Crooks bombarding businesses with 360% more ransomware, report says
- August 8, 2019
- Posted by:
- Categories: Archer News, Cyber Crime, Posts with image, Power Grid, Ransomware
The chances of you clicking on ransomware at work — and freezing your company’s computers — are going up.
Here’s why.
Watch here:
Growing Target
A new report released today by Malwarebytes says the security company detected 363% more business ransomware this year compared to the same time last year.
Meanwhile, the numbers for people on home computers — once the main target — are going down.
“It’s a better return on investment. Bad guys go out to where the money is,” said Adam Kujawa, director of Malwarebytes Labs. “The amount that you can ransom a regular person, a consumer, is going to be far less than a company.”
Better Tools
Attackers now have better ways of spreading their weapon, Kujawa said in an interview with Archer News.
“When you’re able to infect, let’s say, 80% of all the systems on a network, a business network, and then in your last payload drop is ransomware, suddenly you’ve ransomed 80% of a company in a single click,” Kujawa explained.
That gives attackers more leverage and more control.
In addition, cyber crooks are using more “wiper” ransomware that can actually destroy data — rather than just encrypting it — and systems, according to another report released this week.
IBM’s X-Force says it saw a 200% increase in destructive malware cases — including ransomware — in the first half of this year compared to the second half of last year.
Schools, Hospitals, Cities
It’s not just businesses.
It’s anywhere that needs computers to operate, like schools in New York, Oklahoma and New Mexico — just in the last month.
A malware attack is also delaying the start of school in a district in Alabama, as well as registration and testing in some Louisiana schools, where the governor declared a state of emergency.

Downtown
Data hostage takers are focusing on cities, too, like Albany, Baltimore, Atlanta, Riviera Beach and Lake City in Florida.
“There’s some easy prey that are out there,” said Todd Weller, chief strategy officer of Bandura Cyber.
That could affect essential services you need.
For example, water pump stations went down in a ransomware attack against the city of Riviera Beach, Florida, in June, according to news reports.
After a ransomware siege on the city computers in Johannesburg, South Africa, in July, customers could not buy electricity and as a result, lost power.
Easy Prey
Some schools and governments need to do a better job of backing up their data, Weller told Archer News.
If attackers encrypt your data and hold it for ransom, you can restore your data from backups without paying the money.
“Make an investment in backing up your data,” Weller said. “Then there’s nothing to really hold hostage, right? You minimize the amount of data that you’re not able to get back.”
“I think that would be the big game changer,” he added. “And it’s not hard.”
But some cities and businesses are paying the ransom, showing that they are likely not backing up their data properly.
Why not?
“I couldn’t tell you,” Weller answered. “It’s amazing to me. I don’t understand why you just don’t patch and back up your data.”
Overwhelmed
Schools and governments often have less money and staff to focus on cybersecurity.
And keeping cyber attackers out can be difficult.
“It’s a challenge to be good,” Weller said. “It’s an unrelenting, never-ending arms race between attackers and defenders.”
What can schools, cities and businesses do?
Experts say to focus on the basics, including:
—Back up your data
—Update or patch software & systems
—Training employees on phishing email awareness
—Outsource your security if you don’t have enough staff
—Consider moving your data to the cloud, so you can rely on the security of big cloud companies instead of your own.
Make a Plan
In addition, plan for the attack, Kujawa said.
