You can get out of jail — operator jail, that is
- November 15, 2018
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Hacking, Health Care Security, Industrial Control System Security, Posts with image, Smart Devices

You see screens everywhere now, on street corners, in hospital lobbies, at restaurants.
Here’s how easy it is to break through the screen into the computer behind it — and why some experts are willing to tell you how.
Watch here:
Getting In
Internet kiosks up and down New York streets this spring and summer played what some called “creepy” ice cream truck tunes.
LinkNYC, the company behind the kiosks, says it wasn’t a true hack, just a trickster using the call function to dial up phone numbers that play back music.
But hacking your way through a kiosk screen can be all too easy, experts say, as developers skip over basic security steps.
“It is a really common problem,” said security researcher Frank Lycops. “There are a lot of mistakes being made all over again.”
Lycops tests these screens, the kind you see at hotels, on city streets, in airports, hospitals, factories and nuclear plants.
Some hold valuable information.
“I’ve found with kiosk systems with festival tickets a few days before the festival, so only thing I had to do was reprint the tickets, go to the festival and make sure I’m in there before the other guy gets there,” Lycops told Archer News.
It’s true. All along third ave they are playing the Mr. Softee song. Was this truly not intentional? Wow. It feels like a psychological experiment. pic.twitter.com/LBJKHaWWBD
— Steve Burges (@stevenatschool) May 23, 2018
New Yorkers tweeted about ‘hacked’ Internet street kiosks in the spring & summer of 2018.
Operator Jail
Festival tickets are just the beginning.
The kiosk screens are supposed to have a so-called ‘operator jail,’ so you, the ‘operator,’ can’t get past the basic screens to the sensitive inner workings of a hospital or credit card database or power plant.
How secure are many of these jails?
“The easiest and most common ways to break out I’ve found until now is just pressing the shift key five times,” Lycops said.
“From there on you can do whatever you want,” he added.
Shift key on a computer keyboard. Image: TobiDLuxe
Pranks & Attacks
Some escapees just try a little mischief, like the people who put porn up on a parking lot kiosk, as reported by DarkTrace, and condom videos on a hotel tourism screen in Abu Dhabi.
But attackers can use them for more than just entertainment.
A security team tested a visitors info screen in a hospital lobby.
The Independent Security Evaluators 2016 report showed they could not only break in, but even get to patient data and mess with blood samples.
“A lot of people might think, ‘Well, I have an operator jail. I’m safe. The operators can’t do anything wrong or the people using the system can’t do anything wrong,’” said security consultant Dieter Sarrazyn. “It is still out there. It’s still present. The weakness, as we say it.”
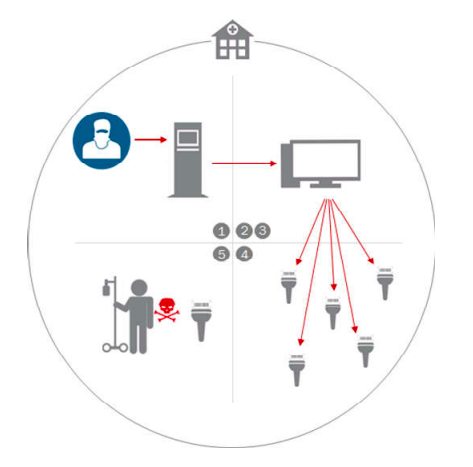
Researchers said they could access patient info through a hospital lobby kiosk screen in a 2016 report. Image: ISE
Industrial Weakness
Sarrazyn and Lycops see many cases where industrial workers break out of their operator jails.
Some try to watch movies on their industrial computers, or HMIs, during long hours on shift.
Others add their own code to make their jobs more efficient — code that ends up crashing the system.
Lycops described one case at the CS3STHLM security conference in Sweden in October.
“Everything worked for two seconds. Then the entire system down,” he told the audience. “They were down for three days just because the operator got bored.”

