Scam Alert #26 — WhatsApp trap & shady phone employees
- August 9, 2018
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Data Breach, Hacking, Health Care Security, Industrial Control System Security, Mobile Devices, Posts with image, Power Grid, Scam Alerts, Secure Messaging, Vulnerabilities

Don’t trust every message you get on WhatsApp.
People can hack you with fake messages — and in some cases, it’s deadly.
This, plus shady phone company employees on the job, in this week’s scam alert.
Watch here:
WhatsApp Trap
WhatsApp is a popular messaging app around the world.
Like many apps, you can set up groups for messages.
But be careful whom you add to your group.
A security team found group members can change your messages — and put words in your mouth.
Check Point’s demo shows an example where researchers intercept a message and change it to add a rumor about a product making kids sick, potentially causing confusion and chaos.
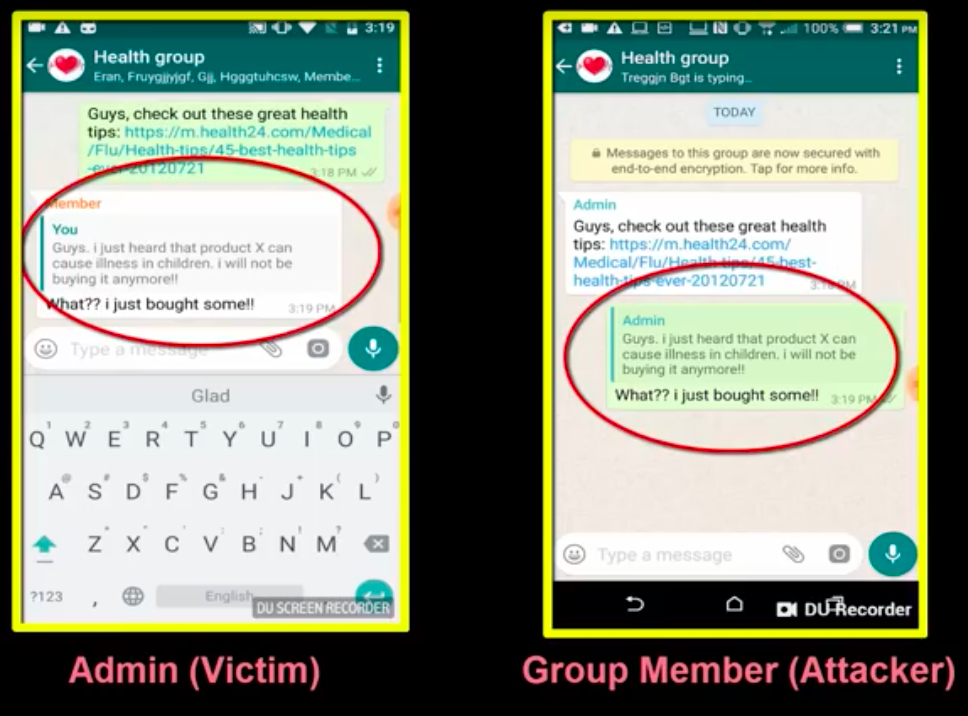
Researchers demonstrate how they add a fake message to a group WhatsApp chat. Image credit: Check Point
Fake WhatsApp rumors have become a deadly problem in India.
Some people there have spread messages about gangs of child kidnappers and organ harvesters.
In response, unruly mobs have attacked and murdered innocent victims.
WhatsApp told Reuters it’s increasing education efforts to help people detect fake news and messages.
Security Week reported that WhatsApp is also making some changes in group chats and putting limits on forwarded messages to try to control fake messages and rumors.
Hacking your Health Records
The doctor is not keeping paper charts anymore.
Your medical records are digital — and researchers are checking to see if they’re safe from hackers.
The bad news?
They found big security holes in medical records software used for about 90 million people.
A group called Project Insecurity checked OpenEMR, one of the most popular free medical records software systems in the world.
The researchers say more than a dozen severe flaws would let attackers in to take your medical data and use it against you.
