What the big Verizon data breach — with exposed PINs! — means for you
- July 13, 2017
- Posted by:
- Categories: Archer News, Data Breach, Identity Theft, Mobile Devices, Posts with image

Your PIN is meant to be private — a personal identification number that lets you in to your bank account and other places where you need protection.
So when word got out that millions of Verizon customers had their personal information and their PINs exposed, people became concerned — and frustrated.
“Wonderful ????,” wrote Edmund Kuklinski on Facebook, with more than a hint of sarcasm.
“Oh, lovely ????,” added Megan Elizabeth.
“Can you steal my identity now?” asked Dennis Fontaine.
There’s debate over just how much damage this data breach could do to you.
But there’s no question that your phone could be a target for a growing kind of scam, and exposed PINs could warm the scammers’ hearts — and fill their bank accounts.
Facebook users react to the news of the Verizon data breach.
The breach
A risk analyst with UpGuard found a Verizon database open and unlocked, according to a post today.
Security researcher Chris Vickery reported that he discovered the data — with up to 14 million customers’ information and a number of PINs— in an Amazon Web Services data repository on June 8, and notified Verizon.
He said Verizon later fixed the problem.
Verizon said another company that it was using to help improve its customer service accidentally left the data exposed.
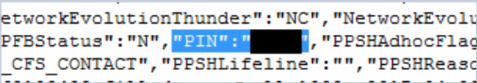
Screenshot showing Verizon PIN information exposed, according to UpGuard. Image credit: UpGuard
PINs
However, Verizon said it checked and found no one else had accessed the database except Verizon, the other company, and the security researcher.
The phone company also said only six million customers were affected.
And those PINs?
“In addition, to the extent PINs were included in the data set, the PINs are used to authenticate a customer calling our wireline call center, but do not provide online access to customer accounts,” Verizon said in a statement.
If true, Verizon customers might rest a little easier, knowing those PINs are not up for sale on the digital black market.
But for some, the breach shows that your information is vulnerable in many, sometimes unexpected, ways.
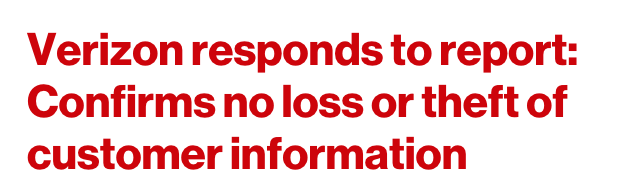
Verizon released a statement about the breach.
Stealing your number
A treasure trove of PINs would make things easier for crooks out to steal your phone number.
Currently, they’re using a number of different tactics to trick you or the phone company into transferring your number to their phone.
It’s a crime that is reportedly popular in Europe and Australia, and now growing in the U.S.
The Federal Trade Commission reported receiving about 26,000 phone fraud complaints last year.
The result — a massive headache for you, fun and profit for the bad guys.
“No service”
It may start when you notice your phone doesn’t seem to be working.
Ed Hyden of Florida wondered why his family didn’t call on his birthday last year.
But he hadn’t lost favor with his relatives, WNBC-TV reported. Someone had stolen his number.
The thief charged about $10,000 to his American Express card.
When the card company called Hyden’s phone to verify the charges, the thief answered and gave the go-ahead.

If your phone suddenly stops working, it could be a sign on phone number theft. Photo credit: 2bmolar via Foter.com / CC BY
How they do it
The scammers use many ways to get your number.
In Australia in January, a man named Martin O’Nea said he answered some questions from a Facebook friend — who was really a crook who’d hacked his friend’s account.
The crook stole his number three times and racked up $12,000 in charges, though O’Nea got most of his money back.
“These bad actors can simulate being you and can move in and out of simulating you,” said CEO Jeff Kukowski of cybersecurity company SecureAuth to Archer News. “They can port your number and simulate being you and get into your account or a company account.”
Other victims
Other victims have said a thief called up, pretending to be from the phone company and asking questions, the FTC reported.
For example, they may ask to “verify” the last four digits of your Social Security number, which they can use to make changes on some phone accounts.
