Not your dad’s Nigeria scam
- November 22, 2016
- Posted by:
- Categories: Archer News, Posts with image
Scammers change their tactics to get your money—and succeed.
You could spot a Nigeria scam if you saw one, right?
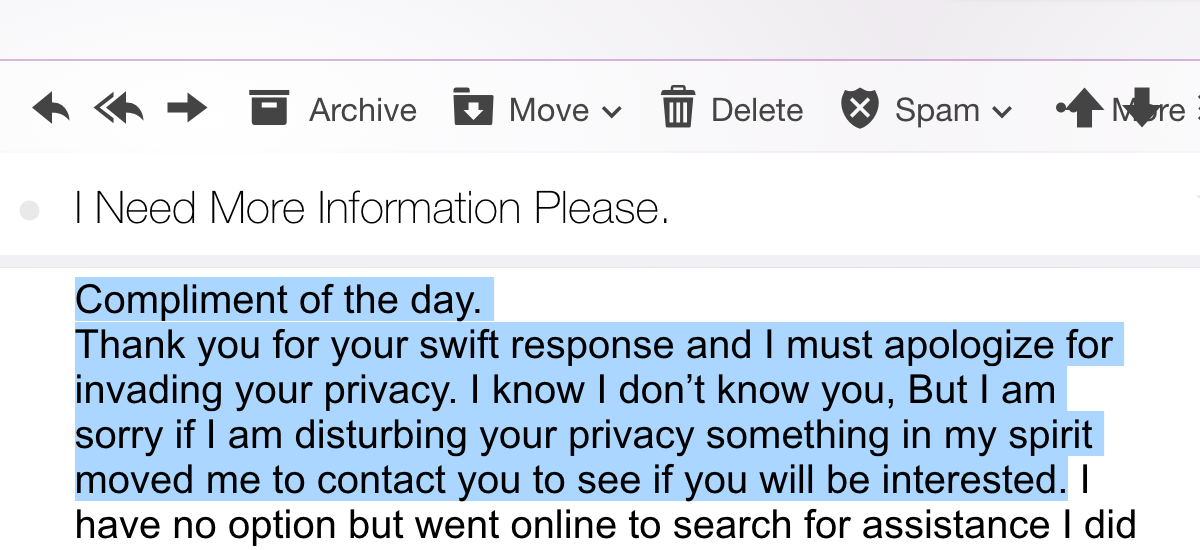
Take this suspicious e-mail that showed up in my inbox this month:
“I work with the Hang Seng Bank. There is a sum of $19,500,000.00 in my Bank. There were no beneficiaries stated concerning these funds which mean no one would ever come to claim it,” the e-mailer wrote.
“This is a deal which I cannot handle alone at this point of time,” he continued. “I intend to give you 30% of the total funds as compensation for your assistance.”
So gracious! And so fake—a traditional Nigeria-style scam, like the millions that have come in through mail, faxes and now e-mail since the 1980’s.
But investigators say Nigerian scammers have changed their style and strategy in the last two years, dodging detection and stealing millions of dollars from people and businesses around the world.
They’re more sophisticated, harder to spot, and have claimed thousands of new victims with millions of dollars in losses, according to researchers at Palo Alto Networks Unit 42.
“Through our analysis, it has become clear that Nigerian cyber actors have demonstrated significant growth in size, scope and capability over the past two years,” Peter Renals and Simon Conant said in their “SilverTerrier” report.
Excerpt of traditional Nigeria scam e-mail.
What are they doing now?
The next Nigerian scam e-mail you receive probably won’t ask for your help transferring millions out of the country, according to information in the report.
It will more likely look like an e-mail from a delivery company, telling you that you have a package on its way.
Or a message from your bank, telling you there is a problem with a transfer or refund.
Or an alert from law enforcement, with “important” information about you.
In May, scammers sent out e-mails with the subject “Warning from the FBI” and an attachment called “Your File,” which actually contained malware, the report said.
Nigerian cyber crooks may then use the malware to take over your computer remotely or steal your information, which they then use to rip you off or trick other people into thinking they are you, researchers said.

