Catch of the Week — December
- December 3, 2020
- Posted by:
- Categories: Archer News, Cyber Crime, Cyber Crime, Cyberattack, Cyberattack, Posts with image

Chances are you’re not seeing your friends and family as much as you’re used to this year.
And cyber crooks think you’ll be itching to make a connection during the holidays.
If not, they’ll try to intimidate you into giving up crucial info. Here’s how.
Watch here:
Let’s Connect
You’ve got another meeting today.
You’re already ‘Zooming,’ for work, with friends and family — even with the doctor.
Attackers are hoping you’ll join this new “video conference” without checking to see who’s actually inviting, according to Bleeping Computer.
They sent out a fake meeting notice over the Thanksgiving holiday and they’re sure to do it more through December and January.
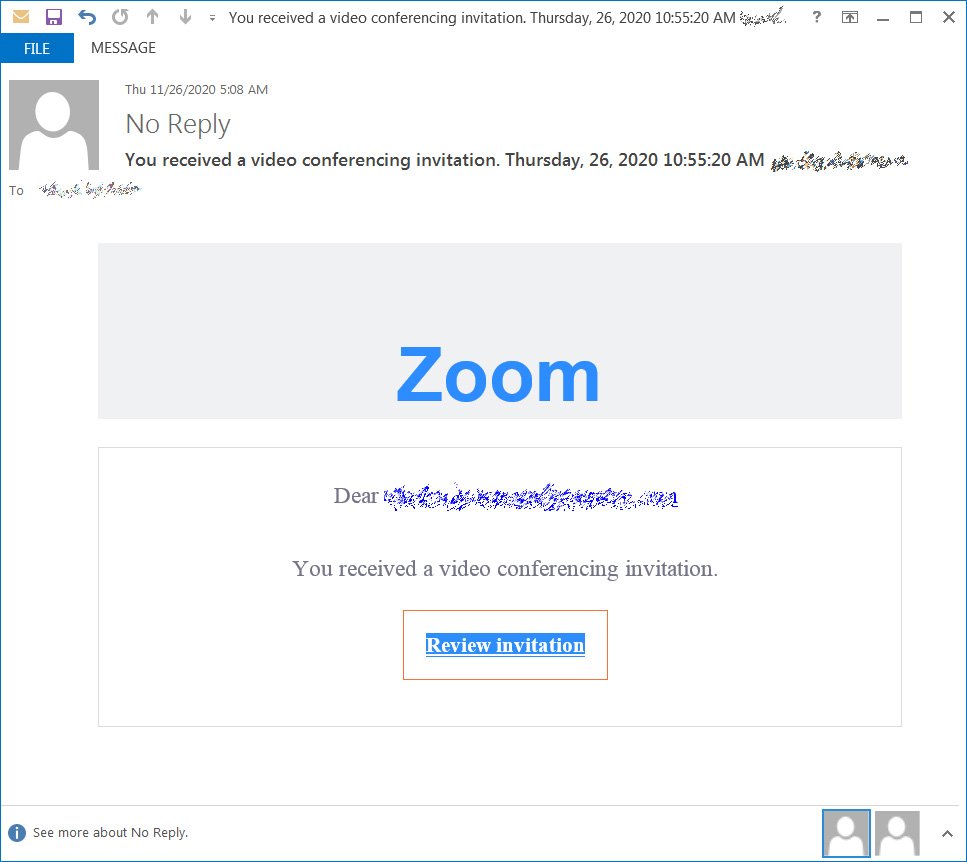
Here’s the trick: click and you go to a Microsoft login page asking for your password.
That’s not normal. Don’t do it. Normally, you click and end up directly at Zoom.
Crooks have already stolen thousands of email passwords this way, Bleeping Computer reported. They can use those credentials to take over your account, reset all of your passwords, and sell you to the highest bidder on the dark web.
Call Me Back
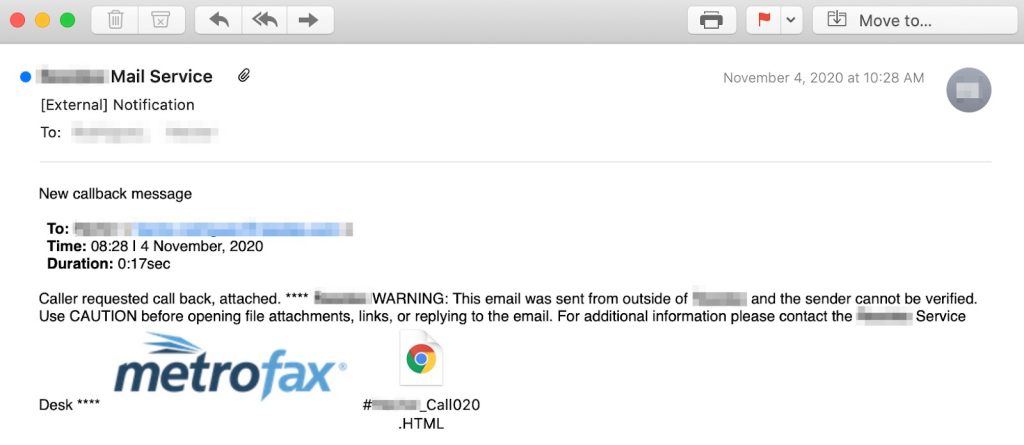
Next, you have a voice mail and the caller wants a call back.