Some Facebook users complained about Verizon’s response to the data breach notification.
In one case, the fake callers said they were from the phone company fraud department and needed the customer to read back a number that had just shown up in a text message on their phone.
The victim gave over the number — which was the verification code the thief needed to move forward, the FTC said.
Crooks can also check out your social media accounts of personal information, or even hack into your computer to get the details, as one set of thieves did last year, allowing them to transfer money out of someone’s bank account, according to computer forensics company 4Discovery.
“Attackers can obtain a wealth of personal information by social engineering,” SecureAuth’s Keith Graham said. “Once they have enough information they can trick a support representative at a phone carrier into porting a number.”
Scammers may ask you to read a code sent to you on your phone.
“Someone broke protocol”
That’s what happened in the case of Justin Williams of Denver, Colorado, this month.
Williams said the crook that stole his number called his phone company, trying to find a phone company worker who would agree to transfer the number without the security passcode.
Finally, after multiple calls, one of the phone company workers gave in, Williams wrote in a post.
“I instantly called AT&T’s customer service line to explain what is happening,” he said. “I give them my name, my phone number, and my security passcode (this is key). The man on the phone reads through the notes and explains that yes, someone has been dialing the AT&T call center all day trying to get into my phone but was repeatedly rejected because they didn’t know my passcode, until someone broke protocol and didn’t require the passcode.”
Finally, PayPal informed him that someone had transferred $200 Australian Dollars from his bank account to another person, according to Williams.
“The fault lies with the AT&T call center representative who let someone manipulate my account without knowing my passcode,” he said.
Justin Williams wrote a post about his phone number theft ordeal.
AT&T provided a response to The Register.
“Protecting customers and their accounts is a top priority. We take this very seriously and have various security measures and protocols to prevent this. In this case, those protocols were not followed and as a result we are taking additional steps to prevent it from happening again,” the statement said.
Tech help
Some companies say technology can help reduce the damage of stolen numbers.
SecureAuth said its systems tell banks, airlines, stores and other businesses if the number has recently been transferred or “ported.”
That’s a red flag, so, for example, a bank might ask questions before allowing big money transfers to go through.
Kukowski said his technology also checks your location, unusual travel, how you type and how you swipe on your phone, and your IP address.
“We look at all those things,” he said. “If any number of them are bad, it’s most likely not you.”
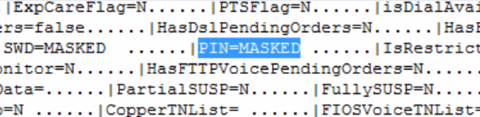
UpGuard reported that many —but not all — of the PINs exposed were “masked” so that a hacker could not see them. Image credit: UpGuard
What can you do?
You may not want to sit back and wait for phone companies to stop employees from breaking protocol, or for every bank to adopt technology to make sure a thief isn’t using your stolen number.
The New York Department of State’s Division of Consumer Protection recommends that you:
—Beware of callers requesting your personal information.
—If you get a cold call from a company, verify by calling the company back directly, not using the return number provided by the caller.
—Don’t store info like passwords and security codes in your text messages.
—Call your phone company if your phone service suddenly stops.
Some Verizon customers said they were going to change their password and PIN.
More help
You can also add a password or PIN to your phone account, though in Williams’ case, it didn’t work.
Still, it may add more protection.
The FTC’s Lorrie Cranor described what each of the four major carriers offer in terms of added protection in a post last summer.
And you can try more in-depth security measures, as described by Forbes, like disabling online access to your wireless account or demanding the phone company only make changes to your account when you show up in person with a photo ID.
A Facebook user reacts to news of the Verizon data breach.
Even more help
You may have one more question.
Should you still use multi-factor authentication — like an extra code the bank sends to your phone to protect against fraud — if the bad guys can just steal your number and use the code?
Some security experts say it’s better than going without, even though it may seem to some to be a hassle.
“Any time you’re asking a user to do anything that takes more than a couple of seconds, it’s hard to get it done,” Kukowski said.
But he added, “Enable your second factor. We should be enabling our second factor.”
