“Victim” sends infectious gift to scammers
- August 17, 2016
- Posted by:
- Categories: Archer News, Cyber Crime, Ransomware

Researcher turns tables, gives ransomware to tech support scammers.
If you get a call from a tech support scammer, you might hang up—and shake your head in disgust.
But a cybersecurity researcher in Paris made use of his opportunity, not only to connect with the bad guys, but also give them a special gift—malware.
“I always mess with scammers as a matter of principle—usually, this only involves replying to e-mails, but I’m open to anything,” said security researcher Ivan Kwiatkowski. “It is my personal belief that the scammers’ business model wouldn’t be profitable if they were spammed back with fake victim replies.”
This time, it wasn’t just e-mail, or spam. It was ransomware, which can hold their files hostage.
The bad guys may need those files to keep the illicit cash coming in—the FBI said tech support scammers stole more than $2 million from people just in the first four months of this year.
“To give you an analogy, if baiting a gullible person is like finding a needle in a haystack for them, I recommend we throw needles at them,” he told Archer News. “Well, you get the idea—my dream goal is to collectively waste their time until it’s not rational for them to keep doing what they do.”
The sting
The first call came from Kwiatkowski’s parents. They had landed on web page that claimed their computer was infected, and contacted him—in a panic—for help.
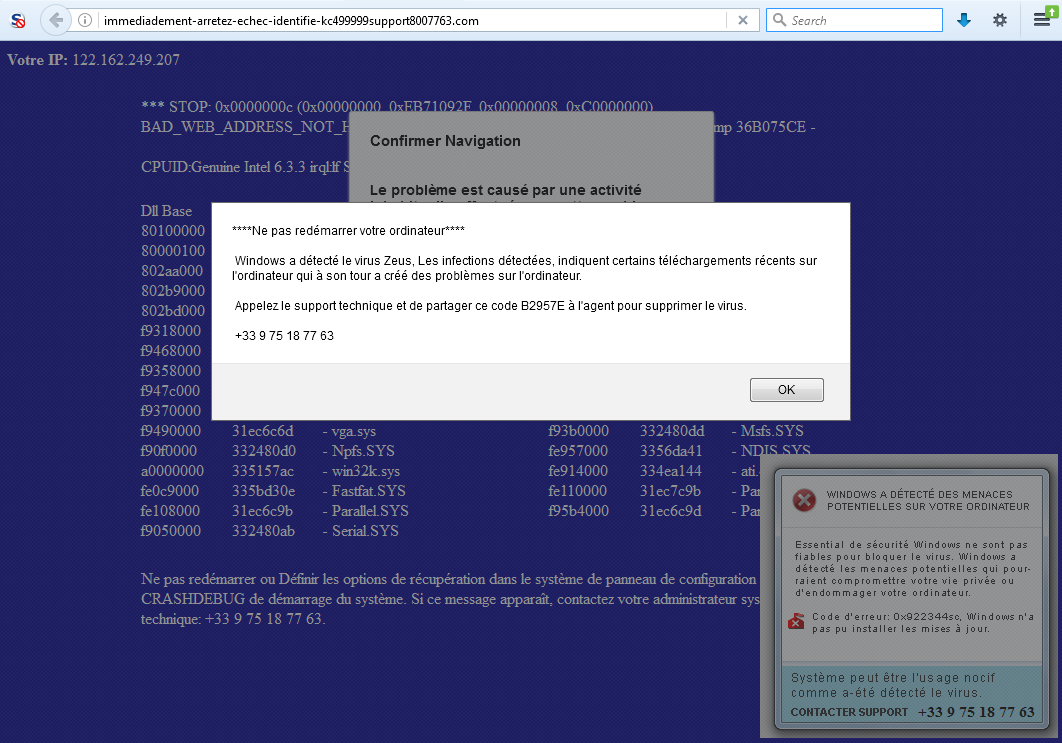
Tech support page image from Ivan Kwiatkowski.
“I had heard about these types of scams in the past, but had never encountered one myself,” he said. “So when the occasion presented itself, I nabbed it, because as a security expert I’m very interested in the ways crooks operate.”
He decided to call the number listed, and eventually got through to a real person.