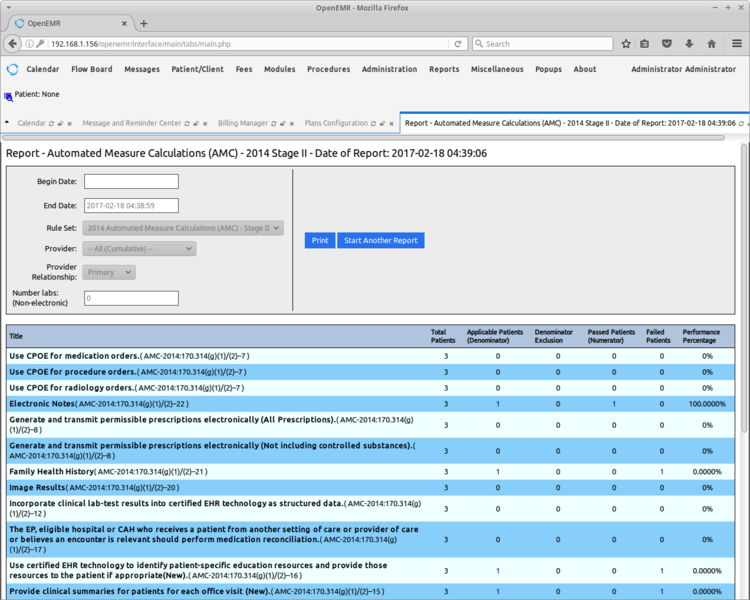
OpenEMR software allows health facilities to keep track of patients’ medical records. Image credit: OpenEMR
They reported it to OpenEMR.
OpenEMR fixed the problem and put out an update.
Now, it’s up to medical offices to make sure they are updating the software.
The CE of OpenEMR sent a statement to DataBreaches.net saying, “The OpenEMR community is very thankful to Project Insecurity for their report, which led to an improvement in OpenEMR’s security.”
“The OpenEMR community takes security seriously and considered this vulnerability high priority since one of the reported vulnerabilities did not require authentication,” the statement added. “A patch was promptly released and announced to the community. Additionally, all downstream packages and cloud offerings were patched.”
Stealing your Electricity
You don’t want your electricity up for sale on the black market — just another hot item for attackers who could snap it up and shut down your power.
But a security company says their test found attackers ready and willing to take over parts of power companies.
Cybereason says it set up a decoy transmission substation online under the name of a well-known utility.
Researchers say in just two days, attackers took it over and put it up for sale on the dark web.
Within ten days, the new owner launched attack operations.
Luckily, it was just a test.

An example of a transmission substation. Image credit: iStock
But security experts say this test shows that the bad guys attacking power companies may come in all shapes and sizes, not just other governments trying to control the grid, but also lower level crooks with fewer resources.
The U.S. requires power companies to work to protect themselves from cyber criminals and spies.
Inside Job
Thieves are stealing not just phones, but phone numbers — leaving you out of luck.
They’ll use them to do things like break into your accounts, intercepting the security messages from your bank or social media.
How do they do it?
Thieves used to call up your phone company and pretend to be you, asking to get your number changed over to them.
Now we’re learning that thieves have stepped up their game by paying phone company employees to steal your number.
Motherboard reports that thieves often look through social media sites like LinkedIn and Reddit to contact people working for phone companies, in some cases, offering them a hundred bucks for each number they help steal.
Reports say crooks look up phone company employees on social media & try to convince them to steal numbers. Image credit: LinkedIn
Deputies in Florida say surveillance of a group of phone number thieves shows the crooks routinely pay workers to grab numbers for them, according to Krebs on Security.
One number hijacker talked about the phone company workers to Motherboard, saying, “Everyone uses them. When you tell someone they can make money, they do it.”
The number stealing scheme is also called a port-out scam.
Instagram Hack
A hack on Instagram brought actress Nikki Blonksy to tears this weekend.
“Guys, I just want to let you know I’ve been hacked,” she said in an Instagram video later posted on Twitter.
The Hairspray star says someone broke in to her account and wrote terrible things about people.
“Calling them horrible things, being racist, being mean about gays,” she said.
We don’t know how hackers got in to her account, but it’s a good reminder to get better at protecting yourself online.
—Use a long password for your accounts. Try for 15 characters.
—Use a password manager to keep track of your passwords.
—Use two-factor authentication, where you type in your password and then get a code on your phone, or use both your password and a physical key.
—Update your phone and computer as soon as updates come in.
“I am heartbroken. I am sick,” sobbed Blonsky in the video.
Follow those security steps to help you avoid feeling heartbroken, sick and under pressure from your family who may be watching you go live with your emotional apology on Instagram.
“Wipe the black under your eyes,” said an annoyed-sounding person off-camera in Blonsky’s video. “Stop crying!”
See other scam alerts:
Scam Alert #25 — Gang arrests & cities under attack
Scam Alert #24 — Car sharing crooks & hackers in the control room
Scam Alert #23 — Hacking the military & a security bra

