Restoring your files “the nasty way” & other new ransomware tactics
- December 14, 2016
- Posted by:
- Categories: Archer News, Cyber Crime, Posts with image, Ransomware
How cyber crooks are trying to get you to pay, through guilt, honor & fear.
“Heck, no, I won’t pay!’ you say as you see the ransom note appear on your screen.
But cyber criminals are finding new ways to trick you into giving them money for unlocking your files.
One of the latest tactics—giving you the “nasty” option.
A ransomware called “Popcorn Time” takes over your digital data, and demands you pay up, according to Lawrence Abrams of BleepingComputer.
The “fast and easy way,” the ransom note tells you, is to transfer 1.0 bitcoin—about $775—to the hostage-takers’ wallet address.
And the “nasty way”?
“Send the link below to two other people,” the note says. “If two or more people will install this file and pay, we will decrypt your files for free.”
In other words, sell out your friends—or enemies—and the thieves promise they’ll give you your files back.
It’s a “move that sets a new level of scumbaggery,” Abrams wrote.

The “Popcorn TIme” ransomware—not related to the Popcorn Time movie & TV show streaming service—offers you a chance to pay off your ransom by infecting two other people, according to BleepingComputer.
Guilt factor
You may refuse to infect a friend. You are an honorable person, after all. You’d rather pay than hurt someone else.
And the crooks add in another layer of guilt.
They claim they are a group of computer science students from Syria, just trying to survive a country riddled by war, BleepingComputer.com shows.
One malware author lost his parents and little sister in 2015 and others on the “team” have also lost family members, he or she writes.
“Be perfectly sure that all the money we get goes to food, medicine, shelter for our people,” the author says. “We are extremely sorry that we forcing you to pay but that’s the only way to keep living.”
You don’t actually know if the cyber crooks are from Syria, from Chicago, or from the house down your block. But you might be more willing to fork over digital cash if you thought your money went to a good cause.
Still not convinced? The group turns to traditional tactics as well.
“Please don’t try to be smart, anything other than payment will cause damage to your files and your files will be lost forever!!!!” the ransom note says.

The ransomware authors try to encourage victims to pay by claiming they are victims, too—of the violence in Syria. Photo credit: Beshr Abdulhadi via Foter.com / CC BY
Personal service?
Another kind of ransomware appeared to offer you a concierge service—a real person you could call for help.
“Yes, it is a live person,” Jerome Segura with Malwarebytes said to Archer News. “But the customer service is not great if you start asking too many questions!”
It looked like someone was combining ransomware with the old tech support scam boiler rooms overseas, he said in a post.
In the past, tech support scammers called you up to tell you your computers is broken, or pretended to lock your screen and offered you a number to call. With the “VindowsLocker” ransomware, it appeared that the digital lock-up could be real, Segura said.
Segura later updated his post to say the VindowsLocker ransomware may be a hoax.
But he said the number posted on the ransom note did indeed lead to tech support scammers who were “actually happy to bypass their usual fake diagnosis and go straight to ask for money to get the files back.”
“We have seen many different ransomware including some that truly looked like jokes but were actually real,” he wrote. “Cracking ransomware takes time and one cannot always wait for reports of victims who are in desperate need of a decryption tool.”
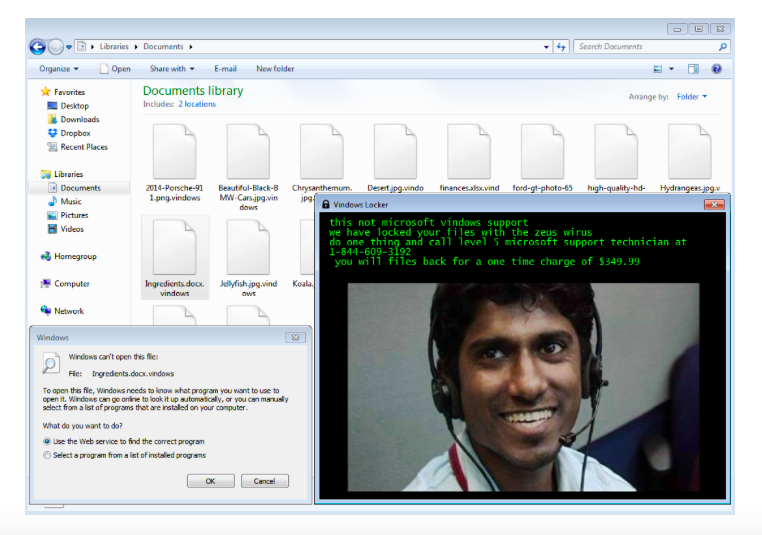
Image of “VIndowsLocker” ransomware. Courtesy: Jerome Segura
Sneaky strategies
Joke or not, you can learn from the sneaky strategies of these kinds of programs.
