What’s going wrong at your water company
- August 9, 2016
- Posted by:
- Categories: Archer News, Cyberattack, Hacking, Industrial Control System Security, Information Sharing, Power Grid, Railway Security

National group finds more than 600 cybersecurity holes in U.S. critical infrastructure.
You may grumble about the size of your water bill, but you’re pretty sure water will come out of that faucet when you turn it on. What if it came out, but the normally crystalline liquid was flush with an overdose of chemicals dialed up by malicious hackers in the water plant?
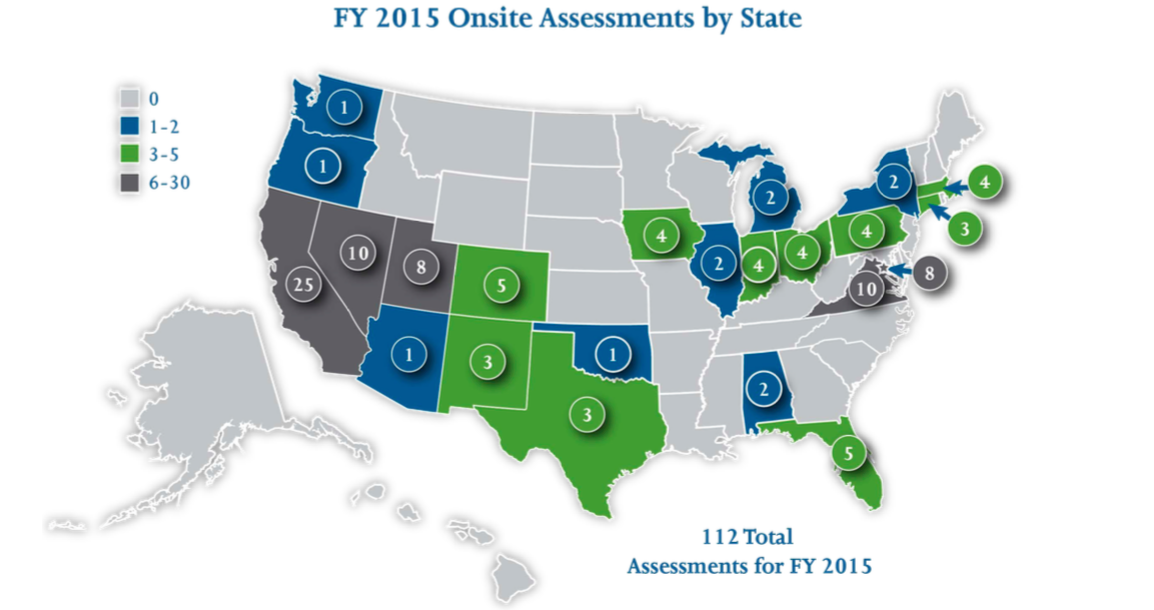
That’s not good for anybody. But the Industrial Control Systems Cyber Emergency Response Team—called ICS-CERT—put out a new report saying it had uncovered 638 security weaknesses in 112 security assessments at water plants, power plants, and other critical infrastructure organizations around the U.S. in 2015.
Some of these weaknesses are the same the group discovered in its assessment report last year, such as issues where companies are not monitoring the digital boundaries well enough so they can tell if bad guys get in, and giving workers far more access to digital systems than they actually need, allowing them to potentially misuse the system.
“We still have a long way to go in securing our factories, plants and ICS systems in general,” said Mikko Hypponen with cybersecurity company F-Secure.
Which plants are vulnerable?
The report did not name the plants with vulnerabilities, but did show a map of where it conducted its assessments, from Washington state to Texas to Florida to New York:
The single most-common weakness found for these plants and factories for both 2014 and 2015 was ‘boundary protection,’ the report said—patrolling the digital fences around the systems that make your water and gas flow, and your traffic lights operate, to keep hackers out.
“Absent strong protection, attackers can more easily penetrate the network boundary around critical assets, access valuable information, and manipulate systems controlled by ICS,” the report said.
BYOD—Bring Your Own Device
The report said organizations also had problems with employees bringing their own phones, tablets and laptops to work and using them in a way that could endanger the system. It also noted that companies were using outdated operating systems and had weak password and authentication set-ups, among other concerns.
Once the bad guys have a password to the machines that run the power plant, it can be far more dangerous than if they guess your Twitter login and started tweeting under your name. But some plants are not using encryption to protect the passwords for these critical devices.
“If encryption is not enabled on authentication, meaning password data are transferred as clear text, attackers can simply listen to the traffic and pull the user name and passwords off the wire while in transit,” the report said.
“Once compromised, persistent access is granted for the lifetime of the user accounts and passwords,” it said.
That can be even worse if the account has passwords that never expire, or if the company does not shut down accounts they no longer use after a worker has moved on, according to the report.
Why is it happening?
There are many obstacles in the way of perfect security at these critical plants and factories, cybersecurity experts say.
One of them—old equipment, Hypponen said to Archer News.
“The vendors are doing their best to improve, but the biggest practical challenge is the long lifecycle of ICS gear,” he explained. “PLCs [programmable logic controllers—-used to run equipment in factories and plants across the country] and other controllers are used for years, sometimes decades until they are renewed.”
“Even if vendors would be shipping perfectly secure ICS gear today, it would still take decades until our factories would all be safe,” Hypponen added.
More connections
Also, companies are connecting more and more industrial systems to the Internet, said Chris Sistrunk with Mandiant, a FireEye company—which in turn creates more security holes.
“We should be concerned but not alarmed,” Sistrunk told Archer News. “Yes, there are a lot of vulnerabilities discovered and reported, since 2010 especially.”
“But—end users are beginning to understand the importance of security,” he said. “Also, vendors are fixing the issues with patches—and also doing more security testing than they ever have before.”
What they need to do
ICS-CERT said it meets with each organization after the assessment and helps them work on fixing the problems.
For example, if the companies allow workers to access critical equipment remotely, the company should add more security layers to verify that worker really is its employee and not a malicious hacker.
They can use a combination of passwords, an electronic key the worker carries with him or her, and a biometric voice print, the report suggested.
The organization should also separate networks so that hackers can’t get into the critical areas through office or home computers, according to ICS-CERT. Companies should not have workers use the same login information for all systems, so that attackers can’t re-use the same user name and password they just hacked to wreak havoc on industrial equipment.
“Whether access is from the corporate network to the ICS or from the Internet to the ICS, this access provides a serious risk to the system,” the report said.
Follow-through
Will power plants, gas and water companies, and factories follow through with the fixes?
ICS-CERT said it is crucial. It’s not just your water that is at risk.
“As the cyber-threat landscape continues to evolve, control systems and their underlying architecture must be secured to withstand cyber attacks,” the report concluded.
“It is important that organizations conduct both risk and vulnerability assessments for the systems that drive the critical automation and processes that support our Nation’s CI [critical infrastructure].”
