A second wave of “bomb” malware hits Saudi Arabia
- January 12, 2017
- Posted by:
- Categories: Archer News, Cyberattack, Hacking, Posts with image
And how this kind of malware could impact you.
You might call it The Return of The Return of Shamoon.
Shamoon is a file-killing malware attack that reportedly wiped out more than 30,000 computers in Saudi Arabia in 2012.
It came back in November 2016, earning the name Shamoon 2.
And now researchers have discovered, there is a second wave of Shamoon 2 trying to inflict damage on the Middle Eastern country.
This new version could be even worse.
“What is really worrisome about this is it’s just outright destructive. It isn’t really trying to steal anything,” said Andrew Plato, CEO of Anitian Enterprise Security. “It’s the closest thing we’re going to get to a cyber bomb.”
Could it happen in the U.S.? It’s possible, though rare, experts say.
Still, you might feel the impact if this “cyber bomb” went off somewhere else.

Riyadh, Saudi Arabia. Shamoon attackers have targeted this country three times, according to researchers. Photo credit: Wajahat Mahmood via Foter.com / CC BY-SA
New wave
The first wave of Shamoon 2 hit on November 17, targeting Saudi government agencies like the General Authority of Civil Aviation, Bloomberg reported.
The second wave focused on another date—November 29—and apparently a different target, according to Robert Falcone, threat intelligence analyst at Unit 42 of Palo Alto Networks.
Still, he said, it looks like the same cyber crooks in action.
“The similarities in both waves of attacks are highly suggestive indicators of being the same threat actors,” Falcone said to Archer News.
They both use “Disttrack” malware, wiping out data in a destructive way, replacing key files with images of a Syrian toddler who died at sea, his research showed. They both set a “kill time” for an hour or day when few employees would be at their desks.
But the new Shamoon 2 attackers may have wanted to twist the knife a little deeper.

Airport in Dammam, Saudi Arabia in 2010. The first wave of Shamoon 2 attacked the government agency that handles the country’s airports. Photo credit: yosoynuts via Foter.com / CC BY-ND
“Major development”
The new Shamoon 2 can also attack a VDI, or Virtual Desktop Infrastructure, Falcone said.
The VDI takes snapshots of your system so you can restore it if malware destroys it, according to Falcone.
“VDI solutions can provide some protection against a destructive malware like Disttrack through the ability to load snapshots of wiped systems,” he wrote in a post about his research.
Attack the VDI system, and you could do major damage.
“In essence, a manual destructive attack against the VDI deployment and snapshots, coupled with the destructive attack by the malware, could destroy an organization’s systems and primary line of backup against such an attack,” Falcone said.
The new Shamoon 2 attackers included credentials—logins and passwords—for VDIs, a possible attempt to get to the victim’s’ backups, he noted.
“If true, this is a major development and organizations should consider adding additional safeguards in protecting the credentials related to their VDI deployment,” Falcone wrote in his post.
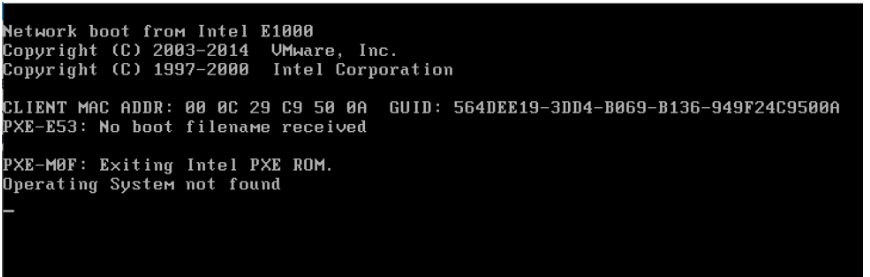
“Operating System not found”—what you might see on your screen after the Shamoon 2 malware destroys your computer. Image credit: Palo Alto Networks
“They’re everywhere”
How common are VDIs?
Very, according to Plato.
“A VDI is a virtual desk top environment,” he said. “The reason we care about it is because they’re everywhere.”
You probably don’t have one at home, but you may use one at work. It’s usually a more secure arrangement, Plato said.
“When you get a to corporate environment, a computer is not actually a computer. It’s kind of a dumb terminal and it runs a virtual desktop,” he said.
Stores and call centers use them, too.
“You go to a store. They’ve got a cash register there, a lot of times, at a virtual desktop,” he explained. “It’s not a full computer. It’s running an image, a virtual image, that’s downloaded from a server somewhere.”

Retail stores may use VDIs at their checkout counters. Photo credit: Random Retail via Foter.com / CC BY
Impact
The new Shamoon 2 malware appeared to target VDIs from Huawei, a Chinese technology and networking company, according to the research.
That could be good news for people in the U.S., Plato said, because Huawei VDIs are not as common in the West.
“The chance of it having a huge impact here in the U.S. is probably a little smaller,” he said.
Still, the malware could be retrofitted for other VDIs, Plato suggested, or it could hit businesses in the east that you depend on for help, like call centers.
“When you call that call center and you can’t seem to get through to them,” Plato gave as an example. “Most likely what’s going on is all the employees that work there, their computers aren’t working. So, that’s where you would see the impact.”

Call center in Egypt in 2009. Call center employees may use VDIs at their workstations. Photo credit: markhillary via Foter.com / CC BY
“Escalation in tactics”
Earlier versions of file-killing malware did have an impact in the U.S.
Cyber attackers used the ‘wiperware’ to take out computers in hacks of Sony Pictures and the Las Vegas Sands Corp. in 2014.
Cybersecurity company FireEye recommended critical infrastructure organizations and government agencies check their systems after the first wave of Shamoon 2 in November.
For now, the new version of Shamoon 2 attacks may be limited to one organization in one country.
But others should take note, Falcone warned.
“The targeting of VDI solutions with legitimate, stolen or default credential represents an escalation in tactics that administrators should be aware of and take immediate steps to evaluate and address,” he wrote.
Featured image: Element of the new wave of Shamoon 2 malware. Image credit: Palo Alto Networks.
