What you might see if you were inside the Ukraine power attack
- January 8, 2016
- Posted by:
- Categories: Cyberattack, Posts with image, Power Grid
A cybersecurity expert says grid operators might have been ‘blinded’ by a cyber invasion.
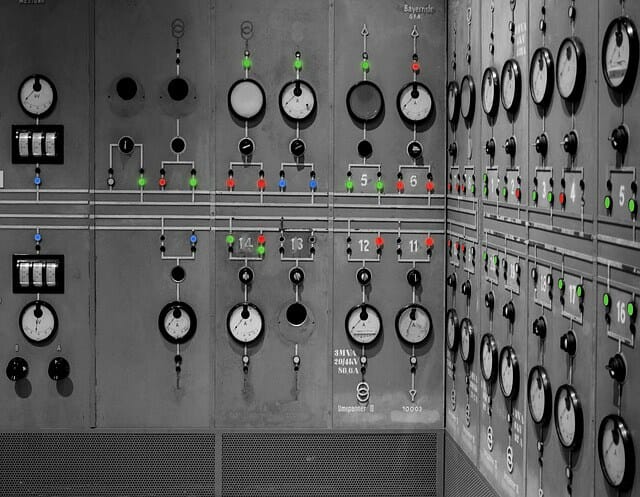
If you are at the helm at a grid control center, you can’t just relax with a coffee and read the latest articles from Archer News. You need to monitor the “load,” making sure levels do not get out of balance and trigger an outage.
But what happens if you can’t see?
A cybersecurity expert says that is what may have happened inside a control center in Ukraine on December 23, when substations shut down and the lights went out for thousands of people in Kiev and the Ivano-Frankivsk region. Malware was found on the systems, and the Ukraine energy companies called it a hacker attack.
Operators may have been blinded to conditions on the grid.
“This is not a good thing, and is analogous to you losing your brakes,” said Michael Toecker of Context Industrial Security. “It’s okay, so long as you don’t need to stop.”
But the grid is like a living thing, constantly changing, and in need of adjustment to keep your lights on and to keep power flowing to hospitals and businesses.
“The grid will keep moving while the operators are blinded, but if conditions develop that the operators need to take action on, they will either not know to respond, or will not be able to respond,” explained Toecker.
Cybersecurity experts around the world are still trying to figure out if hackers shut down the power completely through cyber means—possibly, a first-of-its-kind situation—or if malware may have simply helped attackers carry out a human-caused outage.
So far, researchers have not agreed that there is a direct path from the found malware to the outage itself.
“In this scenario, the hacker doesn’t cause the outage, but the hacker does remove a lot of the awareness and capability to manage the grid,” said Toecker. “The attacker didn’t cause you to crash your car, but he made it so that you couldn’t stop when you needed to.”
Did KillDisk kill the power?
Researchers said they found malware—BlackEnergy and KillDisk—on the system of a power company affected in the outage.
BlackEnergy may have let the attackers in, but what did KillDisk do?
KillDisk is blamed for deleting files in attacks on Ukrainian broadcasting companies in the fall of 2015.
“Based on what I have seen of the KillDisk component so far—and its ability to delete system processes and potentially make the operating system unusable—there is nothing there to indicate that it would have caused a power outage,” Robert M. Lee of the SANS Institute told Archer News.
Lee said deleting files is not enough.
“Deleting files, processes, or killing Windows systems will not cause a power outage in a regional control center,” Lee explained in DataBreachToday. “Kill the Windows computers and the power keeps going.”
“It is far too early and there’s not enough data currently to fully support any theory on what caused the impact,” Lee said.
Debate over the attack
Some cybersecurity experts say the malware may be able to lead to a blackout.
“I do believe that BlackEnergy malware could potentially cause a power outage,” said Marina Krotofil, an independent industrial control systems researcher from Ukraine.
Analyzing the data
Krotofil reviewed a report on the malware by ESET on WeLiveSecurity.
She points to the report’s determination that the the KillDisk found in the electricity distribution companies can not only delete files to make the system unbootable, but also “appears to contain some additional functionality specifically
intended to sabotage industrial systems.”
“If a host/computer running critical software becomes unbootable, this can lead to various consequences, including disconnection of substations,” Krotofil told Archer News.
The malware may also be able to terminate a process used in running industrial control systems, Krotofil noted that the report said.
“Termination of a process can certainly lead to the termination of a software application functionality—in this case, it could be remote connectivity to substations,” Krotofil said.
“These processes can potentially also belong to proprietary software of local Ukrainian producers,” she added, and pointed to these links:
http://it-energo.com.ua/ru/produktsyya/prohrammnoe-obespechenye/
http://galcomcomp.com/index.php/ru/nashi-proekty/15-proekt3-material-ru
Finally, she highlighted that the report said “the binary of the SSH server actually contains a backdoor,”
“Again, this gives hackers permanent access to infected computers, and hackers could then interfere with the telemechanic system, as was stated in the initial report about the accident on the national television,” she said.
However, Krotofil said this is just brainstorming on possibilities.
“We know too little details about what has exactly has happened to say anything for certain,” explained Krotofil.
Other cybersecurity researchers say this analysis may not be correct.
“Many researchers and companies are pointing to the termination of certain processes as tailoring to the ICS (industrial control systems) environment. I believe that analysis to be premature,” said Lee.
Missing link
Cyber investigators are looking for a key clue, the one that could explain exactly how an attack might have happened.
One of the areas of focus is SCADA, the all-important ‘supervisory control and data acquisition’ system that allows people to remotely monitor and control equipment, including equipment that helps run the grid.
“We’re missing any pieces that have a SCADA-specific component,” said Toecker.
If KillDisk did compromise the SCADA system, that still doesn’t completely explain the blackout, said Lee.
“The SCADA system is a supervisory system,” Lee said to Archer News. “It is not good for the SCADA system to go out, and over time there will be problems, but it does not mean that the power instantly goes out. And the narrative that KillDisk caused the impact is not consistent with the evidence presented so far surrounding the events.”
Outage or no outage
Some experts say cyber attackers don’t need to actually cause an outage to cause problems for energy companies. They say the Ukraine attack may show that hackers can cause damage, even if the lights stay on.
“There are parts that if you break them, you are in a lot of trouble — 6 to 12 months of trouble,” said James Arlen with Leviathan Security Group.
“Losing your HMI’s (human machine interfaces) and having to rebuild them is a big impact,” said Patrick C. Miller with Archer Security Group. “That’s significant time lost, temporary degraded capability while you operate in a manual mode, and you will always wonder if you really got all of the malware out—do they still have any code or even possibly a command and control path?”
“We need more evidence. We can only hope they have enough forensic evidence to piece it all together—and that the attackers didn’t do a good job of covering their tracks,” Miller said.
