What you can learn from the pipeline ransomware attack — no matter where you work
- March 5, 2020
- Posted by:
- Categories: Archer News, Cyber Crime, Cyber Crime, Cyberattack, Cyberattack, Data Breach, Industrial Control System Security, Posts with image, Ransomware, Ransomware

When attackers decided to take over computers at a U.S. natural gas company, they didn’t start with a fancy hack.
They just sent an email.
Watch here:
Front Door
A gas pipeline shut down. Ransomware freezing out files. A company in crisis.
All because someone clicked.
“You’ve got to pay attention to those emails that are coming in, because that’s how the bad guys are getting in through the front door,” said James McQuiggan of security company KnowBe4. “You can have the best security system, but you click on that link. It’s just like opening up your front door.”
How They Do It
Attackers still try the basics, like messages saying a package is coming your way or it’s time to change your password.
But security experts say phishing emails are getting harder to detect.
Once attackers choose a target, they’ll scope out employees on LinkedIn, Twitter, Facebook and more to craft a special, poisoned message.
“If they have any kind of social media thing out there, they are a target. Someone is trying to figure out who they are,” Mark Carrigan with security company PAS Global told Archer News. “Learn something and target an email specifically to get you to click on it.”
The Department of Homeland Security has not reported what kind of email the attackers used.
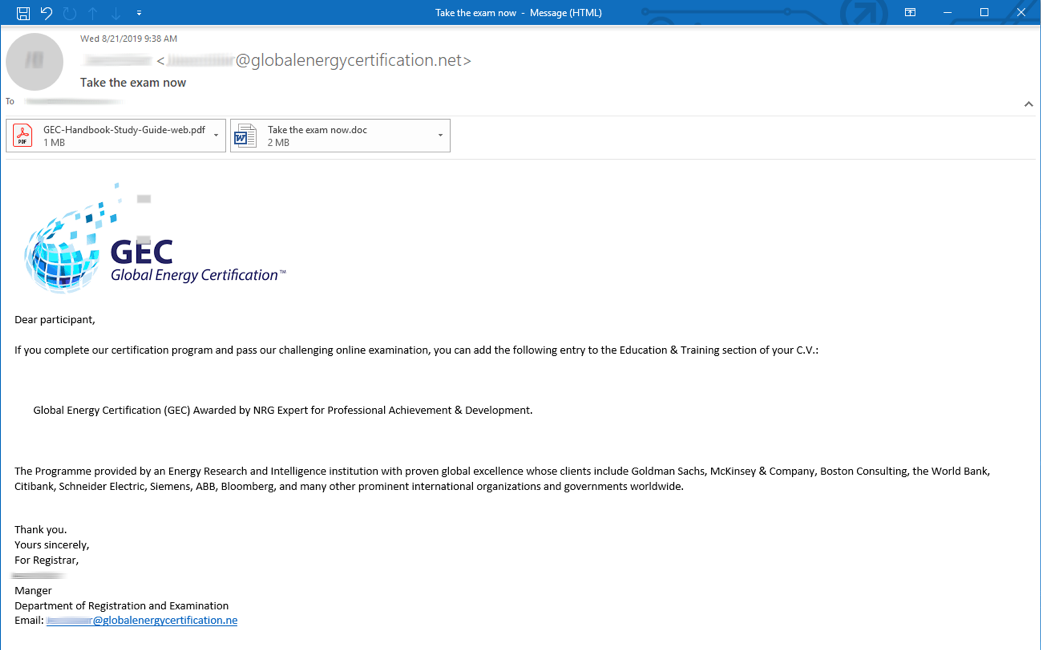
But previous campaigns against utilities used emails pretending to be from a certification organization with the message “Take the exam now.”
New Strains
The pipeline company may have gotten lucky.
Their attackers used Ryuk ransomware, which encrypted files and slowed down operations.
But new kinds of ransomware are making the rounds, like DoppelPaymer, which reportedly just hit parts maker Visser Precision in Denver.
Blackmail
The DoppelPaymer attackers not only encrypt files, but also threaten to publish a company’s sensitive information if you don’t pay.
In Visser’s case, those sensitive customer files could include Tesla, Boeing, Lockheed, SpaceX and more.
Another ransomware called Maze also will steal and publish sensitive info.
In one case, Maze criminals also hit up patients of a plastic surgery office, saying, ‘Pay up or we’ll make your personal pictures and data public.’
“When they do hit you with the ransomware, you think, ‘Oh, my gosh, they’ve just gotten it.’” McQuiggan said to Archer News. “No, they’ve been in for weeks and they have literally taken you down.”

Slow It Down
What can you do?
Recognize that email is a weapon pointed at you.
Pause, ask, verify — instead of simply clicking.
“When they want you to click on something, they want you to take action right now. You’ve got to be able to take a moment to kind of take a breath,” McQuiggan said. ”Go get a cup of coffee, go for a walk and then see.”
Here is more info on social engineering and how you can “hack yourself” to protect yourself.
“You’re going to have to have a constant awareness campaign about security and about concerns,” Carrigan said. “Stop clicking on things. Be very careful.”
Falling Behind
With so much ransomware on the loose, companies are prepared, right?
A recent Swiss cybersecurity agency warning says otherwise.
In February, the Swiss MELANI and GovCERT reported that small and medium business were not making wise security decisions and were falling victim to ransomware.
“A technical analysis of the incidents revealed that the IT security of the companies affected was often incomplete and the usual best practices (Information security checklist for SMEs) were not fully observed,” the warning said. “Furthermore, warnings from the authorities were not heeded.”
Better Practices
Companies can use technology to help filter out sketchy emails, tell users when an email is coming from outside the company and monitor for attacks.
Other steps include:
—Update or patch systems as soon possible
—Keep good backups and regularly verify that they’re intact
—Separate sensitive computer networks
—-Be prepared with a response plan
The gas pipeline company had no response plan for ransomware attacks, according to DHS, even though ransomware has hit hundreds of schools, cities and critical infrastructure in the past year.
Some experts say it is impossible to keep people from clicking on links, so a response plan is essential.
The company also did not separate its sensitive operations network from its corporate network, allowing the criminals to jump from one side to another.
“It’s going to get worse before it gets better,” McQuiggan said.
Not Just Email
Recent research shows attackers are often using other ways to get in.
F-Secure found attackers are using brute force — or credential stuffing — to launch ransomware.
They try as many passwords as possible to see if they can get in.
Since people often don’t change the default password, reuse passwords and use easy passwords, the attacks are often successful.
Multi-factor authentication can help keep attackers out.
The F-Secure report also notes that ransomware gangs are trying remote desktop protocol — or RDP — attacks.
Remote desktop protocol allows legitimate people to access systems for work or repair.
But if you use easy-to-guess RDP passwords or secure RDP poorly, you can give ransomware attackers an open door to your system.
You can also set limits on the RDP ports so that only certain devices can access it.
Main image: Example of a pipeline. Image: Zorazhuang/iStock