The attachment even has your name on it, according to Abnormal Security.
Open it and you’ll see your company’s new remote work policy that you have to sign. It looks official and says scary stuff like, “Any violation of this policy may result in disciplinary action up to and including termination.”
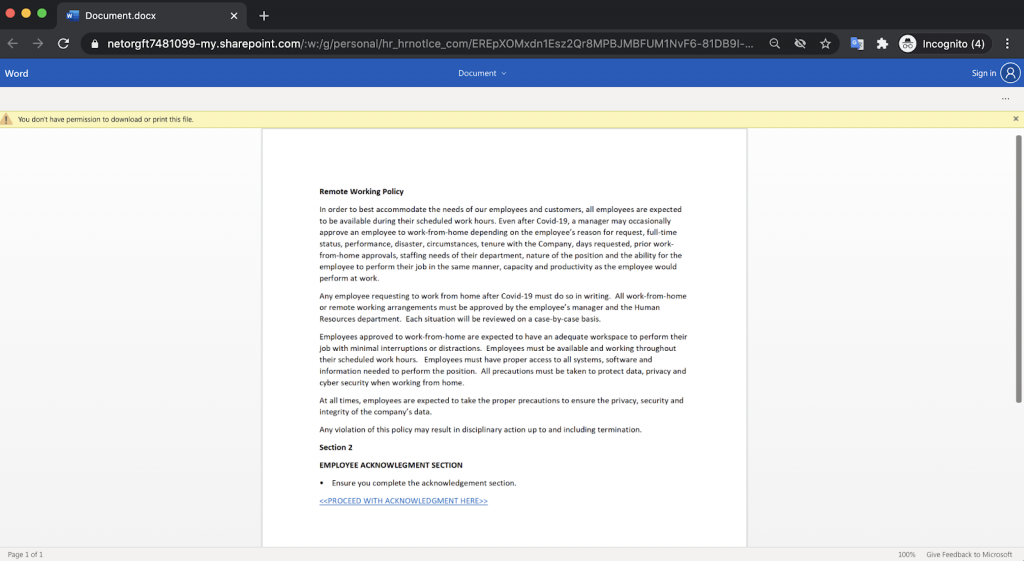
However, to sign, you have to give your email password.
As a bonus, it reads, “Never give out your password. Don’t give your personal information to someone you don’t trust.”
It’s got to be real, right?
Wrong.
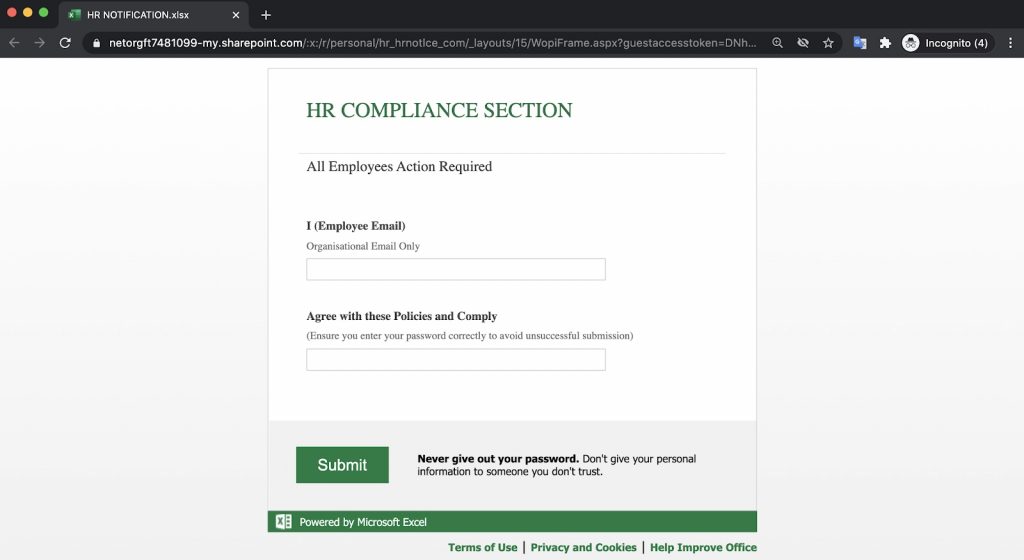
It’s a complex trick designed to steal your crucial info. Always check with your real work contacts before following through on this kind of email. They may find it annoying, but it’s better to be safe than hacked.
A side note on this phish. The sender name looks like it’s coming from your own company, but the real sender’s address is “news@newsletterverwaltung.de”, Abnormal Security said. Remember that attackers can fake the sender address, among other tricks.
See also:
Main image: School of fish. Credit: Juanmonino/iStock (modified)
