Your meat may be vulnerable, researcher says
- April 17, 2017
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Hacking, Industrial Control System Security, Posts with image, Vulnerabilities

Investigation finds vulnerabilities in the machines that process beef, chicken, fish & other foods.
Enjoying that burger, that drumstick, that salmon filet?
There’s a chance it was processed by equipment from Marel.
Iceland-based Marel calls itself the “leading global provider of advanced processing systems and services to the Poultry, Meat and Fish industries.”
Potatoes, vegetables and meat substitutes are also on the company’s menu.
But new research shows that some of those food processing systems could have major security holes, allowing crooks, thieves and spies in to mess with your meat.
“These vulnerabilities impact the systems that produce the food we eat,” said Daniel Lance, a security researcher who also works for Archer Security Group (the parent company of Archer News). “They should be thought of as critical.”

An example of the kind of food weighing systems Marel produces. Image credit: Marel
Meat production is no longer just a butcher hacking away at a carcass.
Now meat processors use advanced, computer-connected equipment.
Unfortunately, that equipment may be hackable, too.
“In the case of a large-scale attack, these vulnerabilities could devastate a majority of the protein industry that are relying on these systems,” Lance said.
“You could see massive price fluctuations in the market and wide-scale product shortages,” he explained.
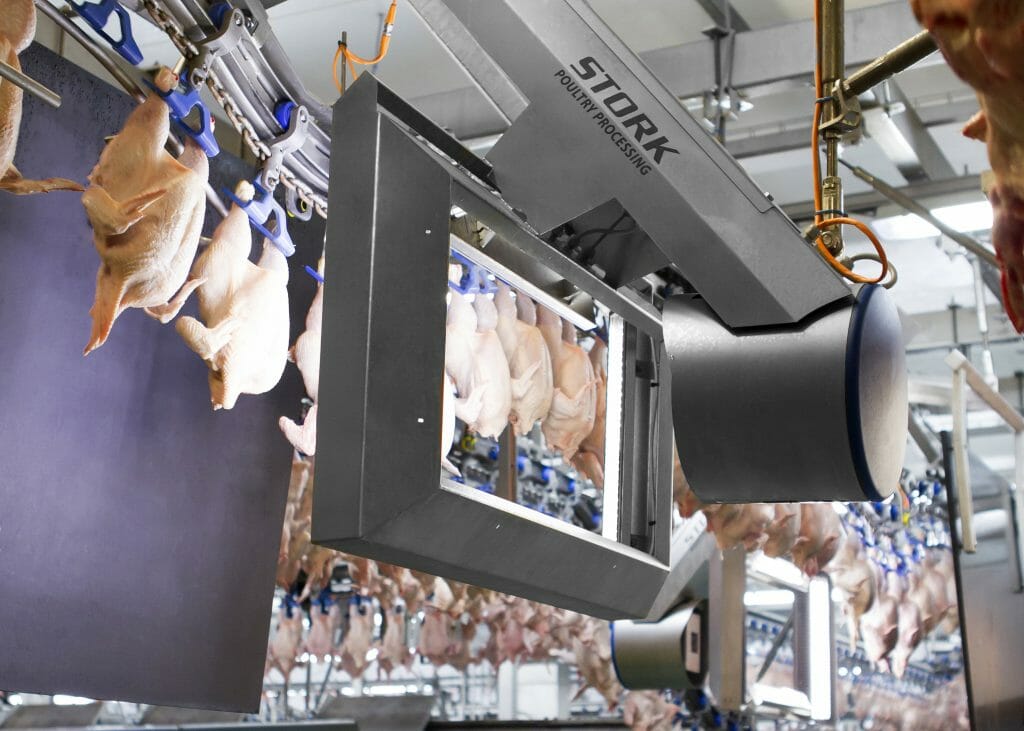
An example of Marel meat-processing equipment. Image credit: Marel
What is the problem?
A group called ICS-CERT in the Department of Homeland Security put out an advisory about the security holes Lance discovered to warn people and companies using Marel’s equipment.
The Industrial Control Systems Cyber Emergency Response Team advisory said some Marel machines have hard-coded passwords, which means the person or company using them doesn’t have the ability to change them.
That also means the bad guys can get in.
“If hard-coded passwords are used, it is almost certain that malicious users will gain access through the account in question,” the non-profit research and development group MITRE said about the weakness.
The likelihood of exploit is “very high,” according to MITRE.
It doesn’t take much skill to do it, the ICS-CERT advisory noted.
And someone could do it from their iPhone, Lance said.
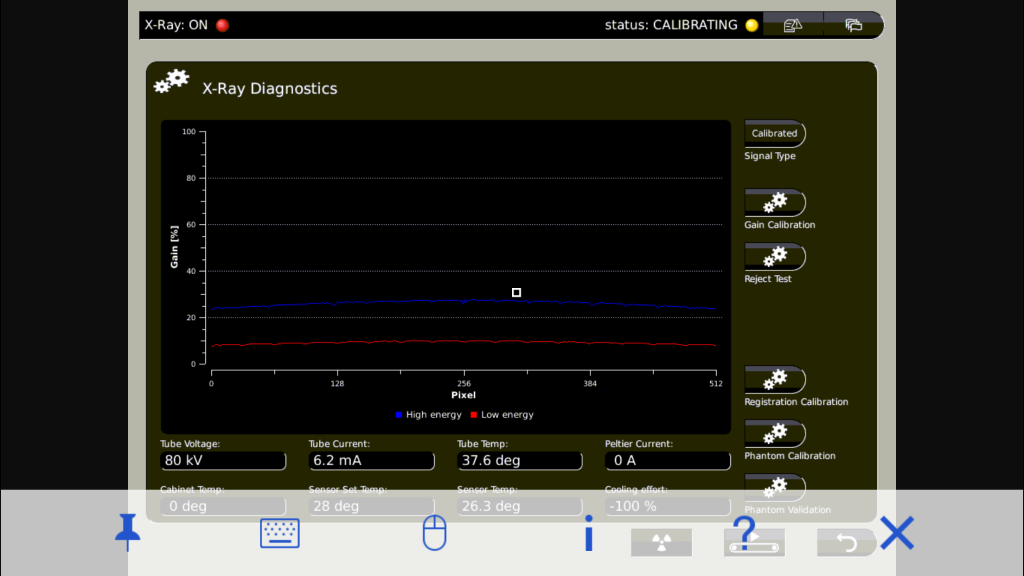
Vulnerability analysis showing an iPhone connecting to Marel equipment. The image is provided with the knowledge of the affected processor in collaboration with an affected food processor during a vulnerability analysis by Daniel Lance. Image credit: Daniel Lance
Spy, cheat & destroy
Once they’re in, they can upload new, malicious things onto the equipment and control it remotely, the advisory said.
What could they do then?
Spy, cheat and destroy, Lance said, with varying levels of damage.
“Food processors might use these vulnerabilities to gain information about their competition,” he said.
One at a time
Some hacks might be smaller, perhaps just to mess with one company at a time.
Someone could change with the software that catches overweight or underweight chicken packages, Lance said.
You could end up with more chicken bones in food that’s supposed to be boneless, and the company could end up with a big headache.