Example of an industrial computer screen or HMI (human machine interface). Image: Green_Mamba on Foter.com / CC BY-ND
Test Your Screens
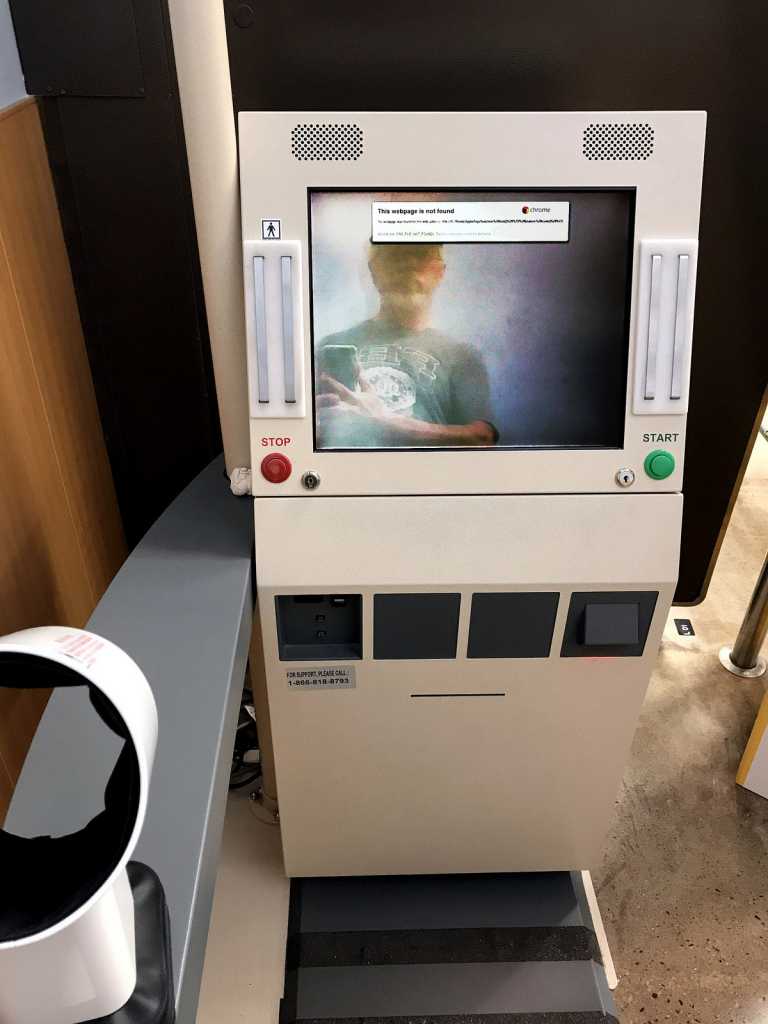
Lycops and Sarrazyn encouraged people at the conference to test their own kiosk screen systems — and showed them how.
“We explain it as, ‘Just abuse your keyboard. Abuse your mouse. Pound on every single key you can imagine. Try every single keyboard combination you can imagine,’” Sarrazyn told Archer News. “With a lot of systems, it’s fairly easy to break it out.”
Archer News asked them why they made this information public.
“Now the bad guys know, but now also the good guys know how to defend against it,” Lycops explained.
“Vendors or integrators are telling people, ‘Look we’ve implemented an operator jail. It is safe. You won’t get access to the operating system,’ and things like that. ‘It’s safe to use,’” Sarrazyn said.
“Good people need to know about it as well because they have a false sense of security,” he added. “They think they are secure but actually they’re not.”

Example of a street kiosk for bike rental. Image: Archer News
More Secure
Dieter and Frank say you can make a real operator jail, without security holes, but it takes work.
Other researchers urged companies and technology vendors to create and follow a security checklist for “multi-user health kiosks,” like the blood pressure machines in grocery stores and check-in screens at clinics.
They should not only secure the software, but also put the kiosks in well-lit areas and use touch screens only, instead of allowing mice and keyboards that could let attackers in, the researchers said.
Blood pressure machine at a grocery store in Virginia Beach, Virginia. Photo by byzantiumbooks on Foter.com / CC BY
Use and Lose?
Until kiosk screens are secure, you may want to rethink entering your personal info into a public kiosk unless you have to.
Lycops said he does not use public kiosks if all possible.
“There are some which you are forced to use, like registration at conferences, things like that. But in hotels, things like that, I don’t use them,” he said. “I’ve seen plenty of them to know there’s a huge chance the system won’t be secure.”
Let’s say you don’t run a system with these kiosk screens, like a hotel or hospital or a power plant.
You may be tempted to test a public kiosk to see if you can break out.
Lycops and Sarrazyn recommend you check the law first to see if it legal where you live, so you don’t end up in a real jail mistake.
And pressing the shift key five times probably won’t set you free.
