Hack my dust
- March 3, 2017
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Hacking, Posts with image, Privacy, Smart Devices
As tiny “smart dust” computers become reality, some worry criminals—or companies—will invade your personal space.
You just stepped on one. And there could be another one in your left nostril.
Miniature computers are already about the size of a pinhead—and they’re going to get smaller.
“You literally could make these things airborne, in the millions and or trillions, and let them go. And what they do is they collect data,” said Bob Noel of Plixer.
He’s talking about “smart dust.”
It’s already in use in some factories and buildings, though in a somewhat larger form.
Researchers are developing ways for the tiny processors—also called motes— to keep people alive, watch over bridges for cracks and monitor pollution.
But Noel and his colleagues want to make sure life-saving smart dust does not also put people at risk.
“It’s going to be all around us,” said Bob Noel of cybersecurity company Plixer. “And we won’t be aware of what it is or what it’s monitoring.”
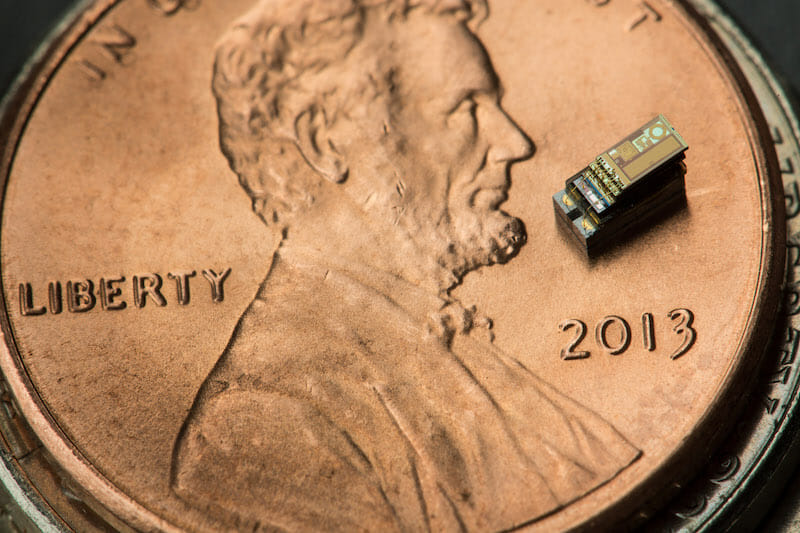
This tiny processor from the University of Michigan made history as the world’s smallest computer. Image credit: University of Michigan.
Almost invisible
You can fit 150 of the Michigan Micro Mote computers into a thimble. This Mote is two millimeters—that’s about .08 inches—and the size of about six grains of salt.
Researchers in Germany last year made a camera lens even smaller, about the thickness of a human hair.
Plans for these itty-bitty components include injecting them into your body to tell your doctor crucial information about your organs, sending them skyward to check air and water quality, and detecting earthquakes—or parking spots in a crowded mall.
Companies could sprinkle some on a package they’re shipping to you to see if their product is damaged during the journey.
The military could deploy them on the battlefield to defeat the enemy—and has already discussed the idea.
Smart dust will be one of the most disruptive technologies over the next ten years, along with self-driving cars and commercial drones, predicted information technology research company Gartner.
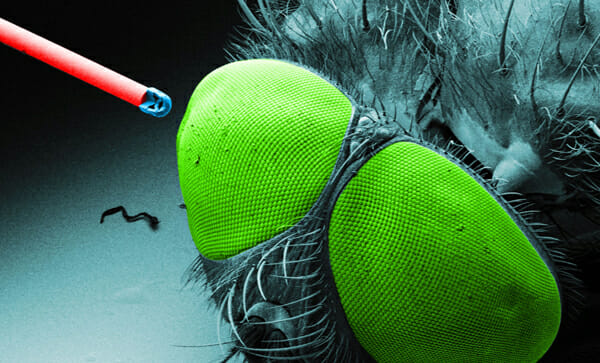
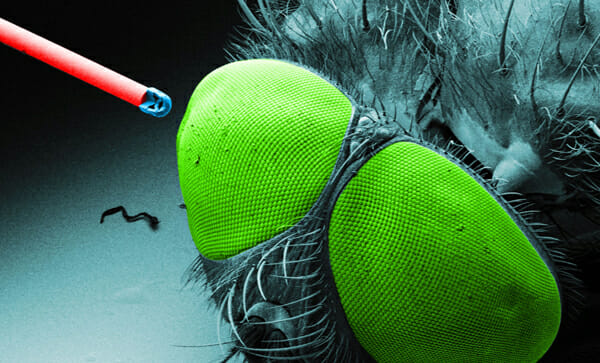
German researchers used a 3D printer to create a camera lens on an optic fiber about the size of a human hair. Image credit: University of Stuttgart.
Hackable?
But these tiny computers could be abused like their full-sized counterparts, according to Noel and Michael Patterson, also of Plixer.
For example, cyber crooks are already hacking into the Internet of Things, taking over smart devices like your home router or your security camera and turning them into zombie computers that they control.
These botnets—network of robot devices—then attack people, companies and governments, even taking down big sites like Twitter, Netflix and Amazon in the process.
“The problem is that when you look at IoT [Internet of Things], most manufacturers today are not building in robust security into that process,” Noel said. “The bad guys have access to thousands of IoT devices and they use those to launch an attack.”
The smart dust computers would become a part of the Internet of Things, Noel and Patterson said.
That mote in your backyard, on the package you just received, or inside your nose, now a zombie computer used to attack your favorite website?
“You could have this smart dust that ends up in a landfill with the ability to run for years,” he explained. “Now think of those in the scale of millions of devices that are in a landfill that are still running that still have Internet connectivity and could be compromised.”