Chicken nugget. Image via Pixabay
Another example from Lance shows how cheaters could hurt a company by changing the fat analysis on machines producing ground beef.
If a company is selling beef that is 80% meat and 20% fat, the crooks could change the machine to turn out meat that is actually 90% meat and 10% fat.
It may not sound like a big deal, but “’lean’ is money in that industry,” Lance said.
“If the problem went on unnoticed, this could have a significant financial impact on the producer,” he added.

“‘Lean is money in that industry,” security researcher Daniel Lance said. Image via Pixabay
Shortages?
It’s not just one company at risk.
The issue is much larger, according to Lance.
Especially if you want to continue eating that burger, drumstick or salmon filet.
“Because of how vulnerable these systems are, a weaponized attack that destroyed the programming or the ability to program these systems could lead to a major shortage of many products, particularly chicken, beef and fish,” he said.

An example of a Marel meat-cutting line. Image credit: Marel
Fixing the problems
The researcher said he contacted Marel through ICS-CERT so the company could fix the problems.
“At first the collaboration was going well,” Lance said. “The feedback I was receiving from ICS-CERT indicated they were willing to work on this and make improvements.”
Lance worked with Marel for a while through ICS-CERT to identify the issues and show how they could be misused.
But then the conversation stopped.
“The vendor [Marel] did verify with ICS-CERT that they did in fact have critical issues,” Lance said. “Unfortunately, that’s about where the collaboration ended.”
“ICS-CERT informed me that the contact they had been working with was no longer collaborating,” he said. “And any further attempts at contacting the company had also failed.”

Marel headquarters in Iceland. Image credit: Marel
Still open
Archer News contacted Marel as well.
But the company did not respond to our questions about the vulnerabilities.
The security gaps are still open, according to ICS-CERT.
“Marel has not produced an update to mitigate these vulnerabilities,” the advisory said.
What next?
What would you do if you knew about an open security hole in food machines around the world?
Keep it quiet, so as not to tip off the criminal hackers? Or let the world know, tipping off hackers, but also giving people a chance to protect their machines?
“The responsibility to disclose a vulnerability that has not been patched is always a difficult moral burden,” Lance said.
He said he worked with ICS-CERT to find the best path forward.
“In the end, we decided together that informing the end user would take priority in this very special instance,” he said.

ICS-CERT warns companies using affected Marel food processing equipment to take steps to protect themselves. Image credit: Pixabay
Meat for your meals
So far, ICS-CERT does not know of any criminal hacking cases involving the Marel machines, the advisory said.
But the group warned companies to take steps to protect themselves, including checking traffic logs for signs of trouble, keeping control systems and devices away from the Internet, and using VPNs if they need to access the machines from afar.
You can see more recommendations here, along with a list of the affected Marel systems.
You may not have known that companies rely on things like check bin graders, speed batchers and SensorX23s to bring you the meat for your meals.
But now you know some of those machines from “leading global provider of advanced processing systems and services to the Poultry, Meat and Fish industries” can be hacked, like your laptop and your phone.
Let’s hope the criminals like their protein, too, and leave the meat supply alone.
Main image: grilled steak. Photo credit: Foter.com