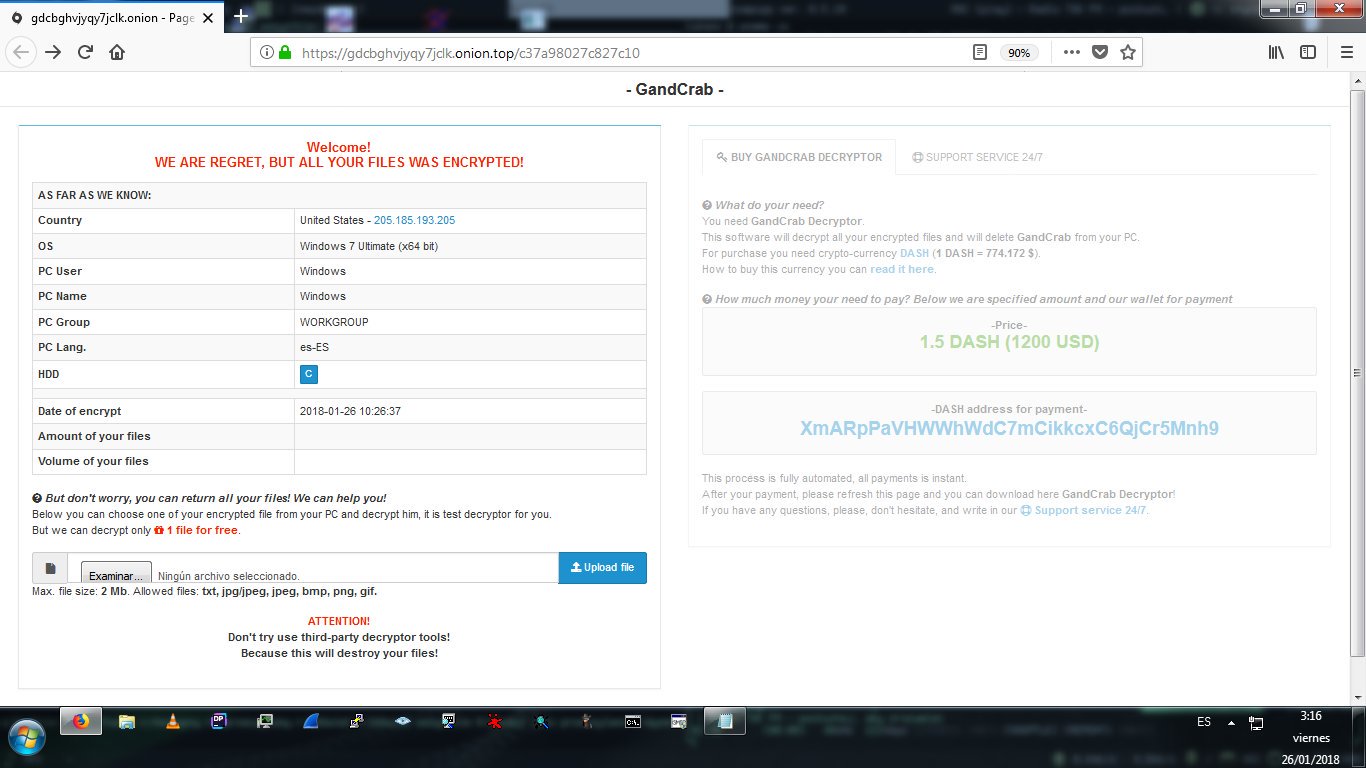
Find out exactly what to do if you or your company gets a ransom note, like this one from the well-known GandCrab ransomware, “We are regret, but all your files was encrypted.”
“You wake up at 8:00 a.m. Someone calls you, says, ‘Man, we’ve been hit by ransomware.’ Alright, follow A-B-C on the checklist,” Kujawa said.
For example, researchers have found ways to decrypt, or unscramble, data hit by some types of ransomware.
You can check NoMoreRansom to find out if the malware holding your computer hostage has a solution.
“It doesn’t mean you have to live in constant fear,” he said. “It means you’re ready in case the worst thing happens.”
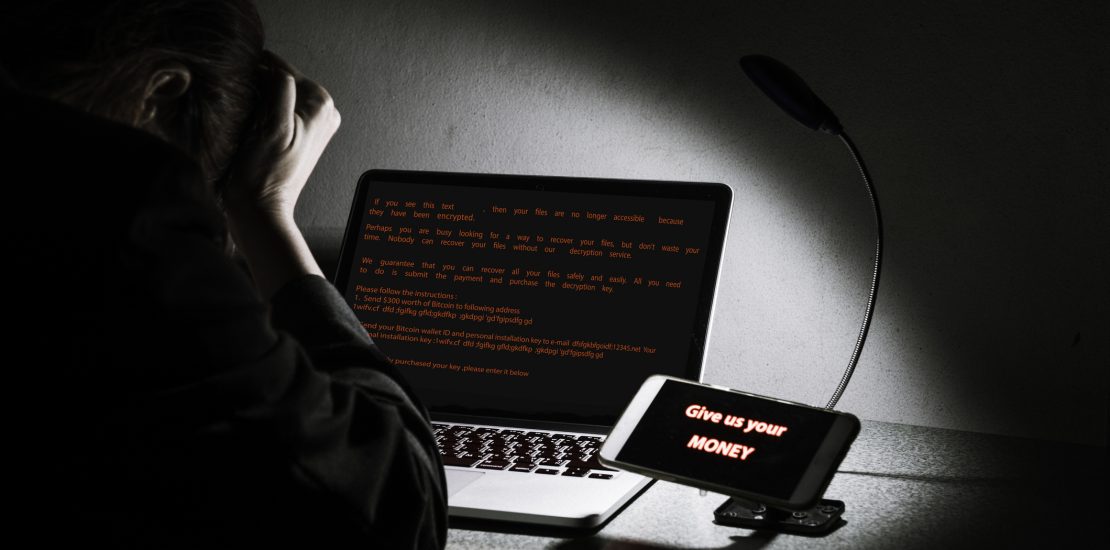
Main image: Representation of a ransomware attack. Image: mkitina4/iStock