Scammers show off the results of their schemes on Facebook. Image from Palo Alto Networks Unit 42 SilverTerrier report.
In the office
You may also get a Nigerian scam e-mail at work.
It could come in from a new customer, from an old customer, or even from your boss.
The scammers are taking over people’s accounts, creating fake accounts that look very similar to real ones, or simply setting up fake companies and charities online, according to researchers.
The e-mails and websites are no longer riddled with spelling mistakes and odd sentence structure—easy to spot as scams, the report said.
“Early attempts by the actors to develop these websites often included grammatical errors and clunky interfaces that led average computer users to question the nature of the websites,” the report said. “Modern versions now demonstrate an enhanced level of web design proficiency and project a more professional appearance.”
Fake sites
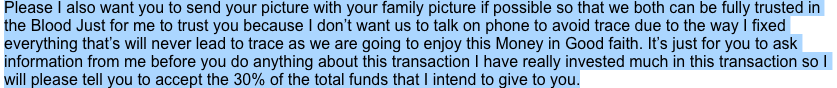
The report shows a site for “KA Equipments,” with a crisp homepage, well-written descriptions, a map of London, and bios and pictures for team leaders.
But the homepage appears to be stolen, an almost exact copy of Jhump and Associates’ site, a business development, equipment and services company based in Texas.
KA Equipments is part of the Nigerian scam network, according to the report.

Website for “KA Equipments.” Image from Palo Alto Networks Unit 42 SilverTerrier report.
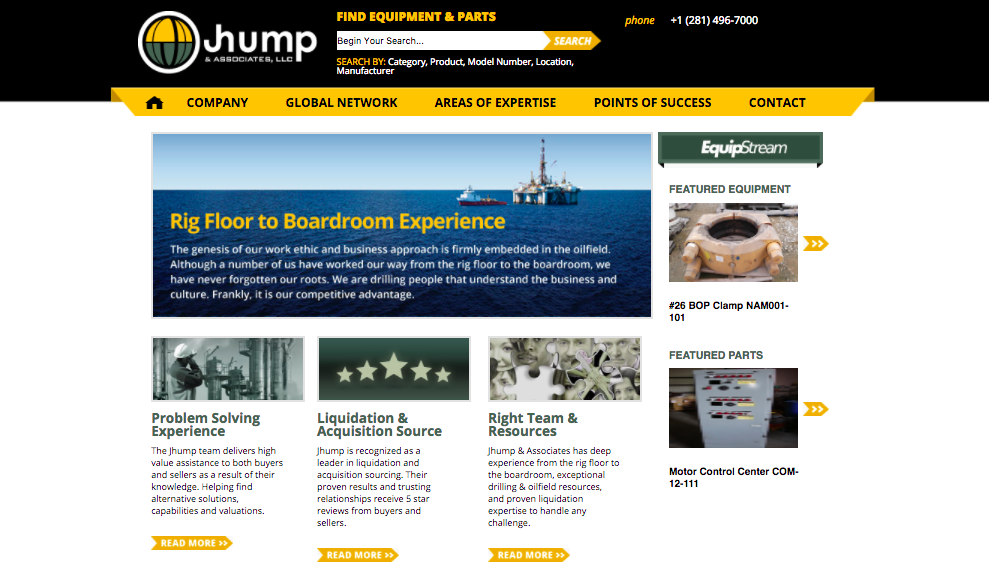
Website for Jhump & Associates in Texas.
The report shows another fake site for a charity called Vintage Orphanage International, which claims to help abandoned children.
Some of the images show real orphans around the world. But the donations page says it is under construction, and tells people to donate through Western Union or MoneyGram.