“I immediately try to get her hopes up by telling her that I’m a businessman working on an important, high-figure contract, and that time is of the essence,” Kwiatkowski writes in a post.
He’s using a virtual machine—“basically, a computer running inside another computer”—that lets him interact with the bad guys without fear of takeover.
Command not found?
The first rep examines his computer remotely, and tells him his machine is infected.
“Look! In the terminal! 1452 viruses found!’ she says.
The smoking gun, she claims, is the phrase “command not found” on the screen.
That can make security experts laugh out loud.
LOL
“To understand why this is funny, I must first explain how ‘low-budget’ their bamboozling attempt is,” Kwiatkowski said.
They could have written a program that at least looks legitimate, and displays scary-looking red pop-ups to frighten the victim into believing there is an infection, he said.
Instead, they opened the command prompt, typed in some words, and then let the computer respond as it normally would. Since they did not type an actual command, the computer responded with the phrase, “command not found.”
“This is the computer science equivalent of opening Microsoft Word, mashing the keyboard randomly, and then explaining that Word underlining words in red is a sign of infection,” Kwiatkowski explained.
“So it’s kind of ironic that the demonstration which is aimed at demonstrating computer expertise actually involves the computer complaining at the user for not making any sense,” he said.
Biting back
The rep’s attack lost its steam, and she eventually hung up. Kwiatkowski called a second time.
This time, the new rep repeats that his computer was infected, and that he needs a “tech protection” subscription—for more than $300—so he will never get viruses again.
Kwiatkowski sends him test credit card numbers, which of course do not work for payment.
“That’s when I’m hit by a stroke of genius,” he wrote in his post.
Sharing is caring
He noticed that the remote assistance tool the scammers were using to access his machine allowed him to share files, too.
“This was actually a spur-of-the-moment idea—definitely not something I had planned before calling,” he said.
He grabbed a sample of ransomware from his “malware collection” he uses for research and sent it through, pretending it was a picture showing his credit card numbers.
“I took a photo of my credit card, why don’t you input the numbers yourself?” he tells the rep.
“I tried opening your photo, nothing happens,” the rep responds.
“Your pictures are corrupted because your computer is infected,” the rep adds. “This is why we need to take care of this.”
What happened?
Kwiatkowski does not know if the ransomware installed successfully on the scammers’ machine.
If it did, he said, the original malicious hackers who were running that version of ransomware would get any “hostage” money paid, and would theoretically be able to unencrypt the files.
Kwiatkowski himself would get nothing, he said. At least, not money. Kwiatkowski hopes he has achieved his goal—to disrupt the scammers’ operations.
“Well, I certainly hope they lost some of their precious time,” he said.
He estimates the damage to the computer system was minimal.
“But realistically, a single operator’s computer might have been trashed, and it’s unlikely that non-backed-up ‘customer’ data was present on it,” he said. “I’d say someone just lost a few hours reinstalling Windows, and that’s good enough for me.”
Right or wrong?
This malware gift for scammers has sparked debates over ethics, according to Kwiatkowski. Is it right to send ransomware to anyone at all, criminal or not?
“My position on this subject is that as soon as the scammers enter my life, I’m put in a catch-22 situation,” he said. “I can either walk away knowing that innocent people are next in the call queue, or I can attempt to hinder their operations the only way I know.”
“Either way, I’m breaking a moral rule, and I feel like the walking away part is worse,” he added. “That it’s also incredibly satisfying to beat them at their own game doesn’t change the fact that it’s also the right thing to do in my opinion.”
Call tips
What about Kwiatkowski’s parents? It turns out their computer was never really infected after all. They called their son for help, and did not give money to the deceptive operation.
If you’re reading this, you probably won’t fall for the next tech support criminal who rings you up. But if you know someone who is less tech-savvy, you can remind them of these tech support call tips from the Federal Trade Commission:
—Don’t give control of your computer to anyone who calls you offering to “fix” your computer.
—Never give out or confirm your financial or sensitive information to anyone who contacts you.
—Getting pressure to act immediately? That’s a sure sign of a scam. Hang up.
—If you have concerns, contact your security software company directly. Use contact information you know is right, not what the caller gives you.