They may hitch a ride on another app or program, Segura said.
You might unknowingly agree to downloading the hitchhiker as well, as you quickly move through the install process for a program you want.
“By swiftly clicking through an installation, it’s easy to miss the fine print and ‘agree’ to these extra applications,” Malwarebytes said in a post about “PUPs”—potentially unwanted programs.
Watch out for signs of trouble while using the install wizard, the series of instructions that help you download n application or program, the post said.
—Read the information in the top navigation bar of the install wizard to catch names of unwanted programs.
—Do not accept standard, express, default, or other installation settings that are recommended. Always choose custom.
—Install wizards may call this out as “advanced” in parentheses but that’s actually a dark pattern [a shady strategy]. Custom settings are not advanced.
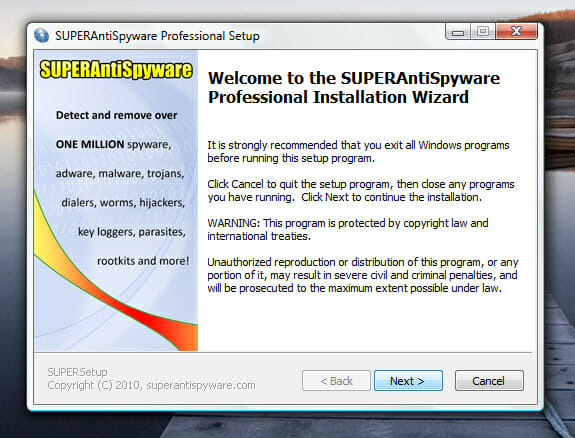
An example of an install wizard. Malwarebytes recommends you check install wizards carefully to make sure there are no extra programs included. Photo credit: digitpedia via Foter.com / CC BY
EULA
You may also find signs of that sneaky program in the end-user license agreement, or EULA, according to Malwarebytes.
“Don’t accept terms of use that are for bundled programs,” the post said. “Read the top title above the fine print to be sure the EULA you are accepting is only for the program you originally downloaded. If it isn’t, you can decline and still move forward in the install process.”
Macros
Some ransomware programs can jump onto your computer through malvertising. Others come in through your inbox.
Microsoft posted a warning today about fake credit card company e-mails that try to trick you into downloading ransomware.
The faux MasterCard message says you will be billed $208.35 unless you move to stop it.
“Go through the attachment to avoid it. Password is 4555,” the e-mail says.
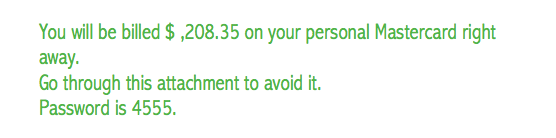
A fake MasterCard e-mail tells you that you will be billed if you do not follow instructions.
“Urgency—by stating that the recipient is being billed, the attack emails can trick unsuspecting users into opening the malicious attachment without consideration for their safety,” Microsoft noted..
The fake message shows you “well-formatted and well-written” instructions, supposedly from Microsoft, that tell you how to “enable macros” so you can see the information you need.
But if you enable macros, the e-mail then downloads ransomware onto your computer, the real Microsoft said.
“…[B]e mindful of documents that instruct you to enable macros—it’s very possible that they contain malicious macros,” Microsoft said.
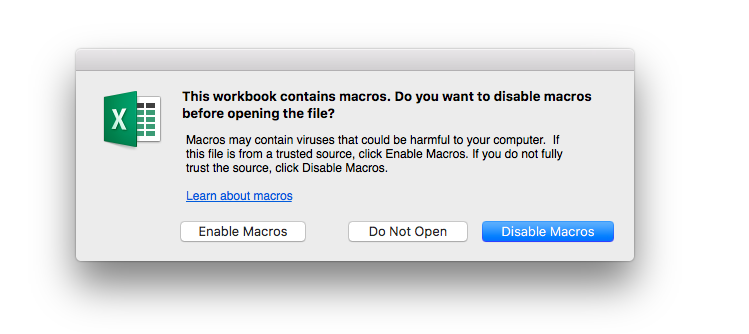
Microsoft warns people about enabling macros because it could expose you to viruses.
Unlocking ransomware
If it happens to you, you can check places like No More Ransom for some decryption keys. But not every piece of ransomware has a free key.
A sheriff’s department in Arkansas just paid $2,400 to get its files back, and a county in Indiana reportedly paid $21,000.
A Pennsylvania prosecutor’s office paid $1,400 in ransom, and a hospital in California paid $17,000.
The ransomware business may rake in $1 billion this year. And next year?
Ransomware “will remain king” in 2017, Malwarebytes said.
That means you’ll need to keep up the fight against guilt, fear and urgency—and any other new tactics cyber crooks
