Your typing just gave you away — and that could be a good thing
- June 6, 2019
- Posted by:
- Categories: Archer News, Biometrics, Cyberattack, Identity Theft, Mobile Devices, Privacy

You may remember the meme showing an Alaskan Malamute behind a computer keyboard.
“On the Internet, no one knows I’m a dog,” it says.
Not any more.
Companies and researchers have created ways to figure out who you are by the way you type, plus other online habits.
Your ‘paws’ may give you away.
And that can be a good thing.
Watch here:
Angry Typer?
You might say we’re taking a personality test.
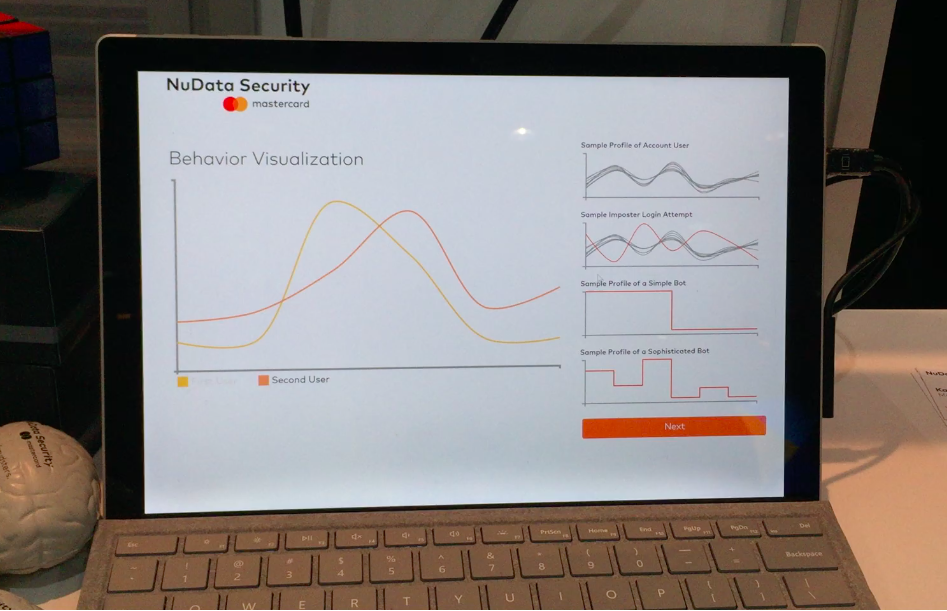
Robert Capps of NuData Security and I type the same sample username and password on a computer keyboard.
It turns out your typing can reveal a lot about you.
“It’s like a digital mood ring!” jokes Capps.
Not really. But Capps says your typing style is unique.
Tools can now check — at millisecond level — how hard you press the keys, how long you hold them down, how quickly you move to the next key, and more.
“Watch what you do on the keyboard,” Capps recommends to all of us. “Watch it a few times, over a few different websites. You’ll notice you’re doing the exact same things over and over and over again.”

Test Results
Our test shows that Capps’ typing style and mine are very different, and even bots can’t replicate them, according to his company.
Type out a word and you create a pattern — mappable, so your computer can tell it’s you, and in theory, only you.
Authentication company Typing DNA shows how it can work in a video.
For example, you use their service on your laptop.
If anyone else tries to get in and steal your passwords or data, the system identifies the incorrect typing pattern and shut things down, according to TypingDNA.
Student Cheating
It could be great way to make sure students taking tests are really the students themselves — and not a cheater jumping in to take it for them, as seen in the recent college admissions cheating scandal.
Prosecutors said wealthy parents paid Mark Riddell about $10,000 each to take 25 ACT and SAT tests for their children to help them get into prominent schools.
Authentication
You can use TypingDNA now as a method of authentication to help get you in to platforms like Twitter, FB and Fortnite, instead of getting a code on your phone.
So convenient! But there’s a problem.
“Huge question. Can it be hacked?” asked Raul Popa, TypingDNA CEO, at a 2016 conference in Romania.
If someone could get to your computer, they could potentially record and imitate your typing style, Popa said.
“This is the way we’ll probably use in the future to hack this system,” he told the audience.
Many Factors
Some security systems combine typing with more of your unique movements and habits, like how you swipe, how you hold your phone, how often you pause and how you use your mouse.
“How you go across the screen, how you hover on a button,” explained BehavioSec CEO Neil Costigan at the European FinTech Awards in 2016. “Would you sweep that way, would you sweep this way, that kind of thing. And we analyze that.”
Analyze, and create a “fingerprint” of your behaviors.
‘What sort of functions are they actually using on a website or mobile app that fit into the normal pattern,” explained Capps. “Knowing when they step outside of that pattern.”
“Once you know that sort of thing, you understand how a consumer presents themselves and how they interact. You can start to make their life a lot easier,” he added.

Convenience
Easier, because you might not need to enter a password to use, say, your bank account online.
And it could make things easier for the banks themselves — or other companies dealing with billions in online fraud.
One of the big problems, according to Capps, is human farms.
Masses of workers, often in developing countries, spend their summers using your identity to open up accounts online.
When holiday shopping starts, they use those accounts to sweep up merchandise with stolen credit cards — and cash out.
“If your account is taken over and transactions happened on a credit card, you may not take a loss for yourself,” said Capps. “But that translates to higher prices when you go back to shop again.”

Under Your Fingertips
Some companies are using this kind of verification on you right now — and you may not even know.
“We’re providing a score about how likely the person is who they say they are. In real time,” said Costigan of BehavioSec.
Forgot your glasses?
Broken arm?
Using your other hand?
Capps’ system can take variations into account, he said.
“So, you might go from a 99% probability match to a 97%. Does that mean it’s not you?” he asked. “No.”
But it might ask you for your password again. Or put you in manual review, just to make sure.

Revealing Emotions?
One thing it can’t do right now is actually serve as a mood ring.
We don’t know if you’re an angry typer — or a happy one.
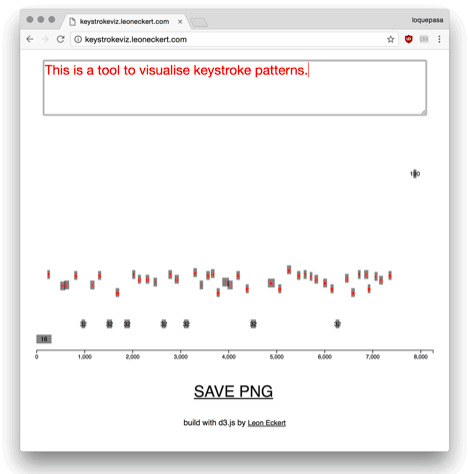
But some researchers have already started looking at whether your typing — your online personality — can reveal your real emotions, like sadness, stress or heartbreak.
“We carry them around with us all times,” said researcher Leon Eckert about phones, laptops and other devices. “They know us really well, too.”
An emotions analyzer could be a benefit for people who need help.
And for attackers who want to take advantage of people in need.
“We open ourselves up to our devices, not the other way around.” Eckert said. “And with that comes vulnerability.”
Main image: Typing on a computer. Image: FancyCrave1