Website for “Vintage Orphanage International.” Image from Palo Alto Networks Unit 42 SilverTerrier report.
Other sites choose domain names very similar to real ones, or just one letter off, for example using “Samsrung” instead of “Samsung,” according to researchers.
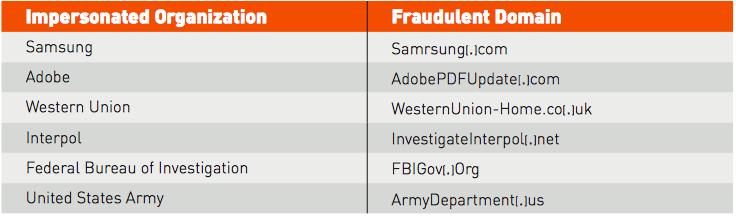
List of real organizations & the fake domains scammers use to impersonate them. Image from Palo Alto Networks Unit 42 SilverTerrier report.
What do they want?
The e-mail to your work account may be an invoice, a purchase order, a request for a quote, or a new order entirely, researchers noted.
And in many cases, it works.
City officials in El Paso, Texas confessed at the beginning of November to sending more than $3 million to scammers who sent them fake invoices for a streetcar project.
This kind of fraud is also called the BEC scam, standing for Business E-mail Compromise, and CEO fraud.
INTERPOL announced in August it had helped arrest a NIgerian scam mastermind by the name of “Mike,” who allegedly stole $60 million dollars from people in small to medium businesses in the U.S. and around the world.
“Our research shows that high tech, higher education, manufacturing, healthcare and construction are all targets of these modern, sophisticated ‘Nigerian scams,’” Ryan Olson, intelligence director of Palo Alto Networks Unit 42, told Archer News.
New generations
New generations are joining those who ran the more traditional “Nigeria scam” letters and e-mails, bringing new technology skills to the old scheme.
“The younger generations represent those graduating fresh out of the universities, who are beginning their criminal careers with malware, while building off the scamming techniques developed by the older generation,” the report said. “Together, these groups are blending their tools and techniques to achieve their goals.”
The scammers may flaunt their ill-gotten wealth openly on social media, even linking their Facebook pages with people in local law enforcement and community religious leaders, according to the investigators.
“Scams, fraud and corruption are viewed as a way of life, and as a result, the majority of these actors apply little effort toward maintaining anonymity,” the report said.

Lagos is the largest city in Nigeria. Photo credit: boellstiftung via Foter.com / CC BY-SA
Nigeria
Nigeria is aware of the problem.
An editorial in Nigerian newspaper THISDAY on November 7 said the country’s 2015 Cybercrimes Act has not stopped the country from reigning as a breeding ground of cybercrime activity.
“But like almost every law in the country, there is the problem of enforcement,” the editorial said. “The ‘yahoo boys’ still daily throng cybercafé premises to ‘transact’ their business with the owners looking away. Yet the law criminalises internet café owners who allow their premises to be used to commit online crimes.”
The country’s minister of communications is calling for change, according to the editorial.
“If African leaders failed to address this threat, there will be negative impacts on economic growth, foreign investment and security,” Minister Adebayo Shittu said.

Nigeria’s minister of communications, Adebayo Shittu. Photo credit: ITU Pictures via Foter.com / CC BY
What can you do?
These kinds of scams will likely continue.
“One of many scams going on today,” said Jerry Humphreys, president and CEO of Jhump & Associates, whose site was copied for use by Nigerian scammers. “A shame, but part of the world we live in now days.”
Basic advice still applies, Olson told Archer News—don’t click on suspicious links, keep your systems and devices up-to-date, and run security on them.
But you can do more.
The report said people who answer the “info@____” kind of e-mails should learn about the modern Nigerian scams and be trained in how to stop the tricksters.
People who work in sales functions with new customers should also be ready.
Experts suggest setting up a multi-step process to make sure an order or directive is real before sending money. For example, don’t answer the e-mail or call the number listed, but instead dial the real number and verify by phone before making a payment.
“The best defense against these evolving threats is a security posture that favors prevention,” said Olson.
