How NOT to do security at a power plant
- November 19, 2020
- Posted by:
- Categories: Archer News, Cyber Crime, Cyber Crime, Cyberattack, Cyberattack, Industrial Control System Security, Posts with image, Power Grid, Power Grid, Security Management
You’ve heard of cybersecurity best practices. Here are some of the worst practices — seemingly small, often overlooked, but carrying big risks.
They turn up at plants and factories, as well as organizations of every kind.
Watch here:
You Had One Job
“You had one job” memes can be funny. We love to chuckle at people making silly work mistakes.
But what if that one job was doing security at a power plant? The results can be serious.
We talked to a cybersecurity expert about cybersecurity worst practices — some of the smaller, overlooked issues that can lead to major consequences in plants and factories and other places.
1: Useless Security
First mistake, doing “useless security.”
“It is the idea of doing the least amount of work possible just to get past,” said cybersecurity professional Dave Foose with Emerson.
Foose has seen a lot of security mistakes at plants around the world. Among them, putting in security that doesn’t really work.
He can’t show you real-life pictures of these errors in sensitive industrial areas, but some social media images can illustrate. For example, a security camera pointed directly toward a wall.
“The idea is that you are doing ‘checkbox security’ at that point,” he said to Archer News. “I did the thing you asked me to do and it’s installed, but it’s not effectively doing what you think it is.”

2: Not Verifying
Second mistake, not verifying. You put in what seems like effective security, but don’t check to see if it’s actually working.
For example: a locked door where people have posted the security code. You might as well leave the door unlocked.
Experts recommend you help people using the security measures understand the risks and help them get what they need. Otherwise, you may think you’re covered, but you’re not.
“You may stop worrying about that risk and it may become more detrimental to everybody at that point,” Foose explained.

3: No Walk-through
Worst-practice security includes not taking a walk through the area to see if there’s anything out of place.
“If you’re not actively walking around to make sure everything is fine, there could be stuff lurking you’re not watching,” Foose said.
One plant found a secret Internet cable plugged into their control systems — a cable that had been there for more than five years, allowing attackers a free and easy way in, according to Foose.
“This is a power generation facility, somewhere in the world — who had, for years, no monitoring, no watching — was connected to the Internet,” he said.
That’s perfect for attackers who want to invade the power grid, like some did in Ukraine in 2015 and 2016, shutting off electricity in the middle of winter.
It’s not just power plants. In one famous case, people found hidden laptops and other small devices found at eight banks in Eastern Europe in 2018. Attackers pretending to be couriers and job seekers had planted them inside and stole more than $10 million.

The wayward generation facility cable means attackers could already be could be buried deep inside the plant systems. Foose said you’d have to do an extreme search to see if the plant’s infected.
“You might as well just throw a Molotov cocktail behind your shoulder, blow it up, and build an identical plant next door to be sure,” he joked.
4: Automation Only
Final worst practice— relying on automation only.
Back in the big 2013 hack, Target assumed their automated alerts would keep them informed, according to Bloomberg Business. But the company learned too late that attackers had raided their computers.
“The problem is that they had systems already set up to alert them, but no one was really actively looking at that system right away,” Foose said.
“Don’t forget the humans, even though they can do things you don’t want to them to. They are still your best tool,” he added.
Best Practices
Security is not an easy job. But Foose recommends people pay attention to these easy-to-make errors. In summary:
1: Useless Security Useful Security
Make sure you’re not just checking a box.
2: Not Verifying Verify
Make sure it’s actually working and people are using it the right way. Help people understand why a security measure is in place and help them get what they need.
3: No Walk-though Do walk-throughs
Walk around and check for things out of place, like unusual cables and devices.
4: Automation Only Include Humans
Don’t rely on automation to do everything. You still need people in the process.
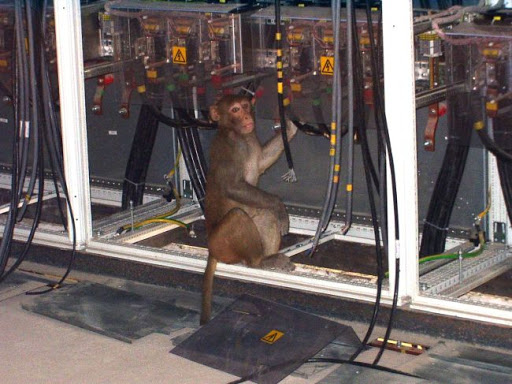
Main image: Monkey in cables. Image: Imgflip