Pile of old computer parts. Image via: Pixabay.
Staying secure
Experts have recommended security for these tiny computers for more than a decade.
And some smart dust manufacturers use security measures like encryption and message authentication to protect the small devices in their networks.
But with the explosion of smart things, some rogue IoT companies are skipping security and selling faulty, vulnerable devices, like light bulbs that allow hackers into your home, and routers that let attackers take over with ease.
Will some product developers who jump on the smart dust bandwagon leave security holes as well? Will they find a way to “kill” the little device when it no longer serves their needs, or let it run on its implanted, long-term battery, abandoned and vulnerable?
“There needs to be a ‘time to live’ on these devices, so that if I’m in the shipping business and I’m putting labels on something with smart dust, that it only stays alive for a year or something like that,” Patterson said.

Researchers said they were able to infect Philips Hue smart bulbs with a spreading digital worm. Photo credit: ursonate via Foter.com / CC BY
Getting personal
A second concern—privacy.
Not malicious hackers, but companies using smart dust sensors to gather as much as they can about you for use or sale. Your data is big money.
“They’re going to collect it. They’re going to know things about you,” said Patterson. “anywhere you go. Anywhere you move.”
“Using this data and behavior and running machine learning, they’re going to profile you,” he added. “Maybe they’ll to go public with that profile or maybe they didn’t intend to go public with that profile, but they were hacked.”
That personality profiling could cause problems, he said.
You might pay more for insurance and other services, have trouble getting a job, be accused of a crime you didn’t commit, or get detained at the airport because your data fits a stereotype.
“I think we need some legislation around just kind of protecting the consumer and keeping everyone honest about what they’re taking,” Patterson said. “There needs to be some level of fairness.”

A “miniature” computer from 1960 that weighed 440 lbs at a Swedish museum. Image credit: Lars Aronsson CC SA 1.0
Get ready
The microscopic computer revolution is coming. In fact, it’s already started.
But Patterson wants lawmakers or industry groups to set up laws or guidelines to make sure the smart dust storm doesn’t do major damage.
His company analyzes the data that goes in and out of computer networks, so with smart dust, more companies might buy his products.
“We’re in the monitoring business and I think it will mean good things for what we do. But ultimately the problem would ideally would be fixed before they fall back on a solution like us to figure out what happened,” Patterson said.
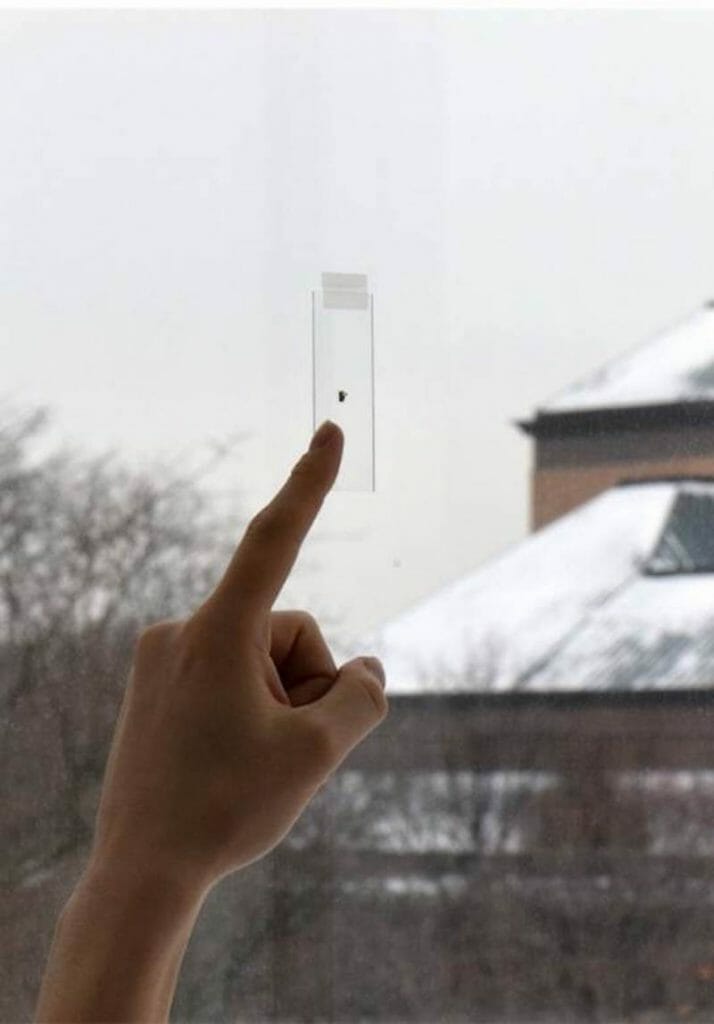
The Michigan Micro Mote on a window. Image credit: University of Michigan
Prepare for it. Computers you can barely see—or can’t see at all, monitoring the world around you—and monitoring you.
You may want to be ready to ask questions about who is watching you, what data they’re sucking up, how secure their device is, and whether someone should make a rule or law to keep companies and/or cyber crooks in line.
“People are looking at this now and it’s a real technology that’s going to evolve,” Noel said. “They’re microscopic, they’re airborne, which means they could be literally anywhere.”
Featured image: Tiny component printed on the end of an optical fiber shown next to a fly’s eye for scale from University of Stuttgart. Image credit: University of Stuttgart
Comments are closed.
