Out for revenge? You’re leaving digital tracks
- July 7, 2017
- Posted by:
- Categories: Archer News, Cyber Crime, Posts with image, Smart Devices

Former employees try to make their companies pay, but get prison time instead.
He was fired. He was angry. He wanted to mess with the guy at work who’d ticked him off.
Court documents show how the former employee’s attack on his company systems went down.
“Coming home drinking a few beers,” Adam Flanagan told investigators. “Loggin’ in, saying, ‘These mother f—kers.’”
Flanagan was a field engineer at a company that helped gather the readings from people’s smart water meters at their homes.

An example of a smart water meter. Image credit: Neptune
He installed base stations that use radio signals to collect the meter info on how much water you use and send it along to the utility so you can get your bill.
Suddenly, a few weeks after he was fired, base stations stopped working correctly.
The problems continued for months, affecting people in Pennsylvania, where Flanagan lives, as well as New Jersey and Maine, prosecutors said.
Somebody got into the computer system and caused havoc.
“I know I wasn’t supposed to be there,” Flanagan said in an interview with FBI agents that was secretly recorded. “I was doing it more to just be a d–khead.”

An example of a smart water meter base station. Image credit: Sensus
“Below expectations”
Flanagan worked at the company — which is not named in court filings — since 2007.
But in his 2013 annual review, he received a “below expectations” rating, according to the documents. After an unsuccessful performance plan, he was let go in November of that year.
In December, the problems began at some of the very same base stations that Flanagan installed, his indictment said.
The base stations could no longer communicate.
Passwords were changed, one of them to “f—k you.”
The water companies had to send out employees to read water meters in person, just like the days of old.
The company where Flanagan worked launched an investigation to find out who was attacking, and how to stop them.
All this cost money — extra hours for workers, a crisis for management, time and money spent on finding and repairing the damage. And who will pay?

An example of what the inside of a smart water meter base station can look like. Image credit: Sensus
How he got back in
While he was still employed at the company, he had a special program on his home computer so he could work on the base stations from home, he told investigators.
“It was on my computer when they let me go,” Flanagan said. “It was still there.”
After he was fired, he used the program to connect to the base stations, he said.
Not just connect. It turns out he could still get in.
“You know, I was just going in there ’cause like I was pissed,” he said. “I was extremely angry.”
He said he put up a pirate picture online and changed a few things.
“I may have changed the password to ‘f—k you’ on a couple of them,” Flanagan said. “Stupid s–t like that.”
“I was just banging it in there,” he explained. “I am honestly at fault, but, yeah, it was nothing to be, I don’t want to say it wasn’t being malicious but it wasn’t anything to, you know, take down a network…”
Excerpt of conversation between Adam Flanagan (AF) and an investigator (AP) from court documents.
Prison time
But prosecutors saw it differently.
Flanagan was indicted, charged with intentionally causing unauthorized damage to a protected computer.
He eventually plead guilty to two counts of intentionally accessing a protected computer without authorization and thereby recklessly causing damage.
A judge just sentenced him to one year and one day in prison.
Tracking you
Maybe Flanagan did not know that many companies track who signs onto their computers and when. Maybe he knew, but the “few beers” clouded his mind.
Either way, he left clues behind.
Other companies should be ready to capture those kinds of clues to stop attacks, said Slade Griffin with cybersecurity company Contextual Security.
“You’ve just got to know what’s going on on your network,” Griffin said. “If you have collected good data on who has logged in from where and at what time, you can begin a trail of evidence.”
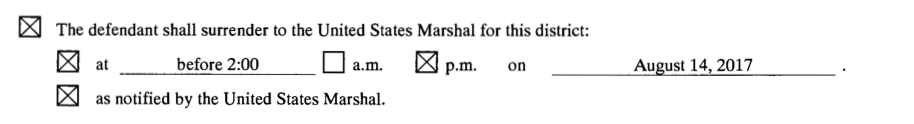
Adam Flanagan’s sentencing document provides a date to turn himself in for imprisonment.
Mistakes
Once you collect the data, keep it in a safe place for up to a year, Griffin recommended.
“This will allow for an investigation if a breach is discovered at a later time,” he said.
Know who has access to each system, he added, and make sure they can’t get in when they leave.
“HR [human resources] should develop a process for tracking what systems people will need access to and initiate a credential change when someone is terminated,” said Griffin.
Plus, change those default passwords, the ones that come on the devices.
And make sure you have multi-factor authentication, not just a username and password.
“Those devices are on the Internet. Anybody could have done this,” Griffin said. “As long as you’re only using a username and password, then your security is based on the strength of the password. And that’s not good.”
We don’t know if the nameless company failed to do all these things, allowing Flanagan full access to stuff he wanted to vandalize.
If they didn’t before, they’re probably doing it now.
Adam Flanagan told investigators that his employer did not remove a special program from his home computer that allowed him access to devices, according to court documents.
Trending?
Flanagan is not the only former employee trying to take digital revenge.
In February, the former IT specialist for a Georgia Pacific paper mill in Louisiana was sentenced to prison for hacking into the mill’s computer system and doing more than a million dollars in damage.
In March, Columbia Sportswear launched a suit against a former IT worker who it says hacked executives’ e-mail for more than two years to try to drum up work for his new boss.
In May, the courts decided a former security guard in California had to pay more than $300,000 after he illegally padded his paycheck while working and then defaced the company’s website after he left the job.

A former employee sabotaged a paper mill that made products like Brawny paper towels. Photo credit: JeepersMedia via Foter.com / CC BY
Who will pay?
Archer News contacted the attorney listed for Flanagan in court documents.
Douglas P. Earl of Philadelphia did not respond to our messages.
But we did get an answer to the question about who will pay for the cost of the crime and the company’s efforts to find out how to stop it.
The judge ordered Flanagan to hand over $40,000 in restitution.
He pleaded guilty in June, and has to report for prison by August 14.
He’ll pay while he’s behind bars, if he’s earning any wages, and he’ll pay $500 a month when he gets out, according to the sentencing document.
He’ll also have to “refrain from excessive use of alcohol” while he is under supervision for three years after prison.
His mission — “just to f—k with them” after an ugly breakup — became a very expensive one. And he’ll be paying —not just financially — for the rest of his life.
