What can you learn about safety from political cyber hacking?
- May 12, 2017
- Posted by:
- Categories: Archer News, Cyber Crime, Cyberattack, Data Breach, Hacking, HVAC Security, Posts with image

A former counterintelligence operative gives insight into how to keep yourself more secure.
Eric O’Neill says he knows a thing or two about catching spies.
He worked as a “ghost” — a spy job where he collected information about his own boss at the FBI in 2001.
That boss, Robert Hanssen, was secretly selling information to Russia.
“I was always undercover,” said O’Neill, currently a national security strategist for cybersecurity company Carbon Black. “I couldn’t even tell my family what I did.”
The ordeal was made into a movie, “Breach” in 2007.
Now in 2017, O’Neill is sharing his perspectives on counterintelligence and counter terrorism.
The goal — to help you protect yourself.
“I can speak pretty well about how you can catch spies and what’s going on with our political attacks that are happening not just in the U.S. but all over,” he told the audience at the Collision tech conference in New Orleans last week.

Eric O’Neill speaks at the 2017 Collision tech conference in New Orleans. Image credit: Archer News
Who, me?
“But wait,” you may say. “I’m no spy target. I’m just a regular person. Why do I need to work about political cyber hacking, or hacking from any kind of spy at all?”
That will not protect you, O’Neill told Archer News.
Spies will go after the weakest link to find a way in, and may use you to reach a bigger target.
For example, you may be a path to your boss, who has money and information they want.
Better yet, they may be able to use your company to worm their way in to another company or government agency.
The attackers who hacked Target in 2013 reportedly got in by stealing the user name and password of an employee at an HVAC company that was working with Target.
How did they get the employee’s login credentials? With a phishing e-mail, Krebs on Security reported.

The 2013 Target hackers reportedly got in through the e-mail of an employee at an HVAC company working with Target. Photo credit: JeepersMedia via Foter.com / CC BY
Bigger goals
Political cyber hackers aren’t usually looking for credit card numbers, however.
“They want to know what we’re going to do and when we’re going to do it,” O’Neill said.
They have other goals, too.
Cyber attackers hit the Democratic National Committee in 2015 and 2016 and passed the information on to the website WikiLeaks.
They also focused on John Podesta, chair of Democratic candidate Hillary Clinton’s presidential campaign.
“He was the most ‘I’m with her’ of all the ‘I’m with hers.’ He ran the campaign,” O’Neill said. “This is the biggest target for the attackers.”

John Podesta in 2010. Photo credit: Center for American Progress via Foter.com / CC BY-ND
Fake e-mail
In March 2016, Podesta received an e-mail that looked like it was from Google.
“He does a very smart thing. He forwards it to his chief of staff and makes it her problem,” O’Neill said. “Within an hour, he has his answer from the head of IT via e-mail.”
The head of IT said the fake “Google” e-mail was legit.
Later, the head of IT said he meant to write that it was not legitimate.
But it was too late for Podesta.

An example of a Gmail phishing message. This is not the message that hooked John Podesta. Photo credit: vernieman via Foter.com / CC BY
Bait & click
“He clicks on this link on the bottom. It takes him to a spoofed Google website that looks just like the Google website,” O’Neill explained.
He enters his username and password.
“And the Russians have all his e-mail in Gmail,” O’Neill said.
“The FBI is 99% sure it was the Russians. The intelligence community is 99% sure it was the Russians. I kinda go with the intelligence community,” O’Neill added. “I’m pretty sure it was the Russians.”
If so, then they can grab power and try to destabilize the U.S.
“Their end goal is making Americans not trust one of the most important institutions we have,” O’Neill said. “If they can make us not trust those things, then they can undermine us on a world stage. And that is what the Russians want.”

John Podesta in 2010. Photo credit: Center for American Progress via Foter.com / CC BY-ND
Other countries
The U.S. is not the only country under political cyber attack.
“They used Ukraine as a test bed,” O’Neill said. “And they were extremely effective. E-mails that get somebody of power to click on a link.”
“They went after [President-elect Emmanuel] Macron in France,” he continued.
“They went after the Germans,” he said. “Undermining the Germans’ belief in their own democracy and process.”
“To know what decisions a leader of a country a person of power is going to make before they make them is power,” O’Neill said. “If knowledge is power, and the Russians can steal that information by cyber attacks, then they can take that power.”

Political and other posters on the street in Ukraine during the May 2014 elections. Photo credit: Congress of local and regional authorities via Foter.com / CC BY-ND
Your takeaway
What can you learn from all this, no matter who is behind it and what their goals are?
For one, don’t use Gmail for sensitive information like Podesta did, according to O’Neill.
Do use two-factor authentication for your accounts, like a code that is sent to you on your phone so a bad guy can’t just steal your password and get in.
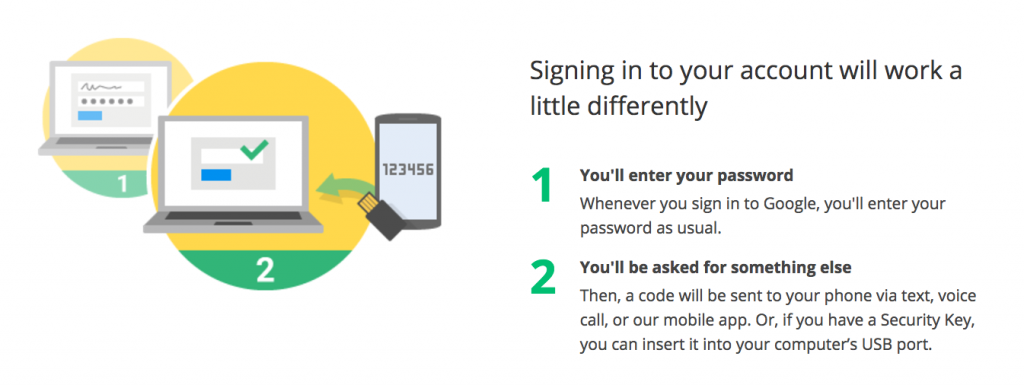
Google’s explanation of how two-factor authentication works. Image credit: Google
If you have a business, make sure your employees are trained in things like e-mail security.
You need to protect your own business with security steps like encrypting data and making back-ups, and also check to see that other companies you’re working with are doing the same.
“See if they have cyber attack insurance. What is their back-up solution? What’s going to happen to your data?” O’Neill asked.
Also, remember that attackers will use the information you put on social media against you to create very realistic phishing e-mails.
“We all live in a reality show and we’ve forgotten the cameras are rolling,” he said. “We’re like that in social media.”
Main image: U.S. capitol building. Photo credit: Douglas_Simkin via Foter.com / CC BY-ND
