if researchers have seen any new LookBack and FlowCloud attacks this year.
“We are continuing to monitor this group for future activity,” the company’s statement said.
One of last year’s targets, the Cowlitz County Public Utilities District in Longview, Washington, said it has seen none of these attacks in 2020.
“Cowlitz PUD is aware of the new info regarding LookBack and FlowCloud,” said Public Relations Manager Alice Dietz. “We use Proofpoint services for email filtering and proactively monitor email and firewall traffic. We have found no activity related to LookBack or FlowCloud campaigns.”
Main image: Electric power substation. Image: Wx-BradWang/iStock
